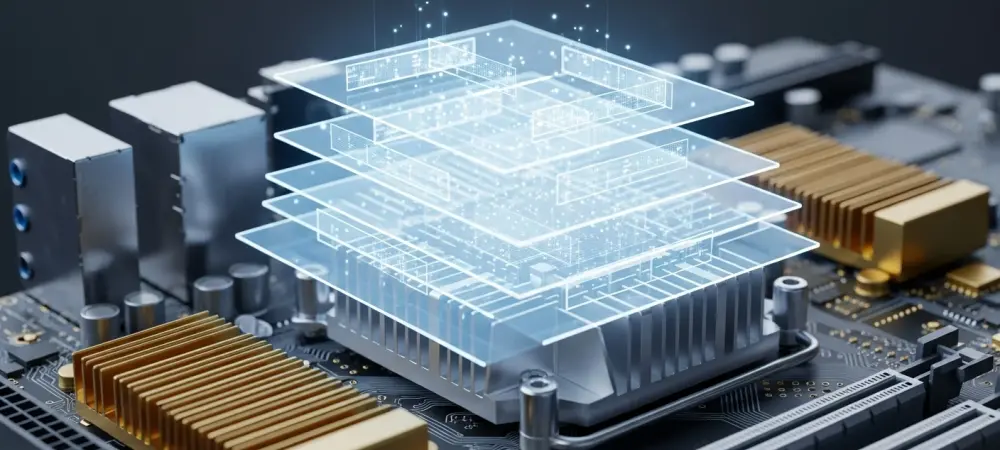
The digital infrastructure that binds the global economy together recently survived a stress test so severe that it forced a total architectural rethink of how security interacts with the core of our operating systems. This transformation, catalyzed by a period of unprecedented system instability, marks a definitive departure from the traditional “all-access” model that governed third-party software for decades. Historically, the Windows kernel was viewed as the necessary battleground for security vendors, a place where absolute visibility required absolute privilege. However, the systemic risks associated with this level of access became impossible to ignore when localized software errors began triggering global operational paralysis. In response, the industry is currently navigating the Windows Resiliency Initiative, a strategic overhaul designed to decouple mission-critical security functions from the most sensitive layers of the operating system architecture. This evolution represents more than a technical patch; it is a fundamental reassessment of the balance between the “absolute power” required by security tools and the operational stability of the global digital landscape.
The Shift: Operating System Resilience
The catastrophic disruption experienced across the global IT sector served as the final warning for an industry that had become overly reliant on kernel-level integrations. When a faulty update in a privileged security layer paralyzed critical infrastructure, it exposed a fragile reality where a single line of third-party code could render millions of systems inoperable. The resulting strategic shift toward operating system resilience seeks to move away from this precarious dependency. Microsoft, in tandem with major security providers, is now prioritizing an architecture that isolates security processes, ensuring that a failure in a protection agent does not escalate into a total system collapse. This movement signifies a transition toward “fail-safe” engineering, where the primary objective is to maintain system availability even when individual software components encounter critical errors.
Data and Trends: Systemic Risk and Recovery
The scale of modern digital disruption has provided a stark dataset for proponents of architectural reform. The most significant outages on record rendered over eight million Windows machines inoperable simultaneously, a figure that underscored the dangers of centralized kernel dependence. This was not merely a technical glitch but a massive economic event, with Fortune 500 companies alone sustaining losses exceeding $5 billion. These statistics have catalyzed a sudden and aggressive market demand for resilient software solutions, as organizations realize that the cost of downtime often far outweighs the theoretical benefits of deep-kernel security hooks. Consequently, the industry is seeing a rapid migration toward frameworks that prioritize modularity and isolation over integrated vulnerability.
This trend is further evidenced by the accelerated adoption of the Microsoft Virus Initiative (MVI) 3.0 framework. Currently, a core group of approximately twelve major security vendors—including industry leaders like ESET, Bitdefender, and SentinelOne—has moved into a phase of real-time API co-development with Microsoft. This collaborative effort focuses on building high-performance pathways that do not require kernel-level residency for effective threat detection. Moreover, there is a growing regulatory trend toward “staged rollout” mandates. Enterprise deployment strategies now frequently require security updates to be released in controlled phases, preventing localized bugs from escalating into global catastrophes. This shift in deployment philosophy reflects a broader realization that the speed of security updates must be balanced with the necessity of rigorous stability testing.
Real-World Applications: User-Mode Security
The practical application of these architectural changes is most visible in the ongoing transition from kernel-mode to user-mode security operations. Security vendors are actively inventorying legacy codebases to migrate risky logic—specifically frequently updated detection signatures—to the safer user-mode environment. In this restricted space, a software crash or an unhandled exception does not trigger the dreaded Blue Screen of Death, but rather results in a simple process restart. This shift ensures that the underlying operating system remains functional even if the security agent itself fails. By moving the “brain” of the security tool out of the kernel, developers are creating a more robust defense-in-depth strategy that protects the host system from its own guardians. The Windows Resiliency Initiative is also manifesting through the creation of new, high-performance APIs that allow third-party tools to maintain visibility into system processes without residing in the kernel. These interfaces provide the necessary data for threat detection while maintaining a strict boundary that prevents third-party code from interfering with core system memory. In practice, major financial and healthcare institutions are already prioritizing “out-of-process” security solutions. These organizations require restartable protection that ensures core business operations remain online during a security event. Furthermore, regulatory bodies and cyber insurance providers are beginning to influence this trend, with organizations like NIST evaluating frameworks that favor user-mode resilience. Some insurance providers are even considering lower premiums for companies that utilize these safer architectural standards, effectively turning system resilience into a financial incentive.
