Cyber Security
- Cyber Security

Beyond the headlines of conventional warfare, a persistent and clandestine conflict is unfolding across global networks, where nations deploy sophisticated digital operatives to harvest intelligence and secure geopolitical dominance. This escalating shadow war in cyberspace poses a direct and formidable
- Cyber Security

Beyond the headlines of conventional warfare, a persistent and clandestine conflict is unfolding across global networks, where nations deploy sophisticated digital operatives to harvest intelligence and secure geopolitical dominance. This escalating shadow war in cyberspace poses a direct and formidable
Popular Stories
- Cyber Security

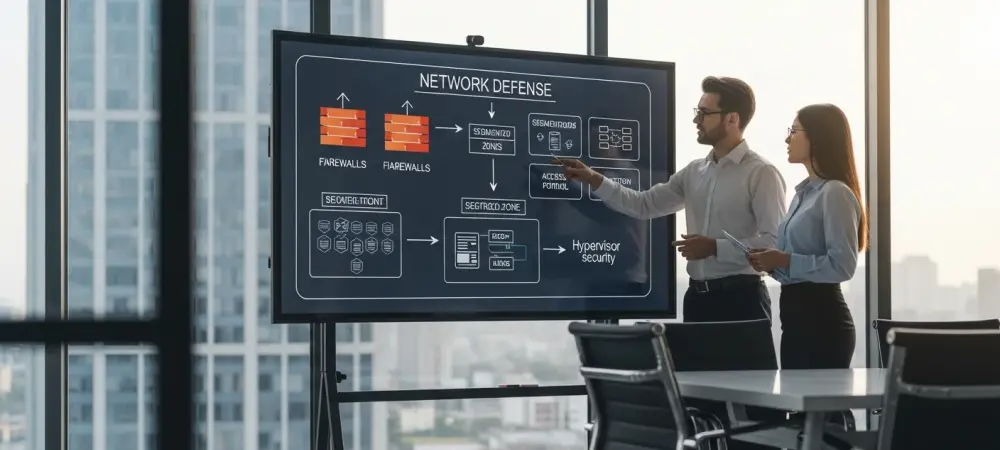
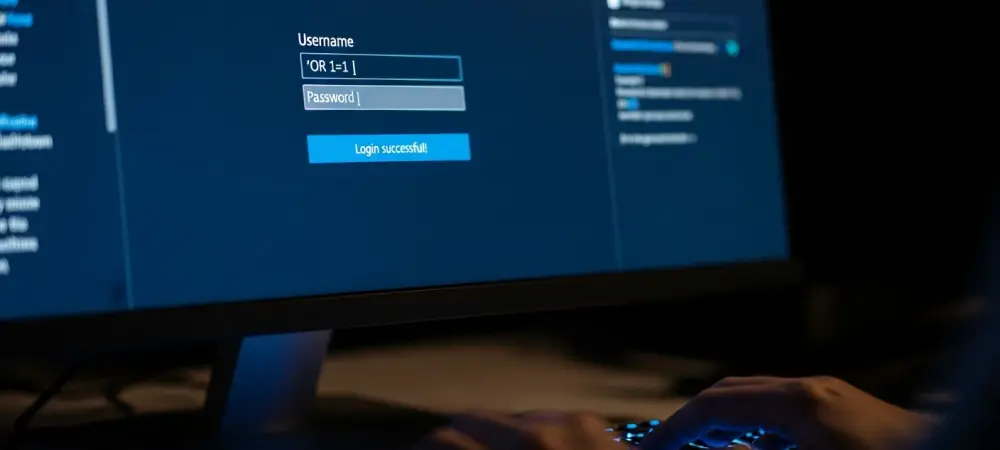
The cybersecurity industry’s relentless pursuit of artificial intelligence and next-generation defenses often overshadows a stark and inconvenient truth: the most damaging breaches still exploit the most elementary security gaps. In an increasingly chaotic and complex threat landscape, a significant strategic
Deeper Sections Await
- Cyber Security

Introduction to a Digital Threat Landscape Imagine a world where over 7,100 GeoServer instances across 99 countries are silently exploited, funneling bandwidth for malicious gain, while 40,000 IoT devices relay attack traffic without their owners’ knowledge, painting a grim picture
- Cyber Security

I’m thrilled to sit down with Dominic Jainy, a seasoned IT professional whose deep expertise in artificial intelligence, machine learning, and blockchain offers a unique perspective on the ever-evolving world of cybersecurity. Today, we’re diving into the dramatic shifts in
Browse Different Divisions
- Cyber Security

