Cyber Security
- Cyber Security

The transition from traditional, human-orchestrated digital intrusions toward a more volatile era of generative exploitation has fundamentally rewritten the global cybersecurity playbook within the last few months. As specialized frontier models demonstrate an unprecedented ability to perform complex offensive tasks
- Cyber Security

The transition from traditional, human-orchestrated digital intrusions toward a more volatile era of generative exploitation has fundamentally rewritten the global cybersecurity playbook within the last few months. As specialized frontier models demonstrate an unprecedented ability to perform complex offensive tasks
Popular Stories
- Cyber Security

The sudden realization that sensitive biometric information and national identity numbers are being traded in clandestine digital marketplaces for less than the cost of a bottled soda has forced a dramatic reevaluation of Nigeria’s digital security protocols. As the nation
Deeper Sections Await
- Cyber Security

The rapid evolution of digital finance in South Korea has necessitated a groundbreaking alliance between the National Police Agency and the country’s leading cryptocurrency exchanges to combat the sophisticated rise of voice-phishing and financial fraud. This collaboration involves the five
- Cyber Security

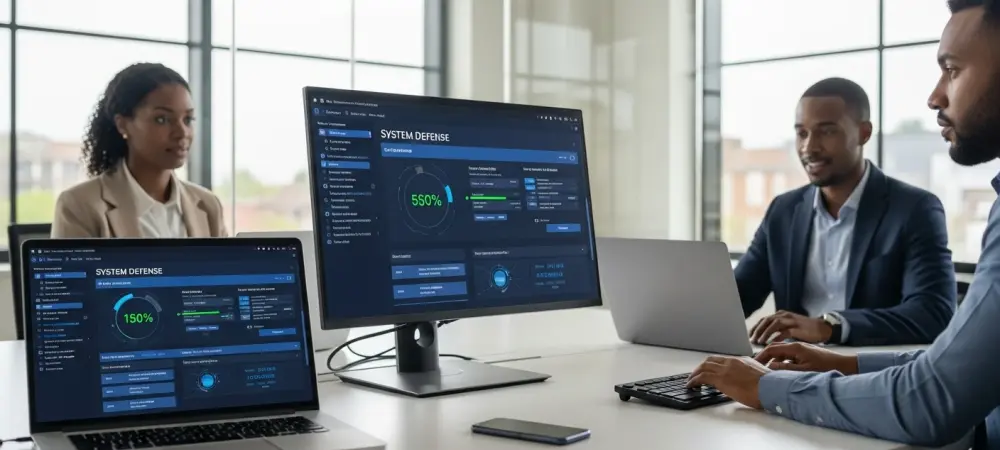
Introduction The recent decision by the Cybersecurity and Infrastructure Security Agency to include a critical Palo Alto Networks vulnerability in its catalog of known exploited flaws signals a major shift in the threat landscape. This development centers on CVE-2026-0257, a
Browse Different Divisions
- Cyber Security

The rapid evolution of digital finance in South Korea has necessitated a groundbreaking alliance between the National Police Agency and the country’s leading cryptocurrency exchanges to combat the sophisticated rise of voice-phishing and financial fraud. This collaboration involves the five
- Cyber Security

A single unauthorized login at three o’clock in the morning can trigger a sequence of events that paralyzes global operations and compromises millions of sensitive customer records within minutes. In this high-stakes environment, the distinction between a managed incident and
- Cyber Security
Dominic Jainy is a seasoned IT professional with a deep specialization in artificial intelligence, machine learning, and blockchain architectures. His work frequently explores the intersection of these emerging technologies, focusing on how to build robust, scalable systems while navigating the
- Cyber Security
The modern digital landscape of 2026 presents a reality where a single sophisticated ransomware strain can paralyze a global enterprise in less than fifteen minutes without warning. While traditional cybersecurity training often relies on static modules or predictable tabletop exercises,
- Cyber Security

The modern smartphone has evolved into a double-edged sword that provides unparalleled convenience while simultaneously serving as a high-fidelity listening device for foreign intelligence services. A high-ranking official enters a secure briefing room, leaving their smartphone at the door, yet
- Cyber Security

Introduction The recent decision by the Cybersecurity and Infrastructure Security Agency to include a critical Palo Alto Networks vulnerability in its catalog of known exploited flaws signals a major shift in the threat landscape. This development centers on CVE-2026-0257, a
Browse Different Divisions
Popular Stories
Uncover What’s Next