Cyber Security
- Cyber Security

Beyond the headlines of conventional warfare, a persistent and clandestine conflict is unfolding across global networks, where nations deploy sophisticated digital operatives to harvest intelligence and secure geopolitical dominance. This escalating shadow war in cyberspace poses a direct and formidable
- Cyber Security

Beyond the headlines of conventional warfare, a persistent and clandestine conflict is unfolding across global networks, where nations deploy sophisticated digital operatives to harvest intelligence and secure geopolitical dominance. This escalating shadow war in cyberspace poses a direct and formidable
Popular Stories
- Cyber Security

The cybersecurity industry’s relentless pursuit of artificial intelligence and next-generation defenses often overshadows a stark and inconvenient truth: the most damaging breaches still exploit the most elementary security gaps. In an increasingly chaotic and complex threat landscape, a significant strategic
Deeper Sections Await
- Cyber Security

The implicit trust users place in automatic software updates was profoundly shaken when developers of the popular text editor Notepad++ disclosed a critical security breach affecting their update infrastructure on February 2, 2026. This incident highlights a growing and dangerous
- Cyber Security

Today we’re joined by Dominic Jainy, an IT professional with deep expertise in artificial intelligence and blockchain, to dissect two alarming vulnerabilities recently discovered in n8n, a widely used open-source AI workflow platform. These critical flaws, rated 10.0 on the
Browse Different Divisions
- Cyber Security

The implicit trust users place in automatic software updates was profoundly shaken when developers of the popular text editor Notepad++ disclosed a critical security breach affecting their update infrastructure on February 2, 2026. This incident highlights a growing and dangerous
- Cyber Security

The very tools designed to accelerate innovation and collaboration can sometimes become gateways for malicious actors, turning trusted infrastructure into a launchpad for internal attacks. In the fast-paced world of software development, a vulnerability in a core platform like GitLab
- Cyber Security

The time it takes to brew a fresh cup of coffee is now longer than the time a motivated, AI-equipped adversary needs to find a weakness, escalate privileges, and seize complete administrative control of a corporate cloud environment. This is
- Cyber Security

A detailed forensic analysis has unveiled the sprawling and previously underestimated infrastructure of a cybercriminal group known as ShadowSyndicate, linking dozens of malicious servers through a rare and consistent operational security flaw. Researchers have capitalized on the group’s unusual habit
- Cyber Security
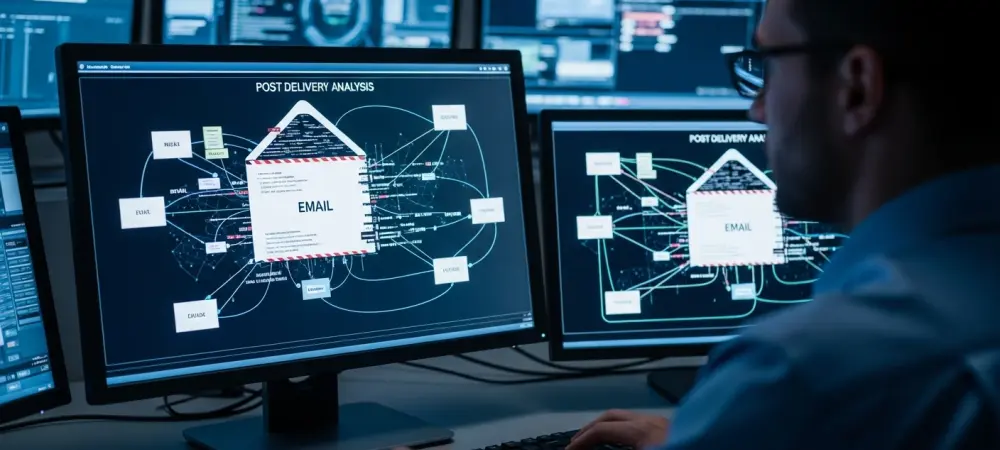
The relentless hum of digital communication now carries a threat that evolves faster than many defenses can adapt, with malicious emails arriving in inboxes at a rate that has more than doubled over the past year. This dramatic escalation is
- Cyber Security

Today we’re joined by Dominic Jainy, an IT professional with deep expertise in artificial intelligence and blockchain, to dissect two alarming vulnerabilities recently discovered in n8n, a widely used open-source AI workflow platform. These critical flaws, rated 10.0 on the
Browse Different Divisions
Popular Stories
Uncover What’s Next