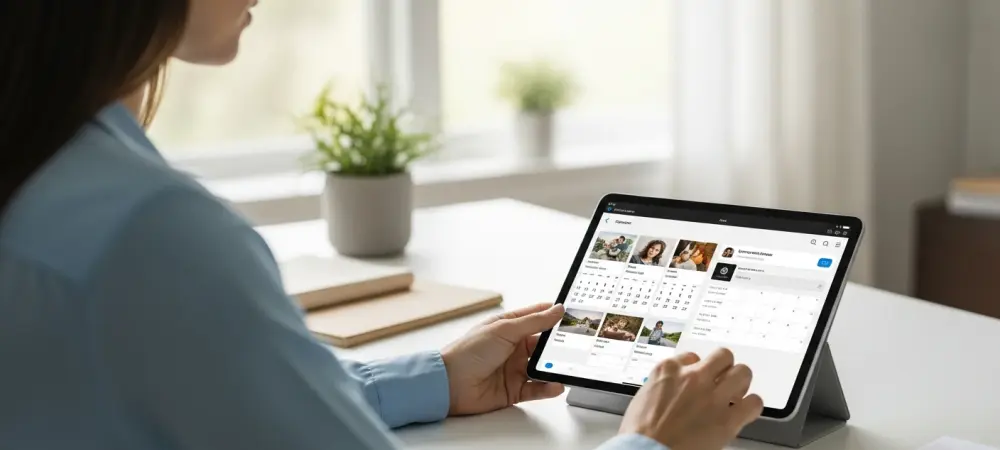
The transition from a reactive digital tool to a proactive life companion has arrived with the latest architectural shifts in personal artificial intelligence, fundamentally altering how individuals interact with their own digital footprints. This new era is defined by a feature known as Personal Intelligence, which represents a significant departure from traditional data processing by granting the AI system deep access to a user’s private ecosystem. By integrating directly with Google Photos, Gmail, and Calendar, the AI can synthesize information from thousands of disparate sources to construct a comprehensive understanding of a person’s life. This allows the system to recognize not only the user but also their family members and close associates without the need for manual tagging or explicit identification. The goal is to create a seamless digital experience where the software anticipates needs based on past behavior and stored memories, effectively moving beyond the limitations of generic responses to provide a highly customized and relevant interface for every user.
Automated Context: Evolution of the Proactive Assistant
Traditional interactions with artificial intelligence often required a tedious process of manual data entry where users had to upload specific files or provide lengthy descriptions to achieve personalized results. The introduction of the Nano Banana 2 architecture has effectively eliminated this friction by allowing the system to automatically fill in contextual gaps using the vast repositories of images and text already stored in the cloud. This underlying technology enables the AI to scan tens of thousands of personal photographs to identify specific likenesses and recurring themes, which it then uses to generate new content or answer complex queries. Instead of a user having to explain who their spouse or children are, the AI already possesses this knowledge through visual recognition and historical data patterns. This shift marks a transition from a tool that merely reacts to commands to a sophisticated assistant that understands the nuances of a user’s social circle and daily routines with minimal intervention.
Beyond simple recognition, this automated context allows the AI to facilitate creative and organizational tasks that were previously time-consuming for the average individual. For instance, the system can generate stylized images of specific family members in new settings by referencing their actual appearance from the photo library, ensuring a level of accuracy that generic models cannot match. This capability extends to scheduling and communication, where the AI might suggest meeting times based on calendar availability or draft emails that reflect the tone and context of past interactions. By synthesizing visual data with textual information from emails, the assistant creates a holistic view of the user’s life preferences. This high level of integration is designed to make the technology feel like a natural extension of the user’s thought process, proactively offering solutions and creative outputs that are deeply grounded in the personal reality of the individual’s unique history and relationships.
Security Frameworks: Balancing Innovation with User Discretion
The move toward hyper-personalization has sparked a significant debate regarding the preservation of digital boundaries and the inherent risks of intrusive data scanning. While some view the ability of an AI to guess user needs as a pinnacle of efficiency, others find the comprehensive scanning of intimate memories to be a step too far into private life. Critics argue that the benefits of convenience may not outweigh the discomfort of knowing a machine is constantly analyzing private photos and sensitive correspondence. This tension reflects a growing concern in the modern era about how much personal data should be sacrificed for the sake of technological utility. The primary challenge for developers lies in proving that such deep integration can be managed without compromising the fundamental right to privacy. As these systems become more capable of understanding the human experience, the conversation around data sovereignty and the psychological impact of constant surveillance has become increasingly prominent.
To address these valid concerns, specific guardrails have been implemented to ensure that users maintain control over their personal information. The Personal Intelligence feature is strictly an opt-in experience, meaning that the extensive scanning of photos and emails does not occur unless a user explicitly grants permission. Furthermore, the core large language models are not directly trained on a user’s private library; instead, the system utilizes specific prompts and responses to refine its performance over time without permanently absorbing sensitive private data into the global model. A transparent verification system, often accessible via a Sources button, allows individuals to see exactly which private images or documents were utilized to generate a specific output. These measures are intended to provide a layer of accountability, ensuring that the AI’s creative or analytical processes remain visible to the user. This approach seeks to mitigate the perceived creepiness of the technology by providing clear visibility into how the data is being handled.
Strategic Implementation: Navigating the Future of Data Integration
The rollout of these extensive personal intelligence capabilities began in the United States as a pivotal test case before expanding to a broader international audience. This phased approach allowed for the observation of how different demographics interact with such intimate technology and whether the initial privacy protections were sufficient to maintain public trust. As users navigated the complexities of this new digital landscape, the importance of clear communication regarding data usage became more evident than ever before. The decision to enable these features was often based on a personal cost-benefit analysis, where the utility of a truly personal assistant was weighed against the desire for digital isolation. Educational resources were distributed to help people understand how to toggle these features and how to audit the information the AI had gathered. This period of early adoption served as a crucial learning phase for both the developers and the public, shaping the standards for how personal data would be integrated into AI in the coming years.
The most effective way to engage with these advancements involved a proactive approach to setting digital boundaries and regularly reviewing permission settings. Users were encouraged to utilize the built-in transparency tools to verify that the AI was only accessing relevant information for the tasks at hand. It was discovered that maintaining a curated digital library helped improve the accuracy of the AI while reducing the amount of redundant data being scanned. Developers focused on enhancing the granularity of user controls, allowing individuals to select specific folders or time periods for the AI to analyze rather than granting blanket access to an entire history. This move toward more specific consent models represented a significant step in resolving the conflict between personalization and privacy. By choosing to engage with the technology on a limited and monitored basis, individuals were able to harness the power of personal intelligence while still retaining a sense of control over their most private digital assets.