Cyber Security
- Cyber Security

Beyond the headlines of conventional warfare, a persistent and clandestine conflict is unfolding across global networks, where nations deploy sophisticated digital operatives to harvest intelligence and secure geopolitical dominance. This escalating shadow war in cyberspace poses a direct and formidable
- Cyber Security

Beyond the headlines of conventional warfare, a persistent and clandestine conflict is unfolding across global networks, where nations deploy sophisticated digital operatives to harvest intelligence and secure geopolitical dominance. This escalating shadow war in cyberspace poses a direct and formidable
Popular Stories
- Cyber Security

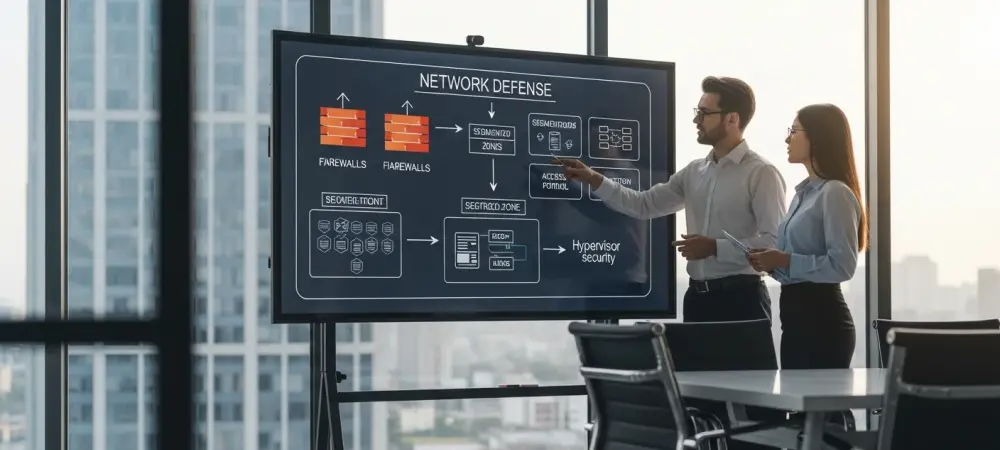
The cybersecurity industry’s relentless pursuit of artificial intelligence and next-generation defenses often overshadows a stark and inconvenient truth: the most damaging breaches still exploit the most elementary security gaps. In an increasingly chaotic and complex threat landscape, a significant strategic
Deeper Sections Await
- Cyber Security
In an era where digital espionage has become a cornerstone of state-sponsored conflict, a chilling new development has emerged from the shadows of cyber warfare, casting a spotlight on the relentless ingenuity of threat actors. A sophisticated piece of malware
- Cyber Security

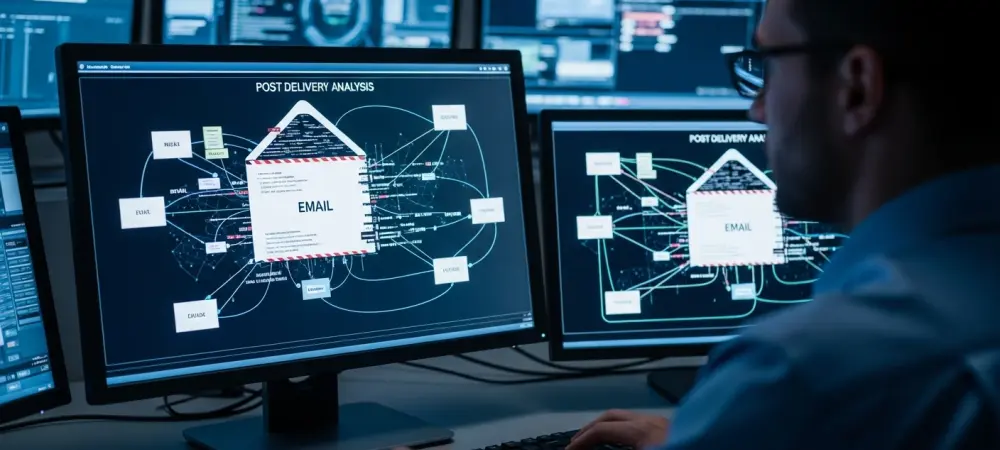
What happens when a seemingly harmless email turns into a weapon of economic destruction? South Korea is grappling with an invisible yet devastating threat from North Korea, where state-sponsored hackers are unleashing sophisticated ransomware attacks to destabilize and profit. These
Browse Different Divisions
- Cyber Security
In an era where digital espionage has become a cornerstone of state-sponsored conflict, a chilling new development has emerged from the shadows of cyber warfare, casting a spotlight on the relentless ingenuity of threat actors. A sophisticated piece of malware
- Cyber Security

Imagine scrolling through your social media feed on X, encountering a promoted post with an intriguing video, and seeing a clickable link provided by the platform’s own AI assistant, Grok. Unbeknownst to millions of users, that link could lead to
- Cyber Security

Imagine a silent digital storm sweeping across the globe, infiltrating the very backbone of critical infrastructure in over 80 countries, compromising 600 organizations without a trace until it’s too late. This is the reality of Salt Typhoon, a China-linked advanced
- Cyber Security

In an era where cybersecurity threats are evolving at an alarming pace, a new phishing-as-a-service platform known as Tycoon2FA has emerged as a formidable challenge to even the most advanced security systems, employing a meticulously crafted 7-stage process that deceives
- Cyber Security

Unveiling the Cyber Sabotage Campaign Imagine a fleet of tankers, vital to a nation’s economy, suddenly cut off from communication, drifting aimlessly in international waters with no access to weather updates or port coordination, a scenario that became reality in
- Cyber Security

What happens when a seemingly harmless email turns into a weapon of economic destruction? South Korea is grappling with an invisible yet devastating threat from North Korea, where state-sponsored hackers are unleashing sophisticated ransomware attacks to destabilize and profit. These
Browse Different Divisions
Popular Stories
Uncover What’s Next