Cyber Security
- Cyber Security

The contemporary digital battlefield is undergoing a fundamental transformation where state-sponsored intelligence agencies increasingly discard their formal military identities to adopt the digital masks of common cybercriminals. This strategic pivot marks a departure from traditional overt data theft toward calculated
- Cyber Security

The contemporary digital battlefield is undergoing a fundamental transformation where state-sponsored intelligence agencies increasingly discard their formal military identities to adopt the digital masks of common cybercriminals. This strategic pivot marks a departure from traditional overt data theft toward calculated
Popular Stories
- Cyber Security

The recent confirmation of a sophisticated network intrusion at Medtronic has sent ripples through the medical technology sector, highlighting the persistent vulnerability of critical healthcare infrastructure in an increasingly digital world. This specific incident came to light after the notorious
Deeper Sections Await
- Cyber Security

With a deep background in applying advanced technologies like artificial intelligence and blockchain to solve complex security challenges, Dominic Jainy has become a leading voice in the discussion around supply chain integrity. We sat down with him to dissect the
- Cyber Security
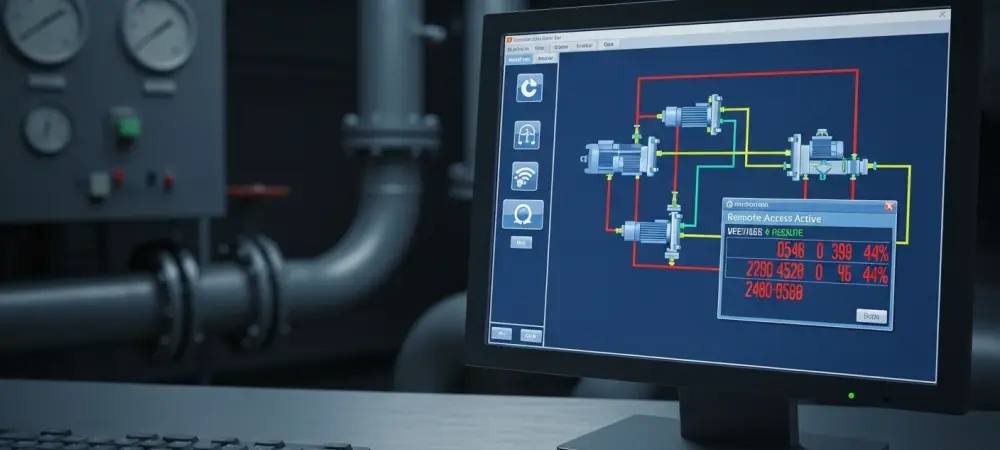
A seemingly innocuous control panel in a small American town, responsible for managing the flow of clean water to thousands of homes, flickers as an unauthorized user gains access from halfway across the world, not through a sophisticated exploit but
Browse Different Divisions
- Cyber Security

With a deep background in applying advanced technologies like artificial intelligence and blockchain to solve complex security challenges, Dominic Jainy has become a leading voice in the discussion around supply chain integrity. We sat down with him to dissect the
- Cyber Security

A detailed analysis of the widespread exploitation of the React2Shell vulnerability reveals a dynamic and escalating threat landscape, where a diverse array of threat actors are leveraging the critical flaw to deploy cryptocurrency miners and several newly discovered malware families
- Cyber Security
In a world where artificial intelligence is rapidly becoming an indispensable co-pilot for developers, the very tools designed to accelerate innovation are introducing novel security risks. We’re seeing a new class of vulnerabilities emerge not in the code itself, but
- Cyber Security

A recently uncovered chain of five critical vulnerabilities in Fluent Bit, an open-source logging agent with over 15 billion deployments, has created a cascading security risk threatening the stability and integrity of the global cloud ecosystem. This widely adopted tool
- Cyber Security

Australian organizations are investing in cloud security at an unprecedented rate, yet they simultaneously face some of the most severe and costly cyber incidents on the global stage, revealing a dangerous disconnect between confidence and capability. This industry report dissects
- Cyber Security
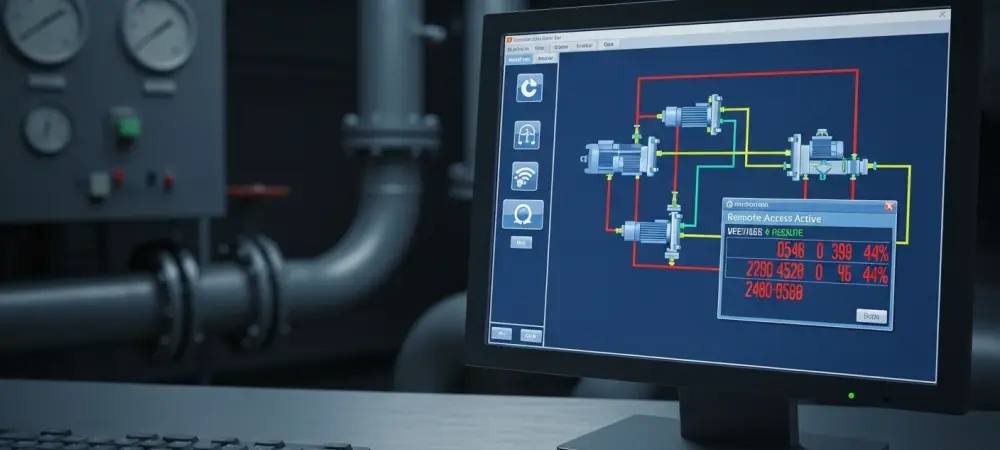
A seemingly innocuous control panel in a small American town, responsible for managing the flow of clean water to thousands of homes, flickers as an unauthorized user gains access from halfway across the world, not through a sophisticated exploit but
Browse Different Divisions
Popular Stories
Uncover What’s Next

















