Cyber Security
- Cyber Security

The contemporary digital battlefield is undergoing a fundamental transformation where state-sponsored intelligence agencies increasingly discard their formal military identities to adopt the digital masks of common cybercriminals. This strategic pivot marks a departure from traditional overt data theft toward calculated
- Cyber Security

The contemporary digital battlefield is undergoing a fundamental transformation where state-sponsored intelligence agencies increasingly discard their formal military identities to adopt the digital masks of common cybercriminals. This strategic pivot marks a departure from traditional overt data theft toward calculated
Popular Stories
- Cyber Security

The recent confirmation of a sophisticated network intrusion at Medtronic has sent ripples through the medical technology sector, highlighting the persistent vulnerability of critical healthcare infrastructure in an increasingly digital world. This specific incident came to light after the notorious
Deeper Sections Await
- Cyber Security

As digital threats against the nation’s most essential services grow increasingly sophisticated and interconnected, the need for a unified and actionable cybersecurity framework has never been more acute. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has responded to this
- Cyber Security

A silent but potent vulnerability within the very fabric of the Windows operating system has been discovered, granting attackers the ability to seize complete control over affected systems with alarming ease. Identified as CVE-2025-55681, this high-severity flaw resides in the
Browse Different Divisions
- Cyber Security

As digital threats against the nation’s most essential services grow increasingly sophisticated and interconnected, the need for a unified and actionable cybersecurity framework has never been more acute. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has responded to this
- Cyber Security
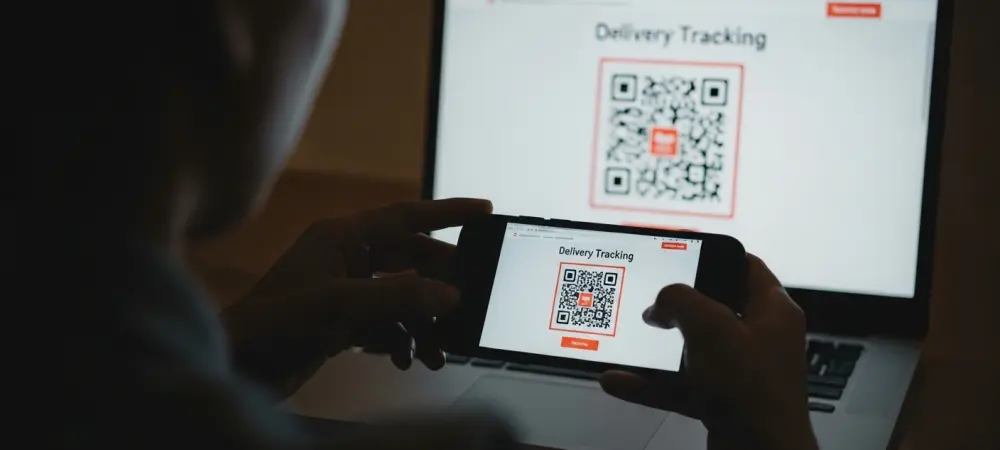
The ubiquitous black-and-white squares of QR codes, once symbols of convenient access to information, have been insidiously repurposed into a potent delivery mechanism for sophisticated cyberattacks. The use of weaponized QR codes in mobile malware campaigns represents a significant evolution
- Cyber Security
The trust inherent in academic collaboration has been dangerously weaponized in a new wave of cyber espionage, where the intellectual capital of scholars is now the primary target for state-sponsored threat actors. A sophisticated campaign uncovered in October 2025 demonstrates
- Cyber Security
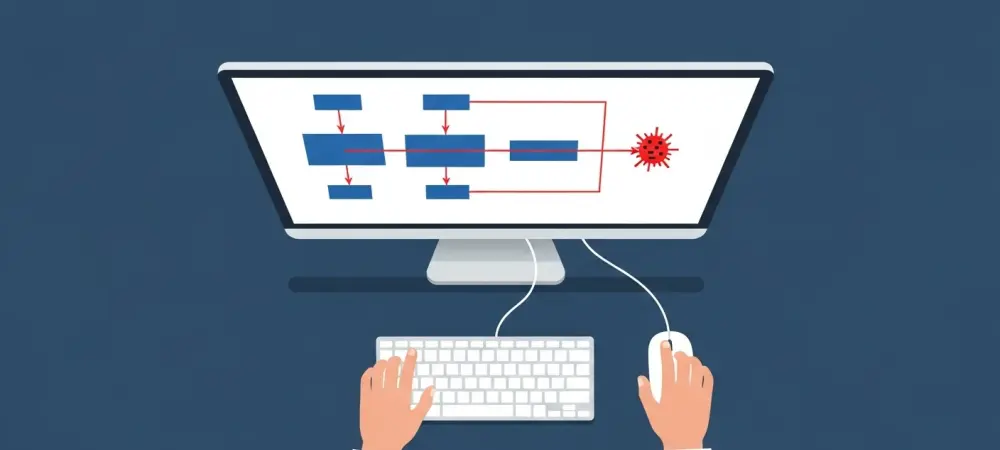
In the high-stakes world of cybersecurity, every second counts. For the analysts on the front lines in a Security Operations Center (SOC), the time between an initial alert and a final verdict is a critical window where a minor threat
- Cyber Security
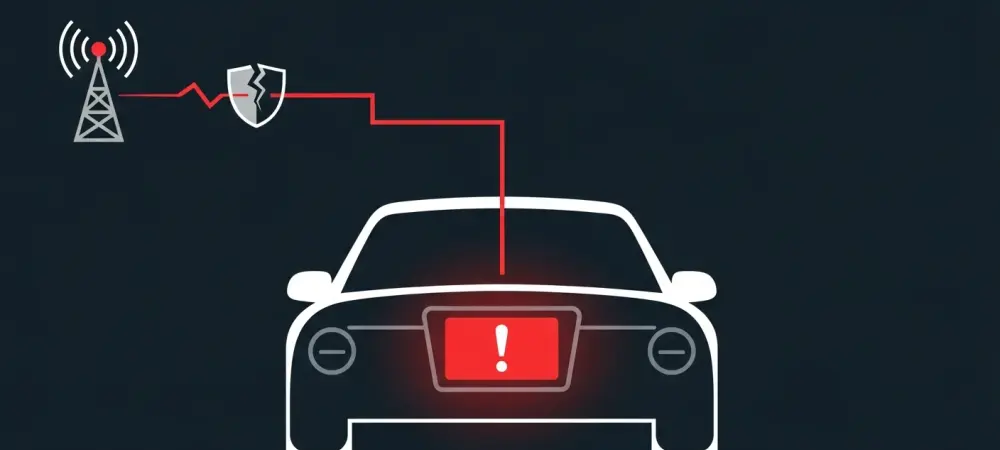
A recently uncovered security vulnerability in a widely used automotive component has transformed theoretical concerns into a tangible reality, demonstrating how hackers can remotely seize complete control of a vehicle’s dashboard infotainment system. This discovery serves as a stark reminder
- Cyber Security

A silent but potent vulnerability within the very fabric of the Windows operating system has been discovered, granting attackers the ability to seize complete control over affected systems with alarming ease. Identified as CVE-2025-55681, this high-severity flaw resides in the
Browse Different Divisions
Popular Stories
Uncover What’s Next
















