Cyber Security
- Cyber Security

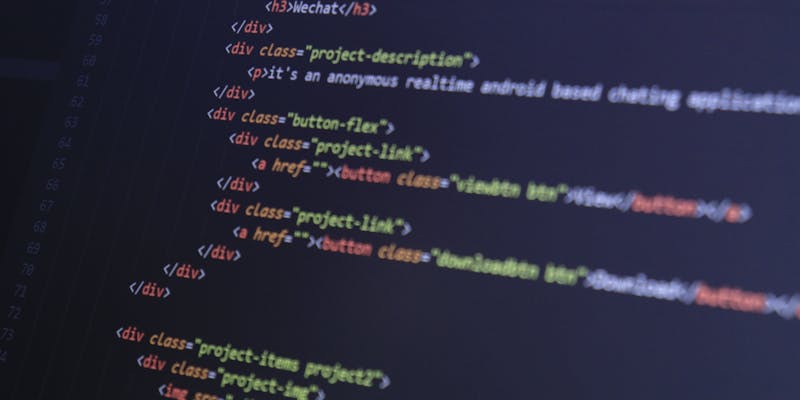
The recent confirmation of a sophisticated network intrusion at Medtronic has sent ripples through the medical technology sector, highlighting the persistent vulnerability of critical healthcare infrastructure in an increasingly digital world. This specific incident came to light after the notorious
- Cyber Security

The recent confirmation of a sophisticated network intrusion at Medtronic has sent ripples through the medical technology sector, highlighting the persistent vulnerability of critical healthcare infrastructure in an increasingly digital world. This specific incident came to light after the notorious
Popular Stories
- Cyber Security

The recent confirmation of a sophisticated network intrusion at Medtronic has sent ripples through the medical technology sector, highlighting the persistent vulnerability of critical healthcare infrastructure in an increasingly digital world. This specific incident came to light after the notorious
Deeper Sections Await
- Cyber Security

The modern battlefield has shifted from physical borders to the intricate digital networks that regulate the water we drink and the electricity powering our homes. While traditional warfare often involves visible movements of troops and hardware, the current digital age
- Cyber Security

The silent operation of a power grid or water treatment facility often masks a terrifying technical debt that is rapidly becoming a liability in the face of quantum computing advancements. As 2026 progresses, the push for cryptographic readiness has moved
Browse Different Divisions
- Cyber Security

The modern battlefield has shifted from physical borders to the intricate digital networks that regulate the water we drink and the electricity powering our homes. While traditional warfare often involves visible movements of troops and hardware, the current digital age
- Cyber Security

The digital world has finally crossed a threshold where the average lifespan of a software vulnerability is no longer measured in months of quiet research but in hours of frantic, automated exploitation. In this current climate, the traditional “cat-and-mouse” game
- Cyber Security

Dominic Jainy is a seasoned IT professional whose work sits at the intersection of emerging technologies and network security. With a deep understanding of how state-sponsored actors exploit the very hardware that powers our home offices, Jainy provides a unique
- Cyber Security

The vulnerability of the American electrical grid and water distribution systems has reached a critical juncture as state-sponsored actors refine their ability to manipulate the hardware governing our most basic daily necessities. Recent reports from the Cybersecurity and Infrastructure Security
- Cyber Security

Dominic Jainy is a seasoned IT professional whose expertise sits at the intersection of artificial intelligence, machine learning, and blockchain technology. With a career dedicated to understanding how complex systems can be both leveraged for innovation and exploited by malicious
- Cyber Security

The silent operation of a power grid or water treatment facility often masks a terrifying technical debt that is rapidly becoming a liability in the face of quantum computing advancements. As 2026 progresses, the push for cryptographic readiness has moved
Browse Different Divisions
Popular Stories
Uncover What’s Next