Industry Expert Perspectives: The Consensus View
The transition away from kernel-heavy architectures has sparked a robust debate among cybersecurity thought leaders regarding the future of endpoint protection. Most experts suggest that while certain foundational elements must remain in the kernel for optimal performance, the future of Endpoint Detection and Response (EDR) is undeniably hybrid. This consensus reflects a pragmatic middle ground, acknowledging that while user mode offers superior stability, the kernel still provides the lowest-latency access to hardware events. Industry consultants emphasize that the goal is not to eliminate kernel access entirely but to minimize the “attack surface” of third-party code within that sensitive space. By relocating non-essential functions, developers can reduce the probability of a system-wide failure without compromising the core effectiveness of their security suites.
The Visibility vs. Stability Debate
A central point of tension in this evolution is the ongoing “visibility versus stability” debate. Historically, security tools required kernel access to perform “pre-execution” blocking—the ability to stop a malicious process before it can execute its first instruction. Experts highlight that moving these functions to user mode introduces potential latency that sophisticated malware might exploit. There is a concern that a malicious process could complete its payload delivery before a user-mode security tool receives the notification to intervene. To address this, industry veterans are working on hybrid models that use lightweight kernel “sensors” to feed data to robust user-mode “analyzers.” This approach aims to provide the best of both worlds: the speed of the kernel and the safety of user-mode processing.
Collaborative Engineering: A New Standard
Renowned professionals across the sector emphasize that the current level of cooperation between Microsoft and its competitors is virtually unprecedented. Traditionally, operating system internals were a closely guarded secret, and security vendors had to reverse-engineer certain functions to achieve the deep integration they desired. Today, however, the “unpicking” of decades of legacy code is a collaborative effort. This partnership is essential to ensure that moving functions out of the kernel does not create new, unforeseen vulnerabilities. Industry veterans warn that the migration must carefully manage the “performance penalty” associated with moving data between different operating modes. If the transition introduces significant processing delays, there is a risk that users might disable security features to regain system speed, creating a different type of security gap.
The Future: Kernel-Level Integration Evolution
Looking ahead, the evolution of kernel-level integration is expected to lead to the emergence of “protected” user-mode environments. These specialized spaces will provide security processes with the same level of tamper-resistance found in the kernel but without the associated risks to system stability. In this future state, malware will be unable to shut down security tools even if they are running at the same privilege level. This architectural innovation will likely become the new standard for all high-reliability software, not just security products. The primary benefit of this evolution will be an “invisible” resilience; future software bugs will result in a single application restart rather than a total system collapse, making the digital ecosystem far more robust against both accidents and attacks.
However, several anticipated challenges remain on the horizon. The “EDR Killer” trend—where sophisticated malware attempts to identify and terminate security processes—will likely intensify as both defenders and attackers move to the same privilege level in user mode. This will require the development of even more advanced self-protection mechanisms for security software. Additionally, the migration process itself is a massive, multi-year undertaking that requires rewriting millions of lines of code. Despite these hurdles, the broader implications of this shift are clear: it marks the maturation of the software industry. We are moving away from a “trust-all” model toward a “fail-safe” architecture that acknowledges the inevitability of human error. This transition is a necessary step in building a digital world where the failure of one component does not lead to the failure of the whole.
Summary: A Forward-Looking Perspective
The Windows Resiliency Initiative serves as a critical paradigm shift that redefines the relationship between the operating system and third-party security providers. By migrating non-essential and high-risk functions from the kernel to user mode, the industry is building a more “bulletproof” ecosystem. This ecosystem is becoming increasingly capable of weathering both flawed updates and malicious attacks without catastrophic failure. While the technical migration is an immense task, the transition is vital for the long-term stability of modern digital infrastructure. The industry’s commitment to this collaborative evolution ensures that system resilience is prioritized as a core pillar of global cybersecurity, shifting the focus from mere protection to total operational continuity.
The industry stakeholders recognized that the previous architectural standards were insufficient for the demands of a hyper-connected global economy. Engineers and policy makers moved with purpose to establish new protocols that prioritized the isolation of critical system components. They implemented more rigorous testing phases and adopted a modular approach to security that separated the engine of detection from the heart of the operating system. These decisions laid the groundwork for a more stable environment where technical errors were contained rather than broadcast across the global network. The transition successfully transformed the landscape from one of fragile dependencies into one of structured, resilient layers. Organizations that embraced these changes found themselves better equipped to handle the complexities of modern threats without sacrificing the uptime necessary for their survival. The shift ultimately proved that the path toward a secure future required a fundamental departure from the high-risk practices of the past, as the collective community chose a sustainable model over the convenience of unrestricted access.