Cyber Security
- Cyber Security

Modern security operations now rely on a delicate web of interconnected applications where a single failure in identity validation can collapse the entire defensive perimeter of a global enterprise. As organizations rush to unify their communication channels with automated response
- Cyber Security

Modern security operations now rely on a delicate web of interconnected applications where a single failure in identity validation can collapse the entire defensive perimeter of a global enterprise. As organizations rush to unify their communication channels with automated response
Popular Stories
- Cyber Security
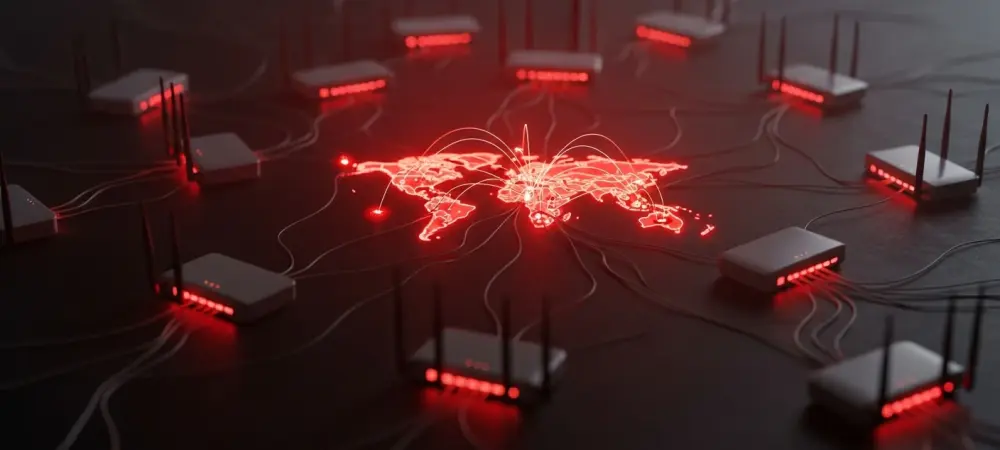
While traditional corporate firewalls remain formidable barriers, state-sponsored cyber operatives have discovered that the humblest pieces of hardware in a remote employee’s home often serve as the most effective backdoors into secure government and commercial networks. This realization has fueled
Deeper Sections Await
- Cyber Security

In a chilling development for global cybersecurity, a sophisticated cyber espionage campaign has emerged, specifically targeting personnel in the defense sector with a focus on Special Operations Command and unmanned aerial vehicle operations. This state-sponsored attack, uncovered by vigilant researchers,
- Cyber Security

In an era where mobile scams and fraud have surged to unprecedented levels, with billions lost annually to phishing texts and fraudulent calls, the urgency for robust smartphone security has never been more apparent. Smartphones are no longer just communication
Browse Different Divisions
- Cyber Security

In a chilling development for global cybersecurity, a sophisticated cyber espionage campaign has emerged, specifically targeting personnel in the defense sector with a focus on Special Operations Command and unmanned aerial vehicle operations. This state-sponsored attack, uncovered by vigilant researchers,
- Cyber Security

In a world where artificial intelligence powers everything from daily queries to critical business decisions, a chilling vulnerability has emerged that could jeopardize user privacy. Imagine this: a simple search for a dinner recipe on ChatGPT might silently expose personal
- Cyber Security

In an era where digital tools shape political landscapes, a staggering reality emerges: sophisticated spyware can infiltrate the most guarded communications of influential figures without a trace, posing a severe risk to privacy and security. Consider the case of a
- Cyber Security

In a startling revelation, a recent report uncovered that over 60% of stolen credentials found in infostealer logs are tied to social media accounts, with LinkedIn emerging as a key target for cybercriminals. This alarming statistic underscores a growing menace
- Cyber Security

Introduction In an era where digital collaboration tools are integral to software development, a recent discovery of multiple security vulnerabilities in a leading platform has sent ripples through the tech community, raising serious concerns about data protection and system integrity.
- Cyber Security

In an era where mobile scams and fraud have surged to unprecedented levels, with billions lost annually to phishing texts and fraudulent calls, the urgency for robust smartphone security has never been more apparent. Smartphones are no longer just communication
Browse Different Divisions
Popular Stories
Uncover What’s Next