Cyber Security
- Cyber Security

The contemporary digital battlefield is undergoing a fundamental transformation where state-sponsored intelligence agencies increasingly discard their formal military identities to adopt the digital masks of common cybercriminals. This strategic pivot marks a departure from traditional overt data theft toward calculated
- Cyber Security

The contemporary digital battlefield is undergoing a fundamental transformation where state-sponsored intelligence agencies increasingly discard their formal military identities to adopt the digital masks of common cybercriminals. This strategic pivot marks a departure from traditional overt data theft toward calculated
Popular Stories
- Cyber Security

The recent confirmation of a sophisticated network intrusion at Medtronic has sent ripples through the medical technology sector, highlighting the persistent vulnerability of critical healthcare infrastructure in an increasingly digital world. This specific incident came to light after the notorious
Deeper Sections Await
- Cyber Security

While enterprise security teams were winding down for the Christmas holiday, a sophisticated threat actor launched an expansive automated campaign, unleashing over 2.5 million malicious requests against a wide array of web applications worldwide. The operation, characterized by its scale
- Cyber Security
The code you did not write is now your biggest security threat, as in an interconnected digital ecosystem, attackers have shifted their focus from direct assault to insidious infiltration, compromising the very building blocks of modern software and fundamentally eroding
Browse Different Divisions
- Cyber Security

While enterprise security teams were winding down for the Christmas holiday, a sophisticated threat actor launched an expansive automated campaign, unleashing over 2.5 million malicious requests against a wide array of web applications worldwide. The operation, characterized by its scale
- Cyber Security

The very headphones designed to deliver private audio experiences to millions of users worldwide have been found to contain a critical flaw that can turn them into a gateway for hijacking connected smartphones. A groundbreaking investigation has uncovered a series
- Cyber Security
The common narrative surrounding cybercrime often portrays threat actors as ghost-like figures, executing flawless, automated campaigns that bypass defenses with surgical precision, but a detailed examination of the digital residue left behind on compromised systems paints a dramatically different and
- Cyber Security
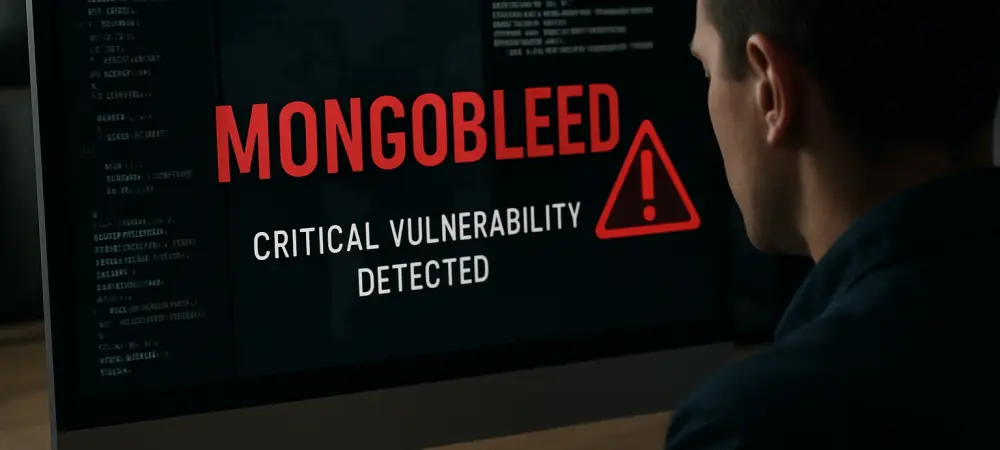
The very memory that powers modern databases can sometimes become an unintentional treasure trove for attackers, silently exposing an organization’s most sensitive secrets to the outside world. A recently discovered vulnerability, known as MongoBleed, brings this abstract threat into sharp
- Cyber Security

A recently disclosed vulnerability in MongoDB, a database technology central to countless modern applications, is now being actively exploited in the wild, placing an estimated 87,000 servers worldwide at immediate risk of significant data exposure. This critical flaw, tracked as
- Cyber Security
The code you did not write is now your biggest security threat, as in an interconnected digital ecosystem, attackers have shifted their focus from direct assault to insidious infiltration, compromising the very building blocks of modern software and fundamentally eroding
Browse Different Divisions
Popular Stories
Uncover What’s Next
















