Cyber Security
- Cyber Security

The contemporary digital battlefield is undergoing a fundamental transformation where state-sponsored intelligence agencies increasingly discard their formal military identities to adopt the digital masks of common cybercriminals. This strategic pivot marks a departure from traditional overt data theft toward calculated
- Cyber Security

The contemporary digital battlefield is undergoing a fundamental transformation where state-sponsored intelligence agencies increasingly discard their formal military identities to adopt the digital masks of common cybercriminals. This strategic pivot marks a departure from traditional overt data theft toward calculated
Popular Stories
- Cyber Security

The rapid integration of messaging platforms into the global financial ecosystem has created a fertile breeding ground for highly organized criminal networks that exploit the inherent trust users place in familiar digital interfaces. In early 2026, cybersecurity researchers identified a
Deeper Sections Await
- Cyber Security

Introduction In an era where digital privacy faces constant threats, with millions of credentials exposed in data breaches each year, securing personal communications has never been more critical, and WhatsApp, a messaging platform relied upon by over 3 billion users
- Cyber Security
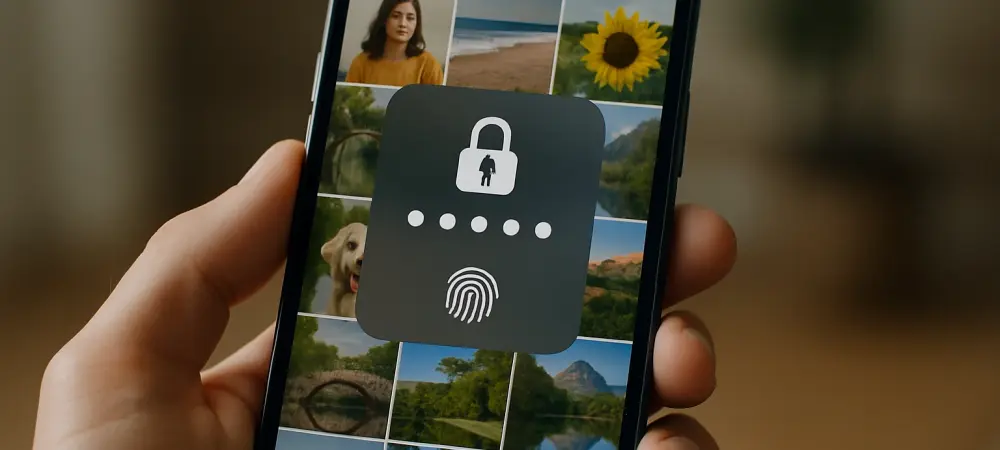
Imagine a scenario where a thief snatches a smartphone, not just for the device itself, but for the goldmine of personal data stored within the photo album—screenshots of passwords, bank statements, and even identification documents like passports or driver’s licenses.
Browse Different Divisions
- Cyber Security

Introduction In an era where digital privacy faces constant threats, with millions of credentials exposed in data breaches each year, securing personal communications has never been more critical, and WhatsApp, a messaging platform relied upon by over 3 billion users
- Cyber Security

The cybersecurity world is grappling with a staggering statistic: over 60% of new malware strains detected this year incorporate some form of artificial intelligence to enhance their destructive potential, signaling a seismic shift in how cyber threats are crafted and
- Cyber Security
In the fast-paced world of mobile app development, millions of developers rely on tools like React Native CLI to craft seamless cross-platform applications. Yet, lurking beneath this trusted toolkit lies a chilling vulnerability—a flaw so severe that it could allow
- Cyber Security

What does it mean when 42 million downloads of malicious apps infiltrate a platform as widely trusted as Google Play, exposing countless Android users to hidden cyber threats? This staggering figure isn’t just a number—it’s a stark reminder of the
- Cyber Security
Introduction In an era where connectivity is almost as essential as breathing, the convenience of public Wi-Fi at airports, coffee shops, and hotels often feels like a lifesaver for staying online. However, a startling advisory from Google has cast a
- Cyber Security
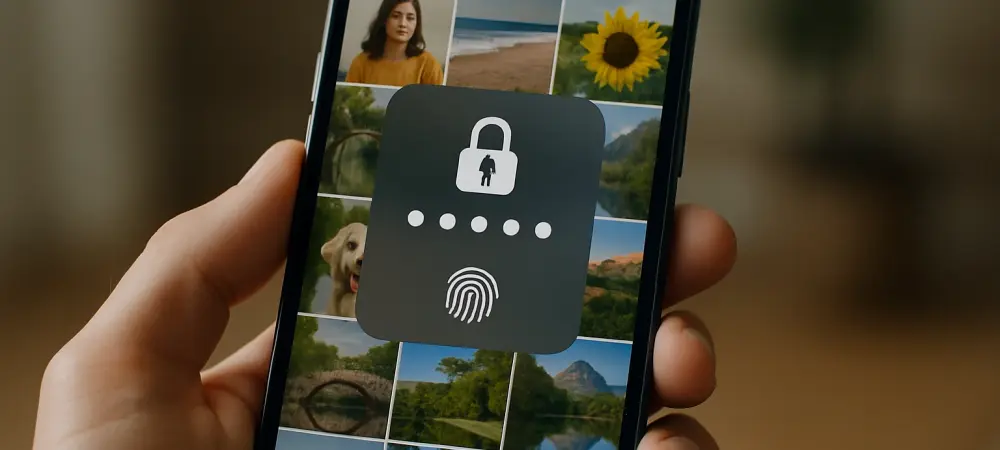
Imagine a scenario where a thief snatches a smartphone, not just for the device itself, but for the goldmine of personal data stored within the photo album—screenshots of passwords, bank statements, and even identification documents like passports or driver’s licenses.
Browse Different Divisions
Popular Stories
Uncover What’s Next
















