Cyber Security
- Cyber Security

The recent confirmation of a sophisticated network intrusion at Medtronic has sent ripples through the medical technology sector, highlighting the persistent vulnerability of critical healthcare infrastructure in an increasingly digital world. This specific incident came to light after the notorious
- Cyber Security

The recent confirmation of a sophisticated network intrusion at Medtronic has sent ripples through the medical technology sector, highlighting the persistent vulnerability of critical healthcare infrastructure in an increasingly digital world. This specific incident came to light after the notorious
Popular Stories
- Cyber Security

The recent confirmation of a sophisticated network intrusion at Medtronic has sent ripples through the medical technology sector, highlighting the persistent vulnerability of critical healthcare infrastructure in an increasingly digital world. This specific incident came to light after the notorious
Deeper Sections Await
- Cyber Security

The prevailing tension between Chief Information Security Officers and financial executives often stems from the inherent difficulty in translating defensive metrics into the language of fiscal performance and enterprise value. While a Security Operations Center serves as the primary line
- Cyber Security

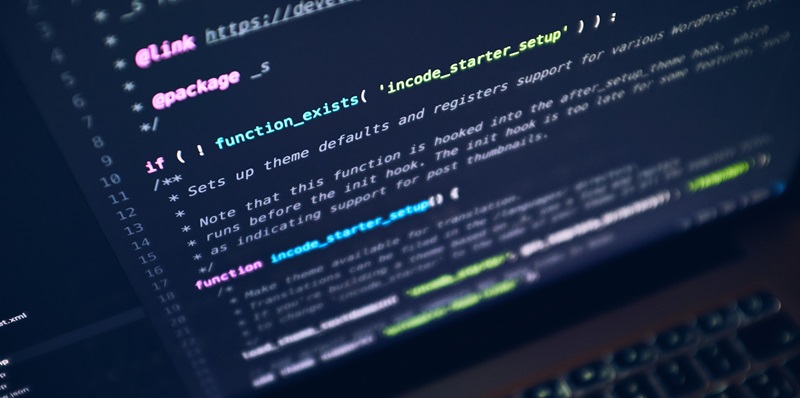
The digital architecture of a modern enterprise relies on the silent, robust performance of middleware, yet a single cryptographic oversight can leave the most secure networks exposed to prying eyes. Apache Tomcat, a foundational element for Java-based web environments, has
Browse Different Divisions
- Cyber Security

The prevailing tension between Chief Information Security Officers and financial executives often stems from the inherent difficulty in translating defensive metrics into the language of fiscal performance and enterprise value. While a Security Operations Center serves as the primary line
- Cyber Security
The architecture of the modern internet relies heavily on the silent efficiency of high-performance web servers, yet the sudden divergence of the Nginx ecosystem has introduced a complex duality that every system administrator must now navigate. Following the pivotal April
- Cyber Security

The rapid weaponization of newly disclosed security flaws represents one of the most significant challenges facing modern cybersecurity operations during the current landscape of 2026. This reality became starkly apparent following the emergence of CVE-2026-39987, a critical pre-authentication remote code
- Cyber Security

The discovery of a critical security vulnerability within the widely used Axios HTTP client has sent ripples through the software development community, highlighting the fragile nature of modern cloud-native architectures. This flaw, identified as CVE-2026-40175, resides deep within the lib/adapters/http.js
- Cyber Security
The modern cybersecurity perimeter is no longer a physical wall but a complex web of trust where the very tools used to build software are being turned into instruments of digital destruction. Within this landscape, a seemingly mundane utility known
- Cyber Security

The digital architecture of a modern enterprise relies on the silent, robust performance of middleware, yet a single cryptographic oversight can leave the most secure networks exposed to prying eyes. Apache Tomcat, a foundational element for Java-based web environments, has
Browse Different Divisions
Popular Stories
Uncover What’s Next