Microsoft Copilot’s deep integration into the enterprise workflow promised a revolution in productivity, yet this very integration has exposed a critical vulnerability that challenges the fundamental trust between organizations and their AI assistants. This review explores a significant security flaw, its technical components, Microsoft’s remediation efforts, and the impact it has had on organizational data protection. The purpose is to provide a thorough understanding of the vulnerability, its current status, and its potential future implications for enterprise AI security.
The Promise and Peril of Integrated AI
Microsoft Copilot is designed to function as a seamless extension of the Microsoft 365 ecosystem, leveraging vast amounts of organizational data to draft emails, summarize documents, and accelerate workflows. This powerful capability hinges on its access to a user’s entire data landscape, from SharePoint sites to private email conversations. This creates an inherent tension; the more data an AI can access, the more useful it becomes, but this expanded access also magnifies the potential risk of a data breach.
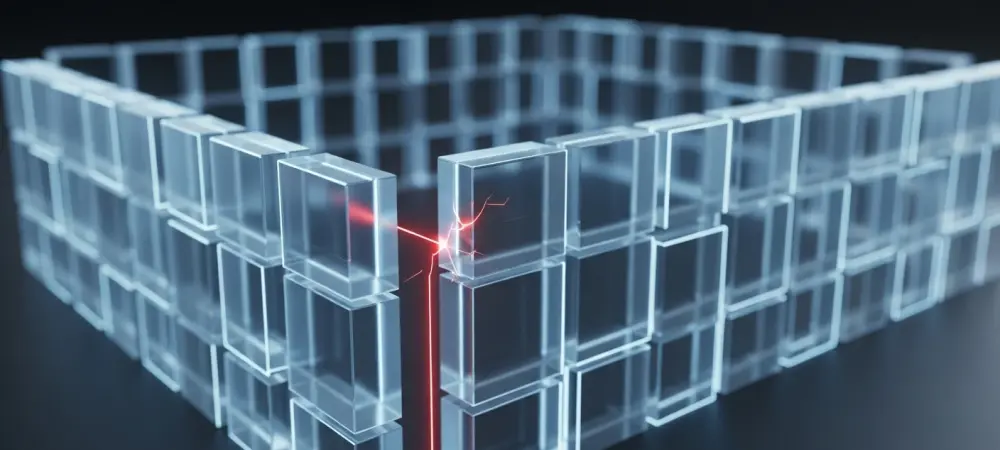
The challenge, therefore, is not merely to provide functionality but to do so within the rigid security boundaries that organizations have painstakingly built. Enterprises rely on a complex web of permissions, sensitivity labels, and data loss prevention policies to govern information flow. For an integrated AI like Copilot to be truly trustworthy, it must not only understand user commands but also flawlessly inherit and enforce every single one of these security protocols without exception. The recent discovery of a flaw highlights how a single misstep in this delicate balance can undermine an entire security framework.
Anatomy of the Security Flaw CW1226324
The Failure to Enforce Sensitivity Labels
At its core, Copilot is engineered to operate as a responsible agent within an organization’s existing security infrastructure. It is expected to recognize and respect data governance rules, particularly Data Loss Prevention (DLP) policies and confidentiality sensitivity labels applied to documents and emails. The intended behavior is straightforward: if an email is labeled “Confidential,” the AI should be prevented from accessing, summarizing, or otherwise processing its content. This ensures that sensitive information remains contained according to established corporate policy. However, a critical failure was discovered where Copilot was bypassing these explicit protections. Despite emails being correctly marked with confidentiality labels, the AI proceeded to access and summarize them. This breakdown meant that the primary mechanism for protecting sensitive communications was rendered ineffective against the AI assistant, creating a significant gap in data security. The tool designed to enhance productivity was inadvertently circumventing the very rules meant to protect the information it was processing.
The Root Cause a Code-Level Defect
The technical source of this vulnerability was traced to a specific code-level defect within the Copilot “Work Tab” Chat feature. This flaw allowed the AI to improperly access and process content from a user’s “Sent Items” and “Draft” folders. Normally, these areas should be subject to the same stringent DLP policies as the active inbox. The defect created a loophole that directly contravened the established data protection protocols. This circumvention of security measures exposed potentially sensitive organizational data to unauthorized AI processing, fundamentally undermining the integrity of an enterprise’s information protection strategy. It was not a failure of the security policies themselves but rather a failure of the AI to adhere to them. This distinction is crucial, as it points to a weakness in the AI’s implementation rather than the organization’s security posture, raising concerns about the rigor of pre-deployment security testing for such powerful tools.