Introduction to a Digital Threat Landscape Imagine a world where over 7,100 GeoServer instances across 99 countries are silently exploited, funneling bandwidth for malicious gain, while 40,000 IoT devices relay attack traffic without their owners’ knowledge, painting a grim picture
- Cyber Security

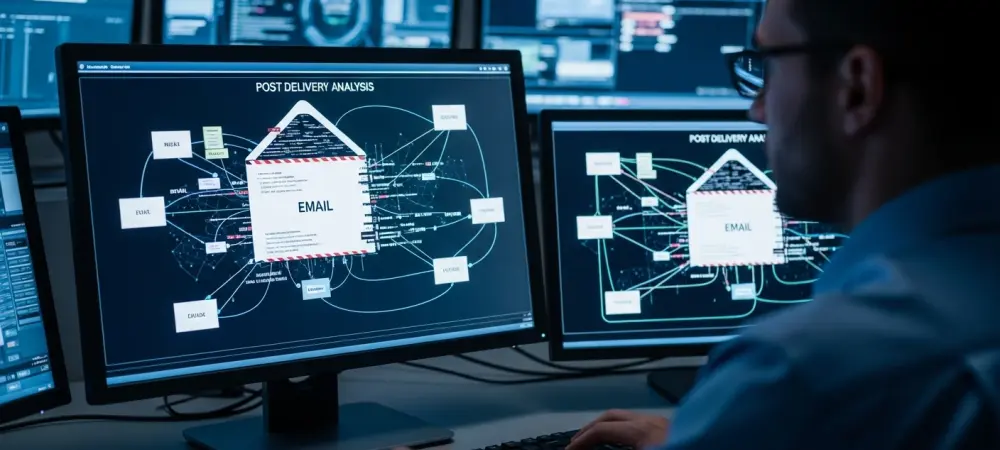
In an increasingly digital world, phishing attacks have reached unprecedented levels of sophistication, with cybercriminals leveraging cutting-edge technology to deceive even the most cautious users. A striking example emerged recently when threat actors targeted Brazilian citizens by creating near-perfect replicas
- Cyber Security

Imagine a scenario where a single misconfiguration in a widely used development tool could allow attackers to break free from isolated environments and seize control of an entire system, posing a severe threat to digital security. This isn’t a hypothetical
- Cyber Security
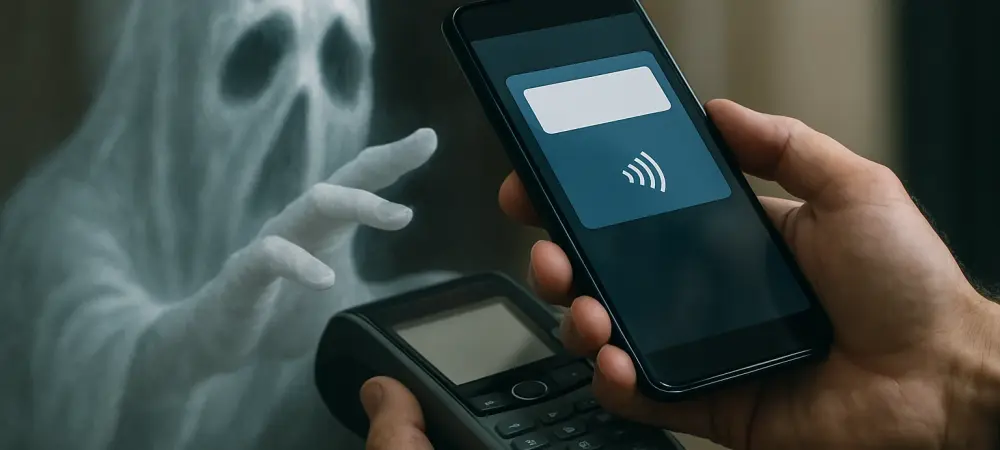
Imagine walking into a store, tapping a phone to make a quick contactless payment, only to later discover that the transaction was made with stolen card data by a cybercriminal halfway across the world. This alarming scenario is becoming a
- Cyber Security

Introduction Imagine managing a WordPress site, pouring effort into content and design, only to discover that a single plugin flaw could hand over complete control to a malicious attacker. This alarming reality has surfaced with a critical vulnerability in the
- Cyber Security

I’m thrilled to sit down with Dominic Jainy, a seasoned IT professional whose deep expertise in artificial intelligence, machine learning, and blockchain offers a unique perspective on the ever-evolving world of cybersecurity. Today, we’re diving into the dramatic shifts in
Browse Different Divisions
Popular Stories
Uncover What’s Next