A trusted tool used by millions, Notepad++, recently became the latest vector for a sophisticated state-sponsored cyberattack, highlighting the chilling reality that the software people rely on can be turned against them. This incident is not an anomaly but a symptom of a dangerously escalating trend in software supply chain security. The compromise of such a widely used application serves as a stark warning about the evolving nature of digital threats. This analysis will dissect this critical trend, examining the data behind the rise in attacks, analyzing real-world breaches, exploring the future trajectory of software security, and providing actionable insights for protection.
The Soaring Risk a Data Driven Look at Supply Chain Threats
The Alarming Growth of Supply Chain Attacks
The threat landscape is expanding at an unprecedented rate, with software supply chains emerging as the new frontline. Citing industry reports, analysis shows a year-over-year increase of over 600% in these targeted attacks. Cybercriminals and state-sponsored actors are no longer just targeting end-user systems; they are infiltrating every stage of the development lifecycle, from code repositories and build servers to final distribution and update mechanisms. This strategic shift means a single successful breach can have a catastrophic ripple effect, compromising millions of downstream users.
This surge in attacks carries a significant financial and reputational cost for affected organizations. The average cost of a breach originating from a supply chain compromise has now surpassed $4.5 million, a figure that does not fully capture the long-term damage to customer trust and brand integrity. The escalating financial stakes underscore the urgent need for a fundamental reevaluation of how software is developed, distributed, and verified in an increasingly interconnected digital ecosystem.
Anatomy of an Attack the Notepad++ Incident
The recent compromise of Notepad++ serves as a textbook example of modern supply chain attack methodology. In a highly targeted campaign identified as CVE-2025-15556, the advanced threat actor Lotus Panda successfully infiltrated the application’s update infrastructure. By compromising the hosting provider, the attackers were able to intercept update requests and selectively deliver a malicious installer containing the “Chrysalis” backdoor. This selective targeting allowed the threat actor to remain undetected while infiltrating high-value networks.
This incident demonstrates a critical evolution in attacker tactics, moving away from broad-stroke, indiscriminate attacks toward precision-targeted infiltration through trusted software channels. The victims spanned government, finance, and energy sectors across the United States, Europe, and Asia, showing the global reach and strategic intent of the campaign. By weaponizing a legitimate update process, the attackers bypassed traditional security measures and exploited the implicit trust between a user and their software provider.
Industry Voices Expert Perspectives on the New Threat Paradigm
In the wake of incidents like the Notepad++ breach, cybersecurity leaders are unified in their message: the era of implicit trust in third-party components and update servers is definitively over. The attack is a clear illustration of how adversaries are exploiting the weakest links in the chain of trust that underpins the entire software ecosystem. This new reality demands a paradigm shift away from assuming security toward actively verifying it at every step.
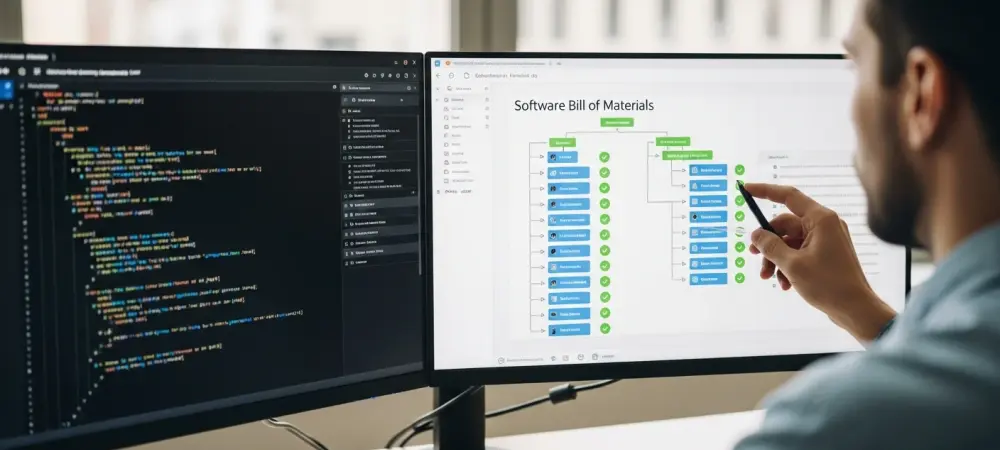
Experts are universally calling for a “zero-trust” approach to be embedded within the software development lifecycle. This model mandates verifiable integrity checks, such as robust digital signatures and comprehensive Software Bills of Materials (SBOMs), as a new industry standard rather than an optional best practice. The consensus is that only by treating every component, dependency, and update as potentially compromised can organizations begin to build a resilient defense against these sophisticated supply chain attacks.
The Future of Software Development Predictions and Countermeasures
The future of software security will be defined by proactive defense and verifiable integrity. A rapid acceleration is expected in the adoption of automated security tools directly within CI/CD pipelines, enabling developers to identify and remediate vulnerabilities in real time. Furthermore, the implementation of mandatory SBOMs for government and critical infrastructure contracts will become standard practice, creating a new baseline for transparency and accountability across the industry. Next-generation security protocols that cryptographically verify software identity from the source code to the end-user’s machine are also on the horizon.
However, significant challenges remain. The vast and complex open-source ecosystem, which forms the backbone of modern software, presents a particularly difficult surface to secure. Attackers will also continue to evolve their tactics, techniques, and procedures (TTPs), requiring a constant and dynamic defensive posture. The long-term implication of this trend is a fundamental and permanent shift in how software is built, distributed, and ultimately, trusted in the digital age.
Conclusion Securing the Chain Protecting the Future
The exponential rise in software supply chain attacks, exemplified by the sophisticated Notepad++ compromise, signaled an urgent and undeniable trend. The era of assuming software was inherently safe had conclusively ended. It became imperative for organizations to have adopted a defense-in-depth strategy that included rigorous code scanning, dependency management, and secure update mechanisms, such as Notepad++’s new “double lock” verification system. For end-users, the message was clear: they had to remain vigilant, update software from official sources immediately, and verify the legitimacy of downloads. Fortifying the software supply chain was recognized not just as an IT problem, but as a foundational requirement for a secure digital society.