Cyber Security
- Cyber Security

The digital boundaries that separate one website from another are far more fragile than most users realize, as evidenced by a recent vulnerability discovery within the heart of the Apple software ecosystem. Security researchers identified a critical weakness in WebKit,
- Cyber Security

The digital boundaries that separate one website from another are far more fragile than most users realize, as evidenced by a recent vulnerability discovery within the heart of the Apple software ecosystem. Security researchers identified a critical weakness in WebKit,
Popular Stories
- Cyber Security

The digital boundaries that separate one website from another are far more fragile than most users realize, as evidenced by a recent vulnerability discovery within the heart of the Apple software ecosystem. Security researchers identified a critical weakness in WebKit,
Deeper Sections Await
- Cyber Security

The rapid proliferation of internet-connected surveillance across global critical infrastructure has created a significant paradox where the very tools designed to ensure security have become primary vectors for sophisticated aggression. Recent intelligence confirms that threat actors linked to Iran have
- Cyber Security

Dominic Jainy stands at the forefront of the technological intersection where artificial intelligence meets robust cybersecurity infrastructure. With a deep background in machine learning and blockchain, he has dedicated his career to understanding how autonomous systems can safeguard the digital
Browse Different Divisions
- Cyber Security

The rapid proliferation of internet-connected surveillance across global critical infrastructure has created a significant paradox where the very tools designed to ensure security have become primary vectors for sophisticated aggression. Recent intelligence confirms that threat actors linked to Iran have
- Cyber Security

The traditional image of a lone, elite hacker meticulously crafting a single “zero-day” exploit has been replaced by a digital assembly line where generative models churn out malicious code by the thousands. This transition marks the industrialization of cyber warfare,
- Cyber Security
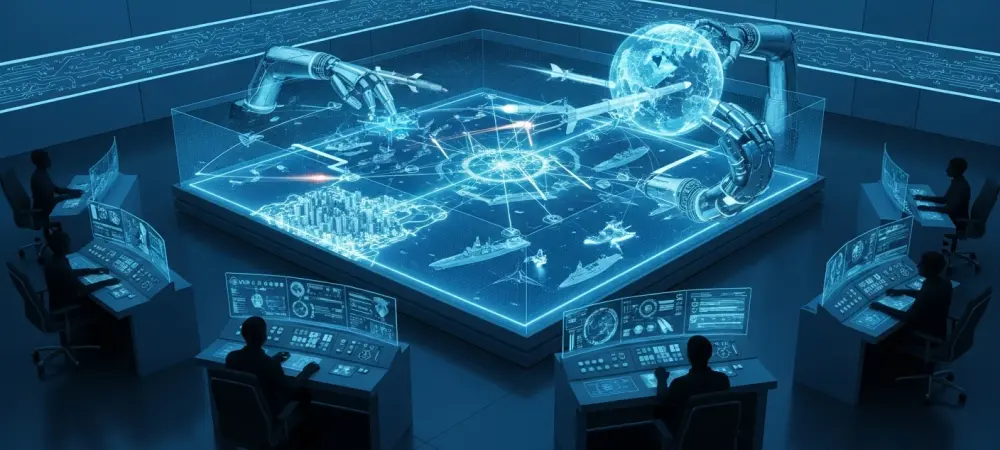
The modern battlefield has transcended the traditional physical realm, transforming every unsecured network switch and surveillance feed into a tactical asset for long-range precision strikes. This evolution marks a fundamental departure from the era when digital and physical operations existed
- Cyber Security

The digital battleground is currently witnessing a profound transformation as the Iranian threat actor known as MuddyWater, or Seedworm, orchestrates a series of highly targeted intrusions against global critical infrastructure. Officially linked to the Iranian Ministry of Intelligence and Security,
- Cyber Security

The recent collaboration between Anthropic and Mozilla has demonstrated that large language models are no longer just creative assistants but have become formidable assets in the high-stakes world of cybersecurity. By scanning thousands of complex C++ files in a fraction
- Cyber Security

Dominic Jainy stands at the forefront of the technological intersection where artificial intelligence meets robust cybersecurity infrastructure. With a deep background in machine learning and blockchain, he has dedicated his career to understanding how autonomous systems can safeguard the digital
Browse Different Divisions
Popular Stories
Uncover What’s Next

















