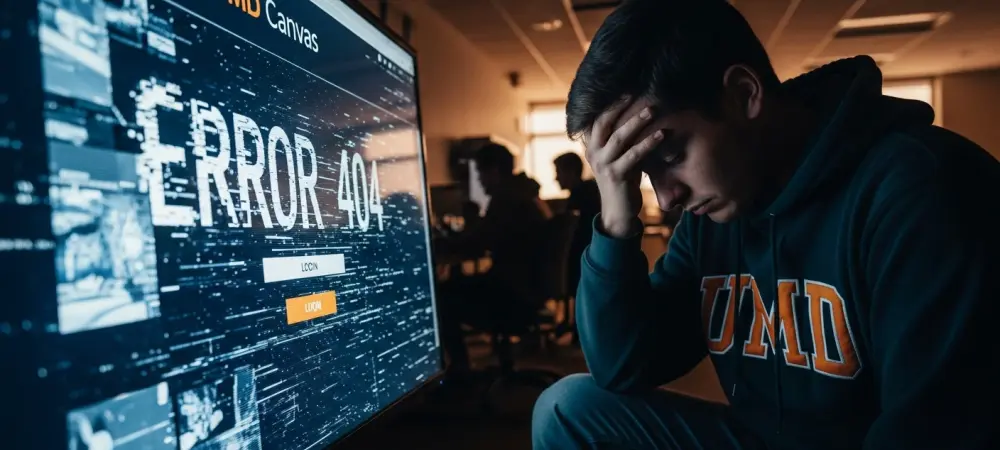
The sudden disappearance of a digital learning portal on the eve of final exams is no longer a hypothetical nightmare but a stark reality that recently paralyzed one of the nation’s leading academic institutions. When the University of Maryland saw its Canvas learning management system vanish under the pressure of a targeted cyberattack, the event did more than just delay tests; it shattered the illusion of perpetual digital availability. This breach, orchestrated by a group known as ShinyHunters, highlighted a dangerous “imagination gap” where the convenience of centralized cloud technology outpaced the contingency planning of the administration. As universities evolve into digital-first environments, the necessity of adopting rigorous security protocols has transitioned from a technical preference to a core institutional mandate. Academic continuity depends on the ability to withstand disruptions that target students when they are most vulnerable. By prioritizing proactive cybersecurity, institutions protect sensitive student data and shield themselves from the cascading legal liabilities and reputational damage that follow a high-profile breach. Moreover, a resilient posture reduces the long-term financial fallout and mitigates the immense psychological stress placed on a student body already facing high-stakes academic deadlines.
Understanding the Canvas Cyberattack and the Need for Resilient Systems
The May 2024 cybersecurity disruption at the University of Maryland serves as a definitive case study in modern educational vulnerability. By targeting the Canvas platform, the attackers effectively severed the link between students and their essential course materials, proving that a single point of failure can halt the entire educational process. This incident demands a shift toward resilient systems that do not merely aim to keep intruders out but are specifically designed to maintain functionality even when a primary service provider is compromised.
Robust cybersecurity best practices are vital for ensuring that learning does not stop when the internet does. Establishing a culture of resilience requires a dual focus: institutions must harden their infrastructure against third-party failures, while students must take ownership of their personal data footprints. The goal is to move beyond passive reliance on external vendors and toward a model of active defense. Such a transition ensures that even if a major platform like Canvas goes dark, the academic mission remains intact through alternative pathways and prepared responses.
The Critical Importance of Proactive Cybersecurity in Higher Education
In the current landscape, following best practices is the only way to safeguard the integrity of the degree-granting process. When a university functions as a digital ecosystem, its security perimeter is no longer defined by physical walls but by the strength of its encrypted connections and the reliability of its software partners. Rigorous protocols ensure that high-stakes periods, such as finals week, remain uninterrupted by external threats. This proactive approach is a necessary investment in the institution’s future, preventing the erosion of trust that occurs when student information is leaked or held for ransom.
