A single line of malicious code can now paralyze a multi-billion-dollar production facility faster than any physical mechanical failure or labor strike ever could. As we navigate 2026, the industrial sector finds itself in the crosshairs of a digital gold rush where the “factory of the future” has inadvertently become the favorite target of the modern extortionist. While previous years saw cybercriminals casting wide nets across various industries, the strategy has shifted toward a cold, calculated focus on the production floor. This transition is not accidental; it is a response to the manufacturing industry’s unique combination of high financial stakes and legacy technological vulnerabilities.
The Profitable Intersection: High Pressure and Low Resistance
Cybercriminals have abandoned the scattergun approach of the past in favor of a calculated assessment of the “sweet spot” on the risk-reward spectrum. While an attack on a hospital might trigger a federal manhunt and a strike on a power grid could be seen as an act of war, hitting a factory provides a massive payday with significantly less heat from international law enforcement. In this high-stakes environment, manufacturing has become the preferred ATM for global ransomware syndicates, who recognize that for a plant manager, every hour of a halted assembly line is measured in millions of dollars of lost revenue.
The logic behind this targeting is rooted in the path of least resistance. Attackers have realized that private corporations are often more likely to settle quietly to protect their quarterly earnings than a public institution governed by rigid federal reporting mandates. By focusing on the private production sector, ransomware groups can maintain a lower profile while securing higher payouts, effectively turning the industrial supply chain into a recurring revenue stream for organized crime.
The Strategic Shift: From Public Services to Private Production
Recent data from cybersecurity leaders confirms a definitive shift: manufacturing has overtaken healthcare and finance as the most-targeted global sector. This pivot is driven by the industry’s unique vulnerability profile—a combination of aging infrastructure and a desperate need for constant uptime. Unlike other critical sectors that might receive immediate government intervention, manufacturers often stand alone, making them prime targets for groups who want to maximize financial gain while minimizing their operational footprint.
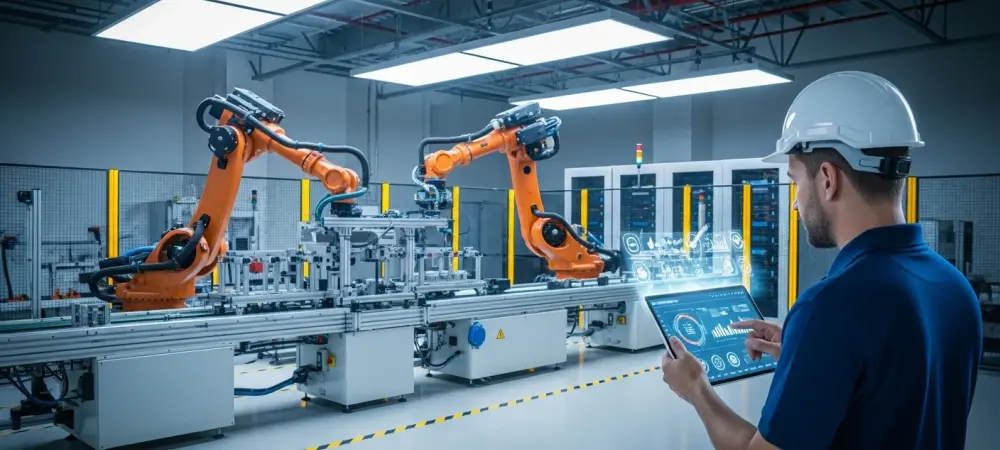
Furthermore, the digital transformation of the factory floor has created a sprawling attack surface that many organizations struggle to monitor. As traditional mechanical systems are connected to the cloud for real-time analytics, the gap between office IT and shop-floor technology narrows. This interconnectedness allows a simple phishing email in the accounting department to potentially escalate into a full-scale shutdown of robotic assembly arms, providing hackers with unprecedented leverage over the entire enterprise.
The Economic Engine: Driving Modern Extortion
The primary catalyst for this surge is the industry’s remarkably low tolerance for downtime, which creates an almost immediate incentive to pay. With median ransom payments now hitting the $1 million mark and some exceeding $5 million, the financial stakes are astronomical. This leverage is amplified by the interconnected nature of global supply chains; as seen in historical incidents where a single breach in a secondary supplier triggered a cascading failure across an entire multi-billion-dollar enterprise, the pressure to resume operations is often overwhelming.
Moreover, the cost of a ransom is frequently dwarfed by the cost of the outage itself. When a facility produces thousands of units per hour, a three-day shutdown can result in losses that take years to recover. Ransomware operators understand these economics perfectly; they time their attacks for maximum disruption, often striking during peak production cycles or just before major delivery deadlines to ensure the victim feels the maximum amount of financial pain.
Beyond the Lock: The Rise of Intellectual Property Theft
The threat landscape is evolving from simple system encryption to sophisticated extortion-only attacks, where the value lies in the data itself rather than the lock on the screen. Manufacturers are being targeted for their crown jewels—proprietary engineering designs, trade secrets, and unique production processes that can be sold to competitors or leaked to ruin a brand’s market position. This shift is particularly dangerous because it bypasses traditional backup strategies; even if a company can restore its systems, it cannot un-steal its most valuable intellectual property.
In this new era of double extortion, the attacker holds the victim’s reputation hostage. Even if a manufacturer has invested in robust recovery protocols, the threat of having sensitive blueprints or client lists published on the dark web creates a secondary crisis. This evolution means that cybersecurity is no longer just about keeping the machines running; it is about defending the very ideas and innovations that give a company its competitive edge in a global market.
The Defensive Bridge: Legacy Hardware and Modern Security
To defend against these threats, organizations began moving security oversight away from general operations and into the hands of specialized Chief Information Security Officers. Success in this environment required a rigorous focus on asset discovery to eliminate unknown security gaps and the implementation of strict network segmentation to prevent attackers from jumping from office emails to factory floor controllers. By hardening legacy systems and enforcing secure remote access for third-party vendors, manufacturers started to close the open doors that had made them easy targets. Proactive firms also adopted an assumed breach mentality, prioritizing detection and response over mere prevention. They integrated automated monitoring tools that could identify anomalous behavior on the network before a full-scale encryption event took place. This shift toward a more resilient architecture ensured that even when a perimeter was breached, the damage remained contained, effectively devaluing the manufacturer as a target for future ransomware campaigns.