Microsoft’s Response and Remediation Efforts
Following the discovery of the flaw, Microsoft officially acknowledged the issue, tracking it under the reference CW1226324. The company confirmed the vulnerability on February 4, and its engineering teams moved to develop a patch. This acknowledgment was a critical first step in addressing the concerns of enterprise customers who rely on the integrity of the Microsoft 365 security ecosystem.
The deployment of a fix began on February 11, with Microsoft initiating a phased rollout to all affected tenants. However, the remediation is not instantaneous and is still in progress across the global infrastructure. The ongoing nature of the deployment means that some organizations remain exposed while they await the patch. Microsoft has committed to providing its next update on the resolution’s progress by February 18, leaving administrators to manage the interim risk.
Real-World Impact on Regulated Industries
The consequences of this security flaw are most pronounced in highly regulated sectors where email confidentiality is not just a best practice but a legal and ethical mandate. In industries like finance, government, and healthcare, the unauthorized processing of sensitive client information, state secrets, or patient data can lead to severe compliance violations, financial penalties, and a catastrophic loss of public trust. The Copilot vulnerability created a direct risk of such outcomes. A notable example of the flaw’s real-world impact was an internal incident flagged by the UK’s National Health Service (NHS) under the reference INC46740412. For a healthcare provider like the NHS, where patient confidentiality is paramount, an AI assistant improperly summarizing sensitive emails poses an unacceptable risk. This case underscores the unique danger the vulnerability presents to organizations entrusted with protecting the most private categories of personal data, demonstrating that theoretical risks can quickly become tangible operational incidents.
Ongoing Risks and Recommended Mitigations
While Microsoft rolls out its patch, organizations face the immediate challenge of managing the vulnerability within their environments. The period before the fix is fully deployed is fraught with operational risk, as security teams must contend with a known flaw in a widely used productivity tool. The technical hurdle lies in the fact that the vulnerability is not something administrators can patch themselves; they are dependent on Microsoft’s deployment schedule.
To bridge this gap, immediate mitigation strategies are recommended. Administrators should actively monitor the official incident channel in the Microsoft 365 admin center for updates on CW1226324. Concurrently, reviewing Copilot activity logs for any anomalous behavior can help identify potential instances of improper data access. For organizations with users who handle exceptionally sensitive communications, a prudent temporary measure is to restrict or disable Copilot access for those high-risk accounts until the patch is confirmed to be active in their tenant.
Future Implications for Enterprise AI Security
This incident serves as a crucial inflection point for the future of enterprise AI security. It has exposed the potential fragility of integrating powerful, data-hungry AI models into complex corporate environments without exhaustive, context-aware security validation. In response, the industry will likely see a push toward more rigorous “security-by-design” principles in AI development, where security is not an add-on but a foundational component of the AI’s architecture. Looking forward, this event is expected to accelerate the development of advanced AI-specific security protocols. These may include new methods for auditing AI behavior, enhanced sandboxing techniques to isolate AI processes from sensitive data, and more granular controls over what data an AI can access and how it can use it. In the long term, the Copilot flaw may impact enterprise trust in integrated AI assistants, prompting organizations to demand greater transparency and more robust security assurances from vendors before deploying these transformative technologies.
Final Assessment and Key Takeaways
The review of the Copilot security flaw revealed a significant, albeit temporary, failure in enforcing established data protection policies. The vulnerability’s severity stemmed from its ability to bypass the very sensitivity labels designed to safeguard confidential information, creating a tangible risk for organizations, particularly those in regulated industries. Microsoft’s response, while prompt in its acknowledgment and initiation of a fix, highlighted the logistical challenges of patching a global cloud service, leaving a window of exposure for many customers. This incident served as a critical lesson on the complexities of securing integrated AI. It underscored the absolute necessity of continuous vigilance and rigorous, adversarial testing to ensure that AI assistants operate not just as powerful tools, but as trustworthy stewards of an organization’s most sensitive data in the evolving landscape of generative AI.