Furthermore, the long-term benefits of an aggressive security stance extend far beyond technical stability. By anticipating threats rather than simply reacting to them, universities can avoid the staggering costs associated with forensic investigations and credit monitoring services for thousands of users. This level of preparation also serves a humanitarian purpose; it minimizes the anxiety and frustration experienced by students who rely on these systems for their livelihoods. In contrast to a reactive “wait and see” approach, proactive security builds a foundation of reliability that enhances the overall prestige of the academic community.
Essential Best Practices for Institutional and Individual Security
To effectively address the vulnerabilities exposed by recent hacks, stakeholders must abandon the habit of passive technology consumption. Resilience is built through a combination of institutional oversight and individual vigilance, creating multiple layers of protection that are difficult for bad actors to penetrate. This requires a fundamental change in how both administrators and students view their roles within the digital campus, moving from mere users to active participants in a collective security framework.
Implementing Comprehensive Incident-Response Simulations
Institutions must move beyond basic technical backups and begin conducting regular “fire drills” for their digital infrastructure. It is not enough to simply have a copy of the data stored somewhere; the organization must practice the specific steps required to deploy that data and communicate with the public during a total lockout. Tabletop exercises that simulate specific failure scenarios help identify where communication might break down and which departments are unprepared for a sudden loss of access.
The 19-hour recovery period during the UMD incident revealed that while the data itself remained safe, the lack of a practiced communication plan created a vacuum of information. Without an official, authenticated channel providing constant updates, students were forced to rely on unverified social media accounts for news about their exams. This underscores the need for pre-planned response protocols that prioritize transparency and ensure that the administration remains the primary source of truth throughout a crisis.
Strengthening Third-Party Risk Management and Supply Chain Audits
Modern universities must perform deep-dive audits of their EdTech vendors to understand the security posture of the entire software supply chain. Often, a university may trust a primary provider while remaining completely unaware of the vulnerabilities present in that provider’s own sub-vendors. This “downstream” oversight is essential for identifying the weakest links in the chain of services that keep a campus running. A clear example of this danger was seen during the MOVEit exploit, which demonstrated how a single flaw in a third-party file-transfer program could compromise hundreds of institutions simultaneously. This event proved that a university’s security is only as strong as its most vulnerable external partner. Consequently, administrators should prioritize vendors who demonstrate radical transparency and provide detailed insights into their own defensive measures and sub-contractor risks.
Advancing Student Digital Hygiene and Local Redundancy
Students should be encouraged to adopt a defensive posture by utilizing multi-factor authentication and maintaining offline copies of their most important course materials. Relying entirely on “the cloud” creates a dangerous dependency that can leave a student helpless during a server outage. By practicing good digital hygiene, students protect their personal identities and ensure that their academic progress is not tethered to a single website.
Following the disruptions at Maryland, a noticeable shift in student behavior occurred as more individuals began downloading lecture slides and assignment prompts locally. This movement toward “local redundancy” acts as a personal fail-safe, ensuring that the materials needed for study remain accessible even if the central server is attacked. This habit of saving critical files offline is a simple yet powerful way to decouple one’s academic success from the stability of a third-party platform.
Final Evaluation: Bridging the Gap Between Convenience and Security
The vulnerabilities revealed by the disruption of centralized platforms served as a definitive wake-up call for the higher education sector. It became clear that the convenience offered by third-party educational tools carries inherent risks that can only be managed through rigorous oversight and practiced resilience. Moving forward, the focus shifted from simple perimeter defense toward a more holistic strategy that included constant crisis simulation and a demand for greater vendor transparency.
The path toward a more secure campus environment required both faculty and students to adopt “local redundancy” habits, ensuring that critical academic content was never stored in only one location. Administrators learned to evaluate new technology not just by its features, but by the vendor’s history of transparency and the institution’s ability to maintain operations if that service failed. Ultimately, the lessons learned from these digital disruptions transformed security into a shared responsibility, requiring constant vigilance and a proactive mindset from every member of the campus community.