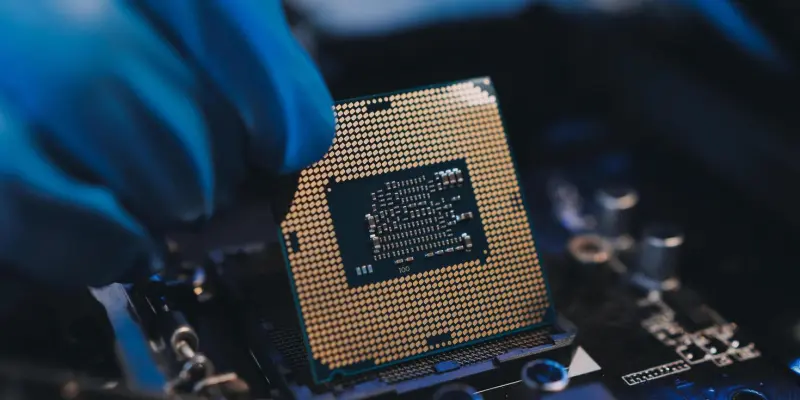
The ongoing concern regarding vulnerabilities in Intel CPUs is once again at the forefront of cybersecurity discussions as researchers have identified potential threats in modern processors. These threats, which harken back to the Spectre vulnerabilities discovered over seven years ago, exploit CPU prediction processes to gain unauthorized access to sensitive data. A recently uncovered flaw, named Branch Privilege Injection (BPI), exemplifies the persistent nature of these threats. BPI leverages a vulnerability in the CPU’s prediction processes, allowing unauthorized users to access data from their counterparts sharing the same processor. This flaw discovered by researchers at ETH Zürich affects all modern Intel CPUs, highlighting the longevity of the Spectre vulnerabilities as a significant security concern. With technology continuously evolving and users demanding higher security standards, these discoveries necessitate a reassessment of existing protections in place for CPU architecture, pushing both industry leaders and consumers to prioritize safeguarding sensitive data.
The identified BPI flaw operates by exploiting Branch Predictor Race Conditions (BPRC), which can enable unprivileged users, those without security clearance from the operating system, to circumvent established security mechanisms. This breach allows them to access confidential information from privileged processes, raising serious concerns about data protection within shared environments. The BPI vulnerability is cataloged under the CVE identifier CVE-2024-45332 and rated with a CVSS v4 score of 5.7, reflecting its impact on affected systems. In response, Intel has acted quickly by developing and disseminating microcode patches aimed at mitigating the risk presented by this vulnerability. Despite these efforts, the BPI flaw serves as a stark reminder of the challenges facing hardware security, particularly in processors, where underlying architectural weaknesses can be manipulated to expose critical data. Continuous research and timely interventions are essential to address these evolving threats and ensure robust security frameworks remain in place.
Spectre v2: A Persistent Threat
Parallel investigations by VUSec at Vrije Universiteit Amsterdam have uncovered additional threats related to Spectre v2 vulnerabilities, specifically a new class called Training Solo attacks. Unlike previous variants, these attacks do not rely on the presence of sandbox environments, raising the stakes for how Spectre v2 vulnerabilities can be exploited. Training Solo attacks, by compromising memory across privileged boundaries, manage to breach previously secure environments, reigniting concerns prevalent during the initial discovery of Spectre flaws. This renewed form of attack poses a significant risk, as it enables unauthorized access to sensitive kernel memory at alarming rates, potentially reaching up to 17 Kb/s. The vulnerabilities identified, namely CVE-2024-28956 and CVE-2025-24495, highlight a critical gap in current CPU defenses, particularly for systems reliant on memory isolation. These recent findings emphasize the fundamental need for continued vigilance and innovation in processor security. They bring to light the sophisticated tactics employed by malicious actors to exploit known and emerging vulnerabilities within CPU architectures. As Intel and other industry giants strive to roll out comprehensive updates and guidance, the ongoing research underscores their commitment to shield users from such threats. However, the rapidly changing landscape of cyber threats demands agility and foresight in security designs, ensuring that newly developed protections evolve alongside potential vulnerabilities. These insights gleaned from recent research encourage a proactive approach in safeguarding processor integrity, protecting sensitive information from increasingly sophisticated exploits.
Future of Processor Security
The resurgence of concerns over Intel CPU vulnerabilities is a focal point in cybersecurity circles, with researchers identifying potential threats in modern processors. These threats echo the Spectre vulnerabilities found over seven years ago, where CPU prediction processes are exploited to gain unauthorized data access. A newly uncovered flaw, called Branch Privilege Injection (BPI), highlights the ongoing nature of these threats. BPI exploits a vulnerability in CPU prediction processes, allowing unauthorized users to access data if they share the processor with targeted processes. Discovered by ETH Zürich researchers, this flaw affects all modern Intel CPUs, underscoring the enduring challenge posed by Spectre vulnerabilities. As technology evolves, the demand for stringent security measures underscores the need for reassessing CPU architecture protections. This pushes industry leaders and consumers to emphasize safeguarding data. BPI affects systems by exploiting Branch Predictor Race Conditions, enabling unprivileged users to bypass security. Cataloged under CVE-2024-45332 with a CVSS v4 score of 5.7, Intel has issued microcode patches to counter this vulnerability. Despite these steps, BPI highlights the ongoing hardware security challenges, particularly in processors. Continuous research and timely interventions are crucial to maintaining robust security frameworks amid evolving threats.