Cyber Security
- Cyber Security

Dominic Jainy brings a wealth of experience in machine learning and blockchain to the table, making him a critical voice in the conversation regarding the security of AI-generated code. As “vibe coding” shifts from a niche trend to a production
- Cyber Security

Dominic Jainy brings a wealth of experience in machine learning and blockchain to the table, making him a critical voice in the conversation regarding the security of AI-generated code. As “vibe coding” shifts from a niche trend to a production
Popular Stories
- Cyber Security

A single, unsuspecting click on a seemingly routine password reset notification recently managed to dismantle a multi-billion-dollar retail empire in a matter of hours. This spear-phishing incident did not just leak data; it triggered a sophisticated ransomware wave that paralyzed
Deeper Sections Await
- Cyber Security
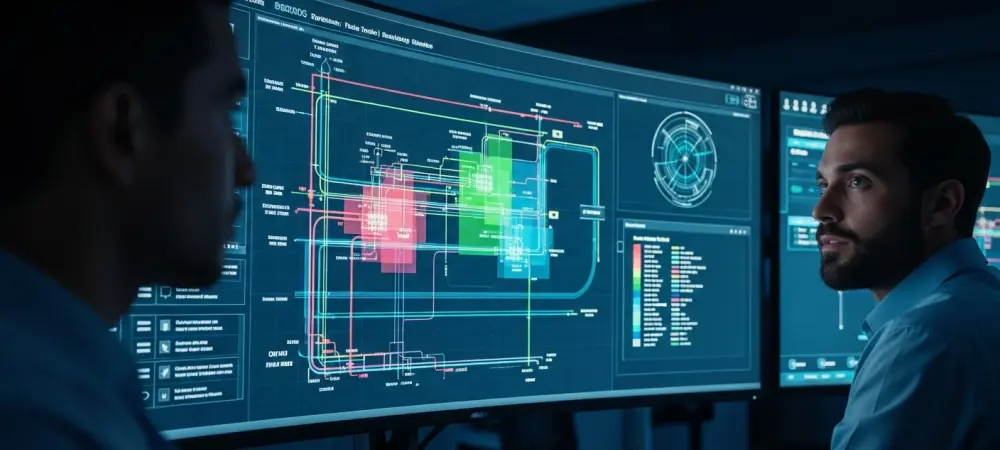
The silent hum of a power station or the steady flow of a water treatment plant belies a new and urgent vulnerability, where a digital breach can now cascade into catastrophic physical consequences for the public. As industrial control systems
- Cyber Security

On January 16, a synchronized security initiative from Google and Mozilla sent a clear message across the digital landscape, underscoring the relentless battle to protect the primary tool people use to interact with the internet. This coordinated release of urgent
Browse Different Divisions
- Cyber Security
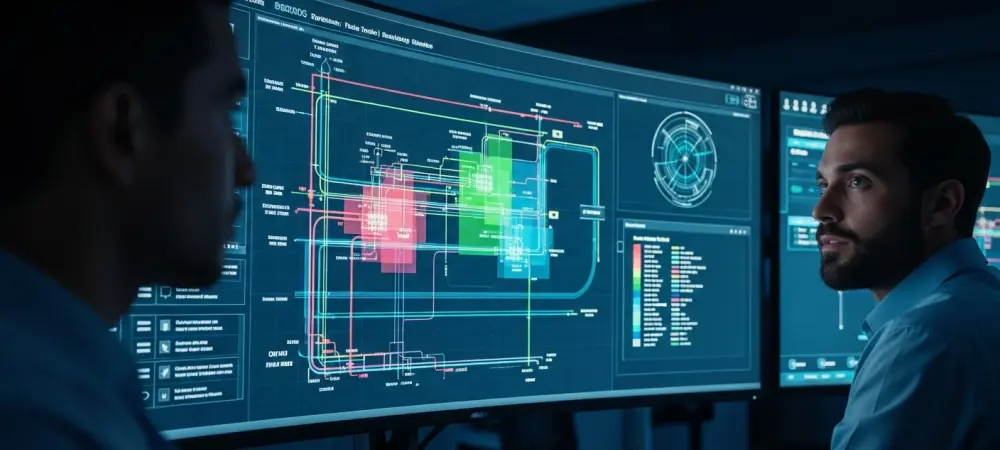
The silent hum of a power station or the steady flow of a water treatment plant belies a new and urgent vulnerability, where a digital breach can now cascade into catastrophic physical consequences for the public. As industrial control systems
- Cyber Security

A recent report from the security firm Wiz detailed a critical vulnerability, named “CodeBreach,” revealing that the intricate digital scaffolding supporting global commerce was far more fragile than imagined, as just two missing characters in an internal script nearly unlocked
- Cyber Security

A critical piece of global cybersecurity infrastructure nearly vanished not long ago, sending a clear warning to governments and businesses worldwide about the dangers of relying on a single, centralized system for tracking software vulnerabilities. This near-miss event has directly
- Cyber Security

With recent leadership changes and a significant workforce reduction, the Cybersecurity and Infrastructure Security Agency (CISA) is undergoing a profound transformation. To understand the implications of this new direction, we sat down with Dominic Jainy, a veteran IT professional whose
- Cyber Security

The blinding speed of a modern cyberattack, often measured in milliseconds, can render a traditional human-led incident response strategy obsolete before the first critical alert even registers on a security analyst’s screen. This stark reality has exposed a fundamental flaw
- Cyber Security

On January 16, a synchronized security initiative from Google and Mozilla sent a clear message across the digital landscape, underscoring the relentless battle to protect the primary tool people use to interact with the internet. This coordinated release of urgent
Browse Different Divisions
Popular Stories
Uncover What’s Next