Cyber Security
- Cyber Security

Dominic Jainy is a seasoned IT professional with deep technical roots in artificial intelligence and blockchain, though his foundational expertise in kernel architecture makes him a vital voice in the cybersecurity space. With years of experience analyzing how complex systems
- Cyber Security

Dominic Jainy is a seasoned IT professional with deep technical roots in artificial intelligence and blockchain, though his foundational expertise in kernel architecture makes him a vital voice in the cybersecurity space. With years of experience analyzing how complex systems
Popular Stories
- Cyber Security

The recent confirmation of a sophisticated network intrusion at Medtronic has sent ripples through the medical technology sector, highlighting the persistent vulnerability of critical healthcare infrastructure in an increasingly digital world. This specific incident came to light after the notorious
Deeper Sections Await
- Cyber Security
Modern software development environments frequently rely on third-party dependencies that can inadvertently introduce devastating vulnerabilities into even the most securely designed enterprise applications. This guide provides a comprehensive analysis of how sophisticated supply chain attacks target the .NET ecosystem to
- Cyber Security

The rapid integration of large language models into the standard toolkit of international hacking collectives has fundamentally altered the velocity at which digital infrastructure is compromised today. Throughout the recent calendar year, global security observers documented a staggering 89% increase
Browse Different Divisions
- Cyber Security
Modern software development environments frequently rely on third-party dependencies that can inadvertently introduce devastating vulnerabilities into even the most securely designed enterprise applications. This guide provides a comprehensive analysis of how sophisticated supply chain attacks target the .NET ecosystem to
- Cyber Security

A single command executed in a terminal can bridge the gap between a productive afternoon and a total corporate security collapse, especially when the malicious actor is hiding in plain sight. The simple command npm install is a routine part
- Cyber Security

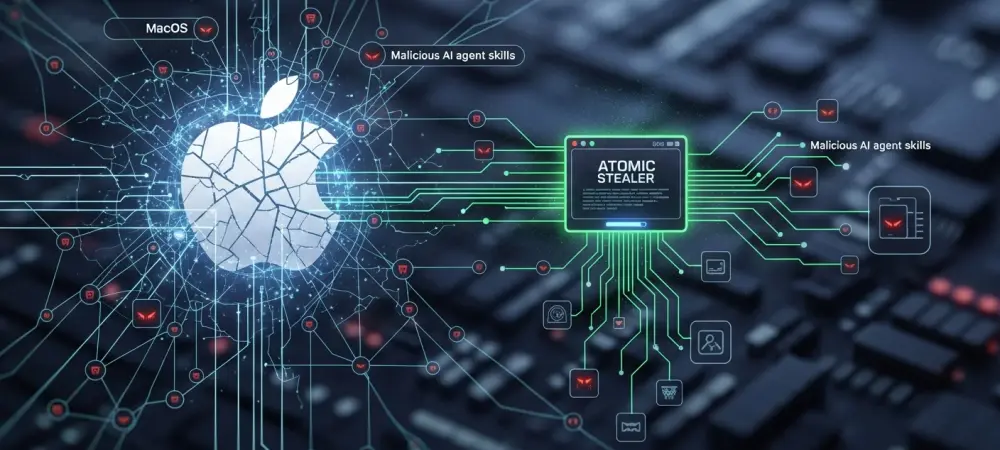
The inherent trust that users place in reputable cybersecurity software has become a primary target for sophisticated threat actors who leverage the very tools designed for protection to facilitate malicious infections. In a recent trend observed throughout 2026, the Chinese-speaking
- Cyber Security

The Emergence of Targeted Cyber Threats in the Supply Chain The global logistics industry has evolved into a hyper-connected network where the physical movement of cargo is now entirely inseparable from the complex digital systems that manage international freight flow.
- Cyber Security
Dominic Jainy is a distinguished IT professional with a deep mastery of artificial intelligence, machine learning, and blockchain technologies. With a career dedicated to exploring how these advanced systems intersect with real-world infrastructure, he provides critical insights into the evolving
- Cyber Security

The rapid integration of large language models into the standard toolkit of international hacking collectives has fundamentally altered the velocity at which digital infrastructure is compromised today. Throughout the recent calendar year, global security observers documented a staggering 89% increase
Browse Different Divisions
Popular Stories
Uncover What’s Next


















