Cyber Security
- Cyber Security

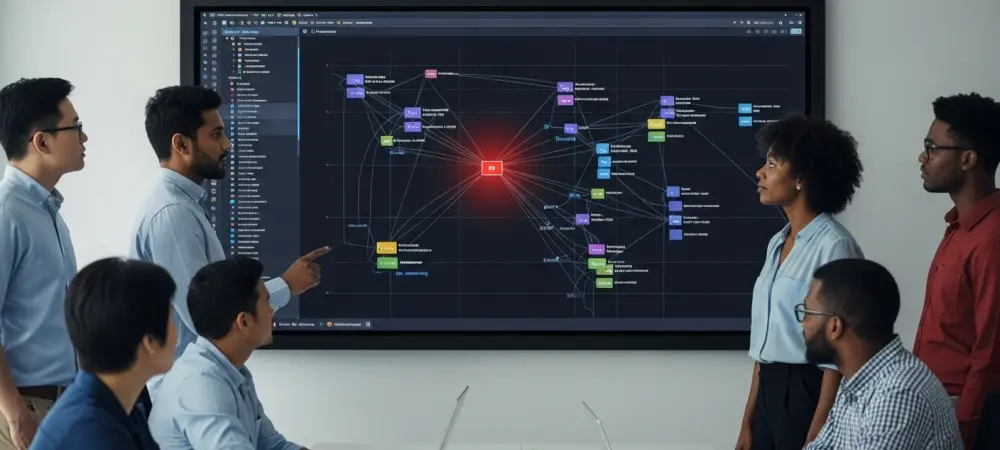
The traditional perception of state-sponsored hacking as a series of isolated operations is rapidly dissolving into a reality of highly integrated, resource-sharing networks. Security researchers have spent the last few years observing a paradigm shift where Chinese threat clusters no
- Cyber Security

The traditional perception of state-sponsored hacking as a series of isolated operations is rapidly dissolving into a reality of highly integrated, resource-sharing networks. Security researchers have spent the last few years observing a paradigm shift where Chinese threat clusters no
Popular Stories
- Cyber Security

The recent confirmation of a sophisticated network intrusion at Medtronic has sent ripples through the medical technology sector, highlighting the persistent vulnerability of critical healthcare infrastructure in an increasingly digital world. This specific incident came to light after the notorious
Deeper Sections Await
- Cyber Security

A scrambled screen and a jittery mouse cursor are no longer just signs of a system malfunction; they are the sophisticated bait in a new generation of cyberattacks designed to turn a user’s panic into a vector for infection. This
- Cyber Security

A seemingly harmless string of text, sent over a decades-old protocol, has emerged as the key to unlocking complete control over countless servers and bypassing all authentication measures in a flaw that lay dormant for over a decade. A critical
Browse Different Divisions
- Cyber Security

A scrambled screen and a jittery mouse cursor are no longer just signs of a system malfunction; they are the sophisticated bait in a new generation of cyberattacks designed to turn a user’s panic into a vector for infection. This
- Cyber Security

The digital infrastructure powering modern software development is a prime target for malicious actors, and a new security advisory from GitLab underscores the critical need for vigilance among system administrators. GitLab has released an urgent security update for its self-managed
- Cyber Security

Unpacking the Latest High-Stakes Vulnerabilities The seamless connectivity that powers modern hybrid work environments also introduces pathways for sophisticated cyber threats, forcing a constant reevaluation of digital security postures. This research summary examines critical security updates recently issued by Zoom
- Cyber Security
The immense convenience of pulling a ready-made package from the npm registry often overshadows the critical security question of whether that third-party code can be leveraged to execute arbitrary code within a Node.js application. Focusing on a real-world case study
- Cyber Security

The seemingly harmless web management interface on your unified communications system could be an unlocked back door for an attacker, thanks to a newly discovered and actively exploited vulnerability that demands the immediate attention of system administrators. In response to
- Cyber Security

A seemingly harmless string of text, sent over a decades-old protocol, has emerged as the key to unlocking complete control over countless servers and bypassing all authentication measures in a flaw that lay dormant for over a decade. A critical
Browse Different Divisions
Popular Stories
Uncover What’s Next



















