Cyber Security
- Cyber Security

The traditional perception of state-sponsored hacking as a series of isolated operations is rapidly dissolving into a reality of highly integrated, resource-sharing networks. Security researchers have spent the last few years observing a paradigm shift where Chinese threat clusters no
- Cyber Security

The traditional perception of state-sponsored hacking as a series of isolated operations is rapidly dissolving into a reality of highly integrated, resource-sharing networks. Security researchers have spent the last few years observing a paradigm shift where Chinese threat clusters no
Popular Stories
- Cyber Security

The recent confirmation of a sophisticated network intrusion at Medtronic has sent ripples through the medical technology sector, highlighting the persistent vulnerability of critical healthcare infrastructure in an increasingly digital world. This specific incident came to light after the notorious
Deeper Sections Await
- Cyber Security

In the intricate world of enterprise cybersecurity, the Security Information and Event Management (SIEM) system stands as the central nervous system, a vigilant sentinel tasked with observing, correlating, and reporting on the endless stream of digital activity across a network.
- Cyber Security

A newly disclosed vulnerability within a core Windows utility highlights a subtle but significant danger, demonstrating how even trusted operating system components can be subverted to dismantle critical security defenses. Identified as CVE-2026-20824, this security feature bypass flaw resides in
Browse Different Divisions
- Cyber Security

In the intricate world of enterprise cybersecurity, the Security Information and Event Management (SIEM) system stands as the central nervous system, a vigilant sentinel tasked with observing, correlating, and reporting on the endless stream of digital activity across a network.
- Cyber Security

The digital battlefield’s clock ticks in microseconds, a pace at which human-led security teams, despite their expertise, are increasingly outmatched by the relentless speed and scale of automated threats. In this environment, traditional, human-led penetration testing struggles to keep pace,
- Cyber Security
The cybersecurity industry has become locked in a high-stakes technological arms race, with defenders deploying increasingly complex AI algorithms to counter adversaries who are, in turn, weaponizing AI to orchestrate more sophisticated and evasive attacks. This escalating cycle of AI
- Cyber Security
The very tools designed to secure and manage complex cloud environments can sometimes become the weakest link, creating a direct pathway for a catastrophic breach that bypasses carefully constructed defenses. A recently discovered vulnerability demonstrates how the trust placed in
- Cyber Security
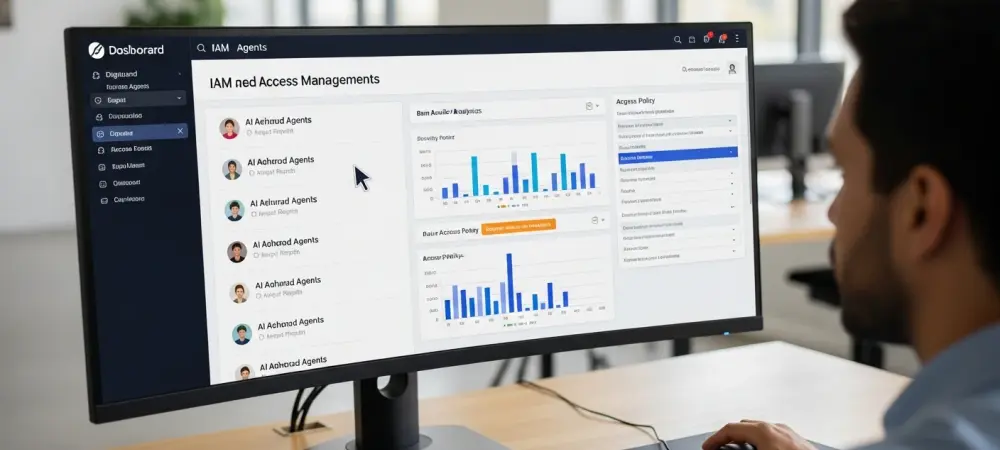
With the rapid integration of autonomous AI into corporate environments, the security landscape is undergoing a seismic shift. We are joined by Dominic Jainy, a veteran IT professional specializing in artificial intelligence and machine learning, to explore the emerging challenges
- Cyber Security

A newly disclosed vulnerability within a core Windows utility highlights a subtle but significant danger, demonstrating how even trusted operating system components can be subverted to dismantle critical security defenses. Identified as CVE-2026-20824, this security feature bypass flaw resides in
Browse Different Divisions
Popular Stories
Uncover What’s Next