Cyber Security
- Cyber Security

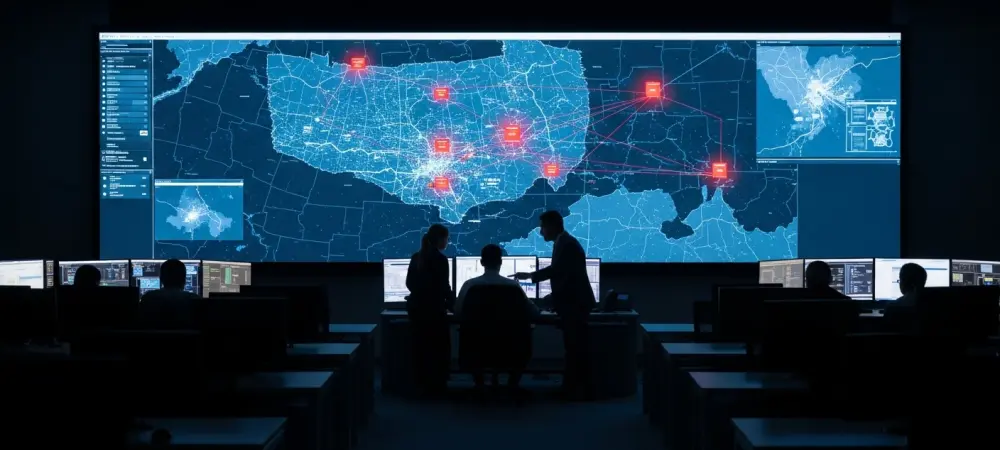
The architectural integrity of global digital infrastructure is no longer maintained by human hands alone; instead, it increasingly relies on self-healing, autonomous agents capable of neutralizing threats at machine speed. This fundamental departure from manual, reactive defense signifies a paradigm
- Cyber Security

The architectural integrity of global digital infrastructure is no longer maintained by human hands alone; instead, it increasingly relies on self-healing, autonomous agents capable of neutralizing threats at machine speed. This fundamental departure from manual, reactive defense signifies a paradigm
Popular Stories
- Cyber Security

The recent confirmation of a sophisticated network intrusion at Medtronic has sent ripples through the medical technology sector, highlighting the persistent vulnerability of critical healthcare infrastructure in an increasingly digital world. This specific incident came to light after the notorious
Deeper Sections Await
- Cyber Security

The seemingly secure digital infrastructure of a major hotel chain unraveled under the weight of a meticulously planned cyberattack, sending a clear warning across Japan’s hospitality industry that the greatest threats often arrive silently and after business hours. The Washington
- Cyber Security

A meticulously planned cyberattack against Poland’s energy infrastructure in late 2025, while ultimately thwarted, cast a long shadow over the security of critical systems worldwide, revealing a sophisticated new blueprint for disrupting modern power grids. The assault, deliberately timed to
Browse Different Divisions
- Cyber Security

The seemingly secure digital infrastructure of a major hotel chain unraveled under the weight of a meticulously planned cyberattack, sending a clear warning across Japan’s hospitality industry that the greatest threats often arrive silently and after business hours. The Washington
- Cyber Security

The convenience of built-in artificial intelligence has rapidly become an expectation in modern technology, but the European Parliament’s recent ban on these features demonstrates that this advancement comes with a significant and often hidden cost to security and data privacy.
- Cyber Security

A trusted platform for collaborative software development recently became the staging ground for a deceptive cross-platform attack, where a counterfeit repository for a legitimate macOS application was repurposed to distribute sophisticated malware targeting Windows users. This incident serves as a
- Cyber Security
While political debates surrounding a Department of Homeland Security funding lapse often fixate on physical border control, a far more insidious and potentially devastating national security crisis is quietly unfolding in the digital realm. The current fiscal stalemate is serving
- Cyber Security

Cybercriminals are continually refining their methods to bypass modern security defenses, often by repurposing legitimate system tools for malicious ends. A recent evolution in ClickFix attacks demonstrates this trend with alarming effectiveness, now employing a new command to trick users
- Cyber Security

A meticulously planned cyberattack against Poland’s energy infrastructure in late 2025, while ultimately thwarted, cast a long shadow over the security of critical systems worldwide, revealing a sophisticated new blueprint for disrupting modern power grids. The assault, deliberately timed to
Browse Different Divisions
Popular Stories
Uncover What’s Next

















