Cyber Security
- Cyber Security

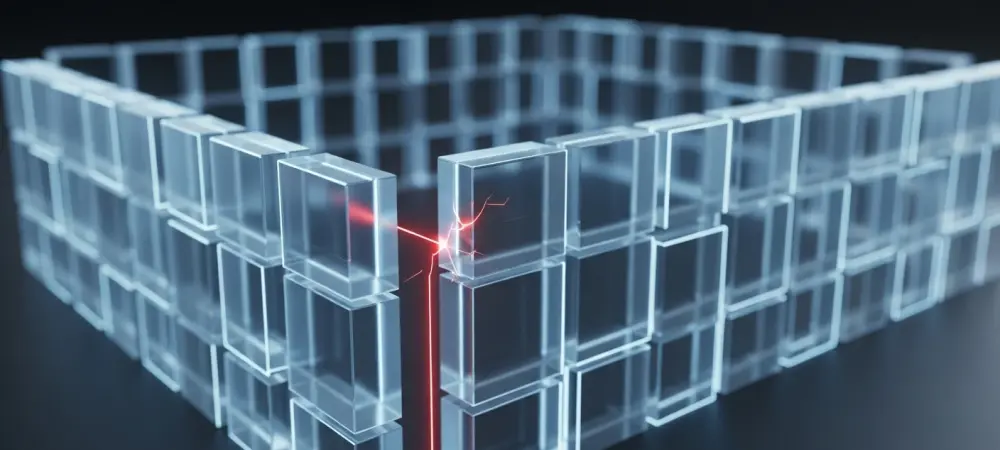
The architectural integrity of global digital infrastructure is no longer maintained by human hands alone; instead, it increasingly relies on self-healing, autonomous agents capable of neutralizing threats at machine speed. This fundamental departure from manual, reactive defense signifies a paradigm
- Cyber Security

The architectural integrity of global digital infrastructure is no longer maintained by human hands alone; instead, it increasingly relies on self-healing, autonomous agents capable of neutralizing threats at machine speed. This fundamental departure from manual, reactive defense signifies a paradigm
Popular Stories
- Cyber Security

The recent confirmation of a sophisticated network intrusion at Medtronic has sent ripples through the medical technology sector, highlighting the persistent vulnerability of critical healthcare infrastructure in an increasingly digital world. This specific incident came to light after the notorious
Deeper Sections Await
- Cyber Security
Dominic Jainy is a distinguished IT expert specializing in the intersection of artificial intelligence and blockchain, bringing a rigorous analytical approach to software security. His experience in managing complex systems allows him to dissect the architectural risks inherent in open-source
- Cyber Security
Microsoft Copilot’s deep integration into the enterprise workflow promised a revolution in productivity, yet this very integration has exposed a critical vulnerability that challenges the fundamental trust between organizations and their AI assistants. This review explores a significant security flaw,
Browse Different Divisions
- Cyber Security
Dominic Jainy is a distinguished IT expert specializing in the intersection of artificial intelligence and blockchain, bringing a rigorous analytical approach to software security. His experience in managing complex systems allows him to dissect the architectural risks inherent in open-source
- Cyber Security

The unseen infrastructure that powers modern civilization is currently facing an aggressive expansion of cyber-espionage that threatens the very backbone of global society. While typical data breaches target financial records or personal information, a new wave of adversaries is now
- Cyber Security
The modern enterprise’s reliance on virtualization has created a vast, interconnected attack surface where a single oversight in disaster recovery tools can lead to total network compromise. The cybersecurity landscape has recently been rattled by the discovery of a high-stakes
- Cyber Security

The era of the simple, static fake login page has vanished, replaced by a sophisticated and dynamic middleman architecture that renders traditional “look-before-you-click” advice effectively obsolete. As security teams have fortified the perimeter with Multi-Factor Authentication (MFA), the criminal underground
- Cyber Security

Digital defense perimeters are crumbling as Latin American enterprises face a relentless barrage of cyberattacks that significantly outpace the global average. While the rest of the world navigates a complex security landscape, this region has become a distinct focal point
- Cyber Security
Microsoft Copilot’s deep integration into the enterprise workflow promised a revolution in productivity, yet this very integration has exposed a critical vulnerability that challenges the fundamental trust between organizations and their AI assistants. This review explores a significant security flaw,
Browse Different Divisions
Popular Stories
Uncover What’s Next



















