Cyber Security
- Cyber Security

The contemporary digital battlefield is undergoing a fundamental transformation where state-sponsored intelligence agencies increasingly discard their formal military identities to adopt the digital masks of common cybercriminals. This strategic pivot marks a departure from traditional overt data theft toward calculated
- Cyber Security

The contemporary digital battlefield is undergoing a fundamental transformation where state-sponsored intelligence agencies increasingly discard their formal military identities to adopt the digital masks of common cybercriminals. This strategic pivot marks a departure from traditional overt data theft toward calculated
Popular Stories
- Cyber Security

The rapid integration of messaging platforms into the global financial ecosystem has created a fertile breeding ground for highly organized criminal networks that exploit the inherent trust users place in familiar digital interfaces. In early 2026, cybersecurity researchers identified a
Deeper Sections Await
- Cyber Security

Imagine downloading a seemingly innocent game or utility app, only to discover later that it’s been silently tracking your every move, recording conversations, or snapping photos without consent. This unsettling reality of spyware lurking in mobile devices has sparked widespread
- Cyber Security

Imagine a critical digital infrastructure, relied upon by countless businesses for seamless connectivity, suddenly becoming a gateway for malicious actors to steal sensitive information. This alarming scenario unfolded recently for Eurofiber France, a leading telecommunications and cloud infrastructure provider, when
Browse Different Divisions
- Cyber Security

Imagine downloading a seemingly innocent game or utility app, only to discover later that it’s been silently tracking your every move, recording conversations, or snapping photos without consent. This unsettling reality of spyware lurking in mobile devices has sparked widespread
- Cyber Security

In the ever-evolving world of cybersecurity, few debates capture attention quite like the recent clash between Perplexity and SquareX over the alleged vulnerabilities in Perplexity’s Comet browser. To unpack this controversy, I sat down with Dominic Jainy, an IT professional
- Cyber Security

Paige Williams sits down with Dominic Jainy, an IT professional working at the intersection of AI, machine learning, and blockchain, who has been deeply embedded with SOC teams wrestling with real-world threats. Drawing on hands-on work operationalizing behavior-driven intelligence and
- Cyber Security
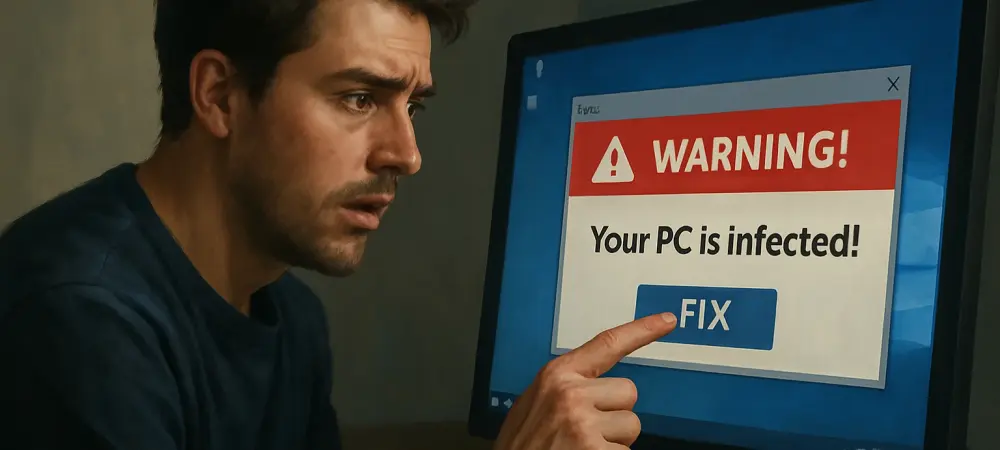
Introduction A sudden prompt telling you to open Windows Run and paste a cryptic command is not help, it is a trap that blends a dusty network utility with glossy web lures to make you do the attacker’s work. This
- Cyber Security

A Market Hungry for Speed Meets a New Underwriting Playbook Brokers still chasing screenshots and static questionnaires to place mid-market cyber coverage face an awkward truth: the cloud moved on, but much of underwriting did not, and that gap slows
- Cyber Security

Imagine a critical digital infrastructure, relied upon by countless businesses for seamless connectivity, suddenly becoming a gateway for malicious actors to steal sensitive information. This alarming scenario unfolded recently for Eurofiber France, a leading telecommunications and cloud infrastructure provider, when
Browse Different Divisions
Popular Stories
Uncover What’s Next
















