Cyber Security
- Cyber Security

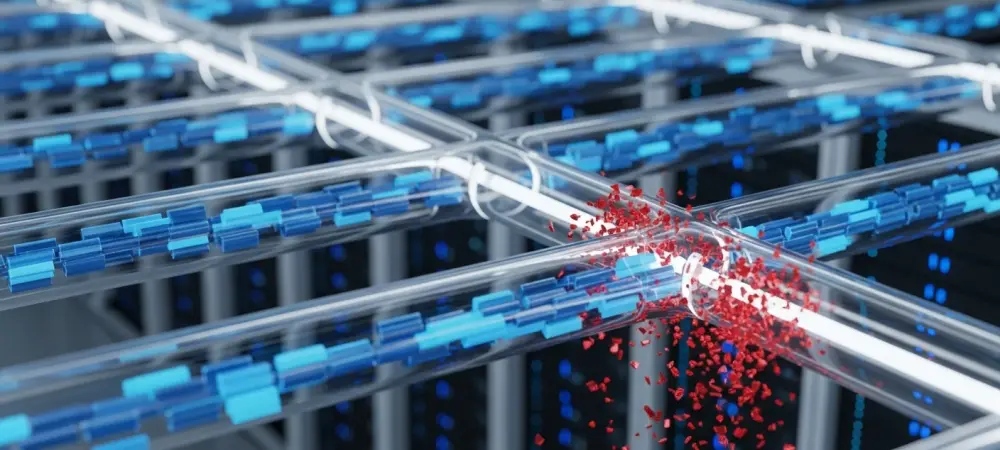
The traditional perception of state-sponsored hacking as a series of isolated operations is rapidly dissolving into a reality of highly integrated, resource-sharing networks. Security researchers have spent the last few years observing a paradigm shift where Chinese threat clusters no
- Cyber Security

The traditional perception of state-sponsored hacking as a series of isolated operations is rapidly dissolving into a reality of highly integrated, resource-sharing networks. Security researchers have spent the last few years observing a paradigm shift where Chinese threat clusters no
Popular Stories
- Cyber Security

The recent confirmation of a sophisticated network intrusion at Medtronic has sent ripples through the medical technology sector, highlighting the persistent vulnerability of critical healthcare infrastructure in an increasingly digital world. This specific incident came to light after the notorious
Deeper Sections Await
- Cyber Security

Introduction The digital key that unlocks your entire online life, your password manager’s master password, has become the prime target of a sophisticated and evolving phishing campaign aimed at LastPass users. This situation underscores a critical vulnerability in modern digital
- Cyber Security

The unsettling reality for network administrators is that a fully patched system does not always equate to a fully secure one, a lesson underscored by the persistent Fortinet SSO vulnerability. The recent Fortinet Single Sign-On (SSO) authentication bypass vulnerability represents
Browse Different Divisions
- Cyber Security

Introduction The digital key that unlocks your entire online life, your password manager’s master password, has become the prime target of a sophisticated and evolving phishing campaign aimed at LastPass users. This situation underscores a critical vulnerability in modern digital
- Cyber Security

Anticipation for the next major iPhone software release has reached a fever pitch, not merely for new aesthetic features, but for critical security and functionality enhancements that promise to reshape the daily mobile experience for millions of users globally. After
- Cyber Security

An overwhelming majority of organizations express high confidence in their ability to thwart a major cyberattack, yet this self-assurance crumbles when tested against the reality of a sophisticated, high-pressure breach. This research summary delves into a critical and widespread “readiness
- Cyber Security
With the tech world buzzing about AI and flashy updates, it’s easy to miss the quiet changes happening in the background—changes that could put millions of us at risk. To unpack this, we’re speaking with Dominic Jainy, an IT professional
- Cyber Security

An Urgent Threat to Virtualized Infrastructure A recently disclosed vulnerability in one of the most widely used enterprise virtualization platforms has rapidly escalated from a theoretical weakness into an active, weaponized threat against global networks. A critical vulnerability in VMware’s
- Cyber Security

The unsettling reality for network administrators is that a fully patched system does not always equate to a fully secure one, a lesson underscored by the persistent Fortinet SSO vulnerability. The recent Fortinet Single Sign-On (SSO) authentication bypass vulnerability represents
Browse Different Divisions
Popular Stories
Uncover What’s Next



















