Cyber Security
- Cyber Security

Modern cybersecurity is no longer just a battle of wits between hackers and researchers but has transformed into a high-stakes competition of automated logic where the smallest error can lead to a catastrophic breach. While large language models once promised
- Cyber Security

Modern cybersecurity is no longer just a battle of wits between hackers and researchers but has transformed into a high-stakes competition of automated logic where the smallest error can lead to a catastrophic breach. While large language models once promised
Popular Stories
- Cyber Security

The digital boundaries that separate one website from another are far more fragile than most users realize, as evidenced by a recent vulnerability discovery within the heart of the Apple software ecosystem. Security researchers identified a critical weakness in WebKit,
Deeper Sections Await
- Cyber Security
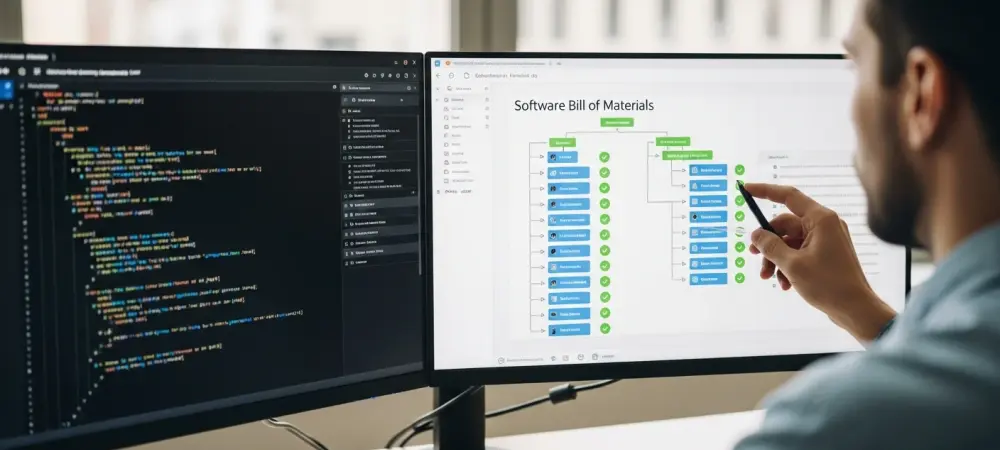
With a tsunami of new software vulnerabilities on the horizon, the old ways of managing cybersecurity are becoming obsolete. We sat down with Dominic Jainy, an IT professional with deep expertise in leveraging technology for security, to unpack a recent
- Cyber Security

The ubiquitous office phone, a seemingly simple device for communication, has evolved into a sophisticated piece of network technology that can unfortunately harbor significant security risks if not properly managed. This article addresses a critical vulnerability discovered in certain Grandstream
Browse Different Divisions
- Cyber Security
With a tsunami of new software vulnerabilities on the horizon, the old ways of managing cybersecurity are becoming obsolete. We sat down with Dominic Jainy, an IT professional with deep expertise in leveraging technology for security, to unpack a recent
- Cyber Security

We’re joined today by Dominic Jainy, an IT professional with deep expertise in artificial intelligence and machine learning. We’ll be exploring a chilling new development at the intersection of AI and cybersecurity: the weaponization of popular AI assistants as stealthy
- Cyber Security
A trusted tool used by millions, Notepad++, recently became the latest vector for a sophisticated state-sponsored cyberattack, highlighting the chilling reality that the software people rely on can be turned against them. This incident is not an anomaly but a
- Cyber Security
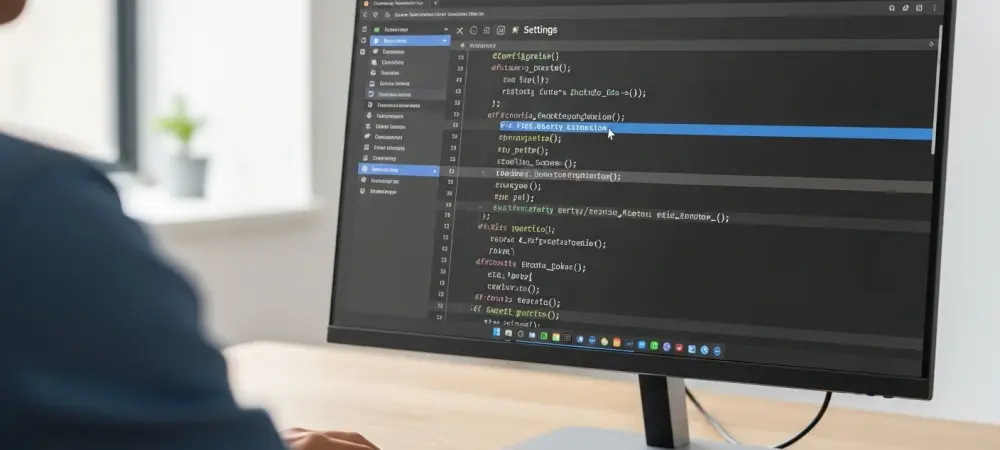
The very development environments meticulously crafted by software engineers to build secure applications have been identified as a significant attack vector, fundamentally challenging the trust placed in everyday tools. Recent findings from cybersecurity researchers have brought a sobering reality to
- Cyber Security
The digital battlefield just became more complex as federal cybersecurity authorities have officially confirmed that four new vulnerabilities, ranging from modern browser flaws to decade-old system weaknesses, are actively being used in attacks. The U.S. Cybersecurity and Infrastructure Security Agency
- Cyber Security

The ubiquitous office phone, a seemingly simple device for communication, has evolved into a sophisticated piece of network technology that can unfortunately harbor significant security risks if not properly managed. This article addresses a critical vulnerability discovered in certain Grandstream
Browse Different Divisions
Popular Stories
Uncover What’s Next

















