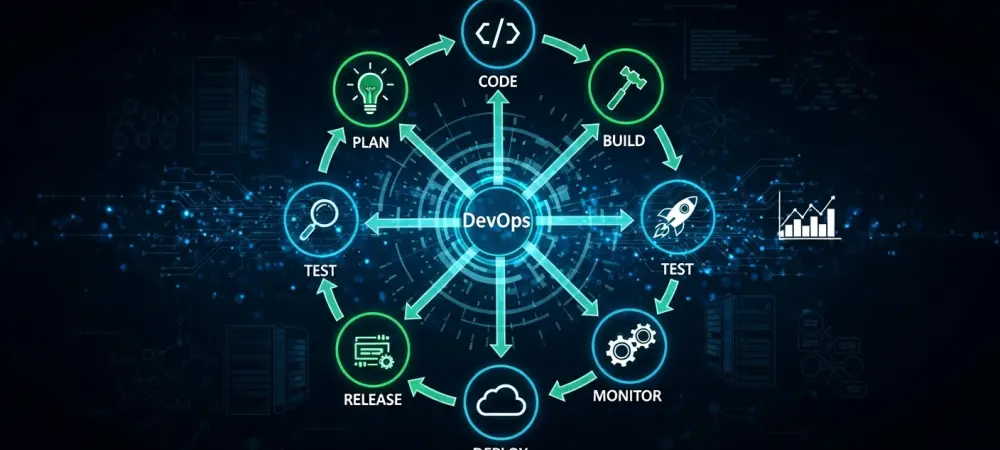
DevOps
- DevOps

The sheer volume of vulnerabilities detected in modern CI/CD pipelines has officially surpassed the cognitive capacity of human security analysts to manage manually without sacrificing development speed. This bottleneck necessitated a shift toward agentic AI, which operates with a degree
- DevOps

The sheer volume of vulnerabilities detected in modern CI/CD pipelines has officially surpassed the cognitive capacity of human security analysts to manage manually without sacrificing development speed. This bottleneck necessitated a shift toward agentic AI, which operates with a degree
Popular Stories
- DevOps
Azure DevOps has stood the test of time as a significant force in the DevOps space, offering an extensive suite of services that cater to various stages of the software development lifecycle. With a strong integrated approach weaving together planning,
Deeper Sections Await
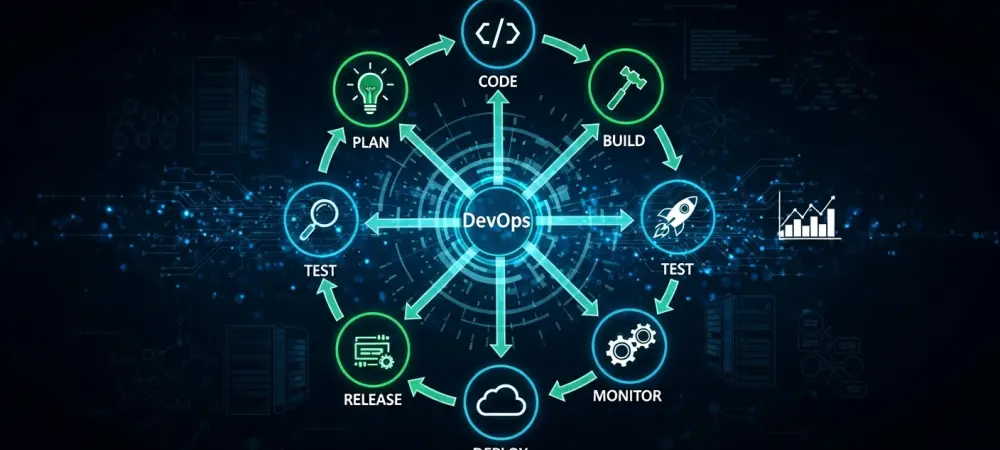
- DevOps
The era of engineers squinting at glowing dashboards to identify a single line of faulty code has reached its inevitable conclusion as systems surpass human cognitive limits. At the DASH 2026 conference, the conversation surrounding software health moved decisively away
- DevOps

Organizations in 2026 have moved beyond basic automation to embrace complex platform engineering models that prioritize developer experience alongside system stability. The current landscape of software delivery demands a sophisticated blend of technical mastery and cultural alignment to manage the
Browse Different Divisions
- DevOps
The era of engineers squinting at glowing dashboards to identify a single line of faulty code has reached its inevitable conclusion as systems surpass human cognitive limits. At the DASH 2026 conference, the conversation surrounding software health moved decisively away
- DevOps

The digital landscape is witnessing a seismic shift where machines generate logic faster than human minds can verify the underlying intent or architectural soundness, pushing traditional engineering workflows to a breaking point. A 26% spike in code production has left
- DevOps

Dominic Jainy is a seasoned IT professional whose career has been defined by his ability to navigate the complex intersections of artificial intelligence, machine learning, and blockchain technology. With a background rooted in building scalable systems, he has witnessed firsthand
- DevOps

The traditional safety margins of the software development lifecycle have evaporated as autonomous AI agents now execute commands at a velocity that renders human oversight functionally obsolete. While these intelligent tools accelerate the pace of deployment and code generation, they
- DevOps

The transition from simple autocomplete tools to autonomous software agents represents one of the most significant shifts in engineering productivity since the invention of the compiler. Visual Studio Code version 1.123 marks a pivotal moment where the industry moves away
- DevOps

Organizations in 2026 have moved beyond basic automation to embrace complex platform engineering models that prioritize developer experience alongside system stability. The current landscape of software delivery demands a sophisticated blend of technical mastery and cultural alignment to manage the
Browse Different Divisions
Popular Stories
Uncover What’s Next