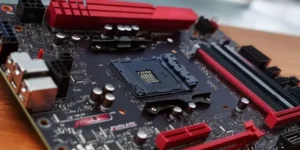
As the tech world gears up for the highly anticipated CES event, MSI is set to unveil its latest lineup of budget-friendly motherboards, targeting both Intel and AMD CPU platforms. These upcoming motherboards are particularly significant as they cater to users looking for high-quality yet cost-effective options. With Intel’s budget-focused Arrow Lake chips and AMD’s high-end Ryzen 9000X3D CPUs in