Unmasking the Threat of Synthetic Identities
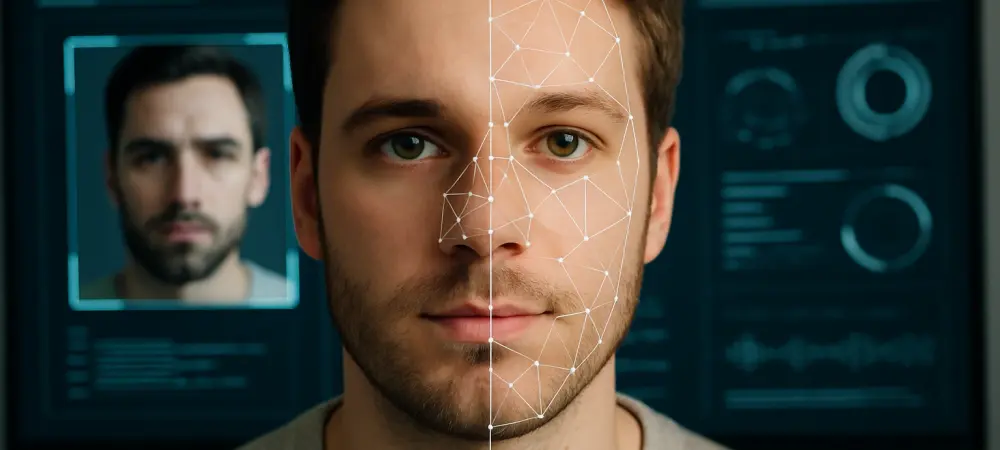
Imagine a scenario where a criminal seamlessly blends the facial features of two individuals into a single, synthetic image, bypassing even the most sophisticated facial recognition systems at a border checkpoint. This is not a plot from a futuristic thriller but a real-world challenge posed by face morphing technology, a subset of deepfake innovation that threatens identity security. With critical applications like passport issuance and border control at stake, the ability to detect these manipulated images has become a pressing priority for global security agencies.
The rapid evolution of face morphing has exposed vulnerabilities in systems designed to protect against identity fraud. As threat actors exploit this technology to create images that can deceive automated verification processes, the need for robust detection mechanisms has never been more urgent. This review delves into the intricacies of face morphing detection, analyzing its key approaches, performance metrics, and real-world implications for safeguarding sensitive operations.
Core Features and Methodologies of Detection Systems
Single-Image Morph Attack Detection
At the forefront of face morphing countermeasures is single-image morph attack detection, a method that analyzes a suspect image in isolation to identify signs of manipulation. This approach relies heavily on machine learning models trained to recognize specific patterns or artifacts left by morphing software. When tailored to a known tool, the accuracy of this method can be remarkably high, often reaching near-perfect detection rates under controlled conditions.
However, the Achilles’ heel of single-image detection lies in its sensitivity to unfamiliar morphing tools. If the system encounters a synthetic image created by software outside its training data, performance can plummet significantly, with accuracy rates dropping to unsustainable levels. This limitation highlights the critical need for diverse and comprehensive datasets to ensure adaptability across a wide range of potential threats.
Differential Morph Attack Detection
In contrast, differential morph attack detection offers a comparative approach by evaluating a suspect image against a verified authentic one. This method achieves more stable performance, with accuracy rates consistently falling within a reliable range across various morphing techniques. Its strength lies in the ability to spot discrepancies that might be invisible in a standalone analysis.
Yet, the requirement for a genuine reference image poses a significant operational challenge. In many real-world scenarios, such as border screenings or identity checks, access to an authentic photo for comparison may not be feasible. This constraint limits the practicality of differential detection in fast-paced or resource-constrained environments, necessitating alternative strategies for deployment.
Performance Analysis and Technological Advancements
The field of face morphing detection has seen substantial progress in recent years, driven by innovations in algorithmic design and machine learning capabilities. Cutting-edge tools now incorporate advanced feature extraction techniques to identify subtle inconsistencies in facial textures or geometric alignments that betray synthetic origins. These advancements have bolstered the resilience of detection systems against increasingly sophisticated morphing methods.
Expert insights underscore the importance of integrating these technologies with operational protocols. Guidance for staff on recognizing suspicious cases has proven instrumental in preventing manipulated images from infiltrating secure systems. Moreover, ongoing research aims to bridge the gap between laboratory accuracy and real-world applicability, ensuring that detection tools remain effective under diverse conditions.
A key trend shaping this domain is the emphasis on proactive measures alongside reactive detection. By enforcing stringent policies on photo submissions for identity credentials, organizations can reduce the entry points for fraudulent images. This dual focus on technology and procedure represents a holistic approach to tackling the evolving landscape of digital identity threats.
Real-World Applications and Security Implications
Face morphing detection plays a pivotal role in high-stakes environments where identity verification is paramount. Border security agencies rely on these systems to screen travelers and prevent unauthorized access, while passport offices use them to validate applicant photographs. The ability to intercept synthetic images in these contexts is crucial for maintaining the integrity of national and international security frameworks.
Beyond governmental applications, the technology also supports routine identity verification processes in the private sector. Financial institutions and online platforms increasingly adopt morphing detection to combat fraud during account creation or transaction authentication. As digital interactions grow, the scope of this technology expands to protect against a broader spectrum of deceptive practices.
The significance of these applications is underscored by documented instances of document fraud facilitated by face morphing. Reports from European authorities have highlighted the use of synthetic images in forging identity credentials, emphasizing the urgent need for reliable countermeasures. Detection systems thus serve as a critical line of defense in preserving trust in digital and physical identity ecosystems.
Challenges Hindering Effective Deployment
Despite technological strides, face morphing detection faces notable hurdles that limit its efficacy. The dependency on training data remains a persistent issue, as systems trained on specific morphing tools struggle to generalize to novel methods employed by adversaries. This gap in adaptability poses a significant risk in an era where new software emerges rapidly.
Operational constraints further complicate the implementation of detection mechanisms. The necessity of authentic comparison images for differential analysis is often impractical in dynamic settings, while single-image methods require constant updates to training datasets to maintain relevance. These logistical barriers highlight the need for flexible solutions that can operate under varying conditions.
Regulatory and procedural challenges also play a role in hindering progress. Establishing standardized guidelines for photo submission and verification across jurisdictions is a complex endeavor, often slowed by differing priorities or resource allocations. Addressing these systemic issues will be essential to scaling detection capabilities and ensuring consistent protection against identity fraud.
Reflecting on Achievements and Charting the Path Forward
Looking back, the journey of face morphing detection technology reveals a landscape of remarkable innovation tempered by persistent challenges. The strides made in algorithmic accuracy and operational integration demonstrate a strong foundation for combating synthetic identity threats. Yet, the limitations in adaptability and practicality underscore areas where further effort is needed.
Moving forward, stakeholders should prioritize the development of adaptive algorithms capable of handling diverse morphing tools through continuous learning. Collaborative efforts between technology developers and security agencies can foster the creation of comprehensive datasets to enhance system robustness. Additionally, establishing global standards for identity verification protocols could streamline the adoption of preventive measures.
Ultimately, the fight against face morphing demands a sustained commitment to innovation and coordination. Investing in research to anticipate future deepfake tactics will be crucial, as will educating operational teams to recognize and respond to suspicious cases. By building on past successes and addressing existing gaps, the path toward fortified identity security becomes clearer and more attainable.