The vast and interconnected ecosystem of WordPress plugins offers incredible functionality, but it also conceals a landscape where a single unsanitized parameter can jeopardize tens of thousands of websites. A critical SQL injection vulnerability, identified as CVE-2025-67987, affecting the popular Quiz and Survey Master plugin, serves as a powerful case study. This review will explore its technical underpinnings, the remediation process, and its broader implications for developers and site administrators. The purpose is to provide a thorough understanding of this specific vulnerability, highlighting its impact and the lessons it offers for security practices.
An Overview of the QSM Plugin Vulnerability
The core security flaw discovered late last year in the Quiz and Survey Master (QSM) WordPress plugin created a significant risk for its extensive user base. Affecting over 40,000 websites, the vulnerability allowed authenticated users with minimal permissions, such as Subscribers, to execute arbitrary SQL commands. This capability could lead to data theft, content manipulation, or a complete site compromise.
Its emergence is not an isolated incident but rather a reflection of the ongoing security challenges within the vast third-party plugin ecosystem. The flaw underscores the critical need for developers to adhere to secure coding practices, as even a seemingly minor oversight can create a widespread and dangerous attack vector. For site owners, it highlights the importance of a proactive security posture.
Technical Anatomy of the SQL Injection Flaw
The Unsanitized Input Vector
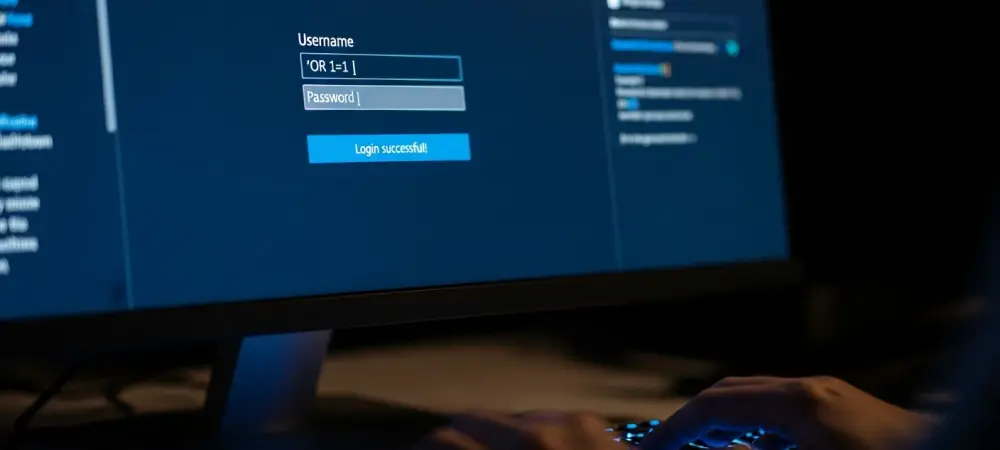
At the heart of the vulnerability was the failure to properly sanitize user-supplied data within a specific API function. The plugin included a REST API endpoint designed to fetch quiz information, which accepted a parameter named is_linking. The value provided to this parameter was directly incorporated into a raw SQL query without validation or escaping, creating a direct path for malicious input to reach the database.
This oversight meant that an attacker could inject SQL syntax into the parameter’s value. The database server, unable to distinguish between the intended query structure and the malicious code, would execute the entire command. This provided a simple yet powerful mechanism for manipulating database operations.
The Absence of Prepared Statements
The security flaw was significantly compounded by the development team’s failure to use SQL prepared statements. This fundamental security practice separates the SQL command’s structure from the data being supplied, effectively preventing user input from being misinterpreted as executable code. By not implementing this safeguard, the plugin left the door wide open for injection attacks.
Without the protection of prepared statements, any authenticated user could craft a malicious payload to exploit the unsanitized is_linking parameter. This low barrier to entry made the vulnerability especially dangerous, as it did not require an attacker to first gain elevated privileges.
The Disclosure and Patching Process
The timeline from the vulnerability’s discovery to its resolution demonstrates the value of a coordinated disclosure process. On November 21, 2025, security researcher Doan Dinh Van of the Patchstack Alliance responsibly disclosed the flaw to the plugin vendor. This private communication initiated a swift response from the development team.
This collaboration culminated in the release of Quiz and Survey Master version 10.3.2 on December 4, 2025, just under two weeks later. The patch effectively neutralized the threat by implementing proper data validation, specifically by forcing the is_linking parameter to an integer value. This simple change closed the injection vector and secured the affected sites.
Real-World Impact and Attack Surface
The vulnerability exposed a vast number of WordPress sites to potential data breaches and unauthorized manipulation. With an install base exceeding 40,000, the potential for widespread damage was considerable. Because the flaw was exploitable by any authenticated user, the attack surface was exceptionally broad, removing the need for an attacker to escalate privileges.
Although there is no public evidence of this specific vulnerability being exploited in the wild, its potential impact remained severe. An attacker could have extracted sensitive user information, altered site content, or created new administrative accounts. The incident serves as a stark reminder that the severity of a vulnerability is determined not only by its technical nature but also by the ease with which it can be exploited.
Broader Implications and Development Challenges
This incident is a critical reminder of the security challenges inherent in an open and extensible platform like WordPress. It underscores the perpetual risk posed by third-party plugins and reinforces the non-negotiable importance of implementing fundamental security principles from the outset of development.
The core challenges highlighted by this case include ensuring the consistent adoption of secure coding standards across a diverse community of independent developers. For the ecosystem to become more resilient, practices like robust input validation and the mandatory use of prepared statements must become universal, not optional.
Future Outlook and Preventative Measures
Looking forward, this event emphasizes the need for a multi-layered security approach to protect WordPress environments. For developers, this means prioritizing secure coding education and implementing rigorous code audits as a standard part of the pre-release process. It is no longer sufficient to focus only on functionality; security must be a primary design consideration.
For WordPress administrators, the key lesson is the necessity of diligent site maintenance. This includes the prompt application of all security updates for plugins, themes, and the core platform. Furthermore, deploying a Web Application Firewall (WAF) can provide a valuable additional layer of defense, capable of detecting and blocking many injection-style attacks before they reach the application.
Conclusion: Key Lessons from a Critical Flaw
The review of CVE-2025-67987 provided a clear case study on the mechanics and impact of a classic SQL injection vulnerability within the modern WordPress ecosystem. The incident ultimately highlighted the success of the responsible disclosure model, which enabled a swift and effective resolution before widespread exploitation could occur. However, it also served as a stark reminder of the severe consequences that arose from neglecting basic security hygiene in plugin development. The key takeaway was that robust input validation and the universal use of prepared statements were not optional features but foundational requirements for secure web application development.