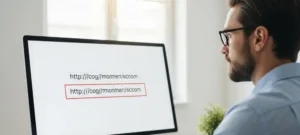
Introduction The digital key that unlocks your entire online life, your password manager’s master password, has become the prime target of a sophisticated and evolving phishing campaign aimed at LastPass users. This situation underscores a critical vulnerability in modern digital security: the immense power concentrated in a single credential. The purpose of this frequently asked questions article is to dissect