As the cyber threat landscape continues to evolve, security researchers have recently made a significant discovery: a new malware variant believed to be associated with the notorious BlueNoroff Advanced Persistent Threat (APT) group. This development has raised concerns due to BlueNoroff’s track record of financially motivated campaigns targeting cryptocurrency exchanges, venture capital firms, and banks. In this article, we delve into the details of this latest malware variant, its connection to BlueNoroff, and its potential implications for cybersecurity.
Background on BlueNoroff
BlueNoroff, a well-known APT group, has gained notoriety for its financially motivated campaigns. Over the years, they have been known to launch targeted attacks against critical entities in the financial sector. Their primary targets include cryptocurrency exchanges, venture capital firms, and banks. These campaigns have been marked by sophisticated infiltration techniques, with the group often employing social engineering tactics to gain unauthorized access to systems.
Discovery of the new malware variant
The spotlight is now on a standalone binary named “ProcessRequest,” which security researchers have identified as a new malware variant associated with BlueNoroff. What makes this discovery even more intriguing is its interaction with a previously flagged domain. What is particularly alarming is that a legitimate cryptocurrency exchange operates under a similar domain, further raising concerns about possible misattributions.
Analysis reveals that the malicious domain, registered in May 2023, resolves to a specific IP address. This finding adds to the urgency surrounding this malware variant and highlights the need for swift action to mitigate potential threats.
Connection to BlueNoroff’s Rustbucket campaign
Further investigation into this new malware variant has uncovered strong similarities with BlueNoroff’s Rustbucket campaign. In this campaign, the APT group assumes the identity of an investor or headhunter to deceive their targets and gain access to their systems. By leveraging social engineering techniques, BlueNoroff exploits the unsuspecting nature of their victims, gradually infiltrating their organizations and securing unauthorized access.
Analysis of the Malware – ObjCShellz
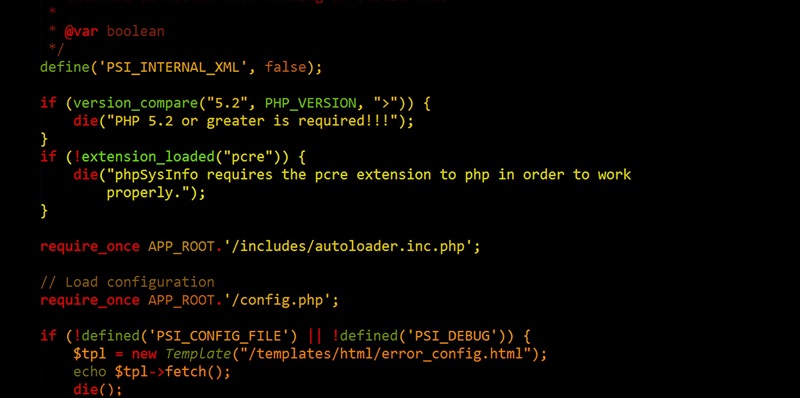
The newly discovered malware variant, aptly named ObjCShellz, exhibits a range of sophisticated features. This malware employs a communication channel with a Command and Control (C2) server, utilizing a POST message to a specific URL. Through this communication, ObjCShellz gathers sensitive information about the infected macOS system while simultaneously constructing a user-agent for seamless and covert communication with the C2 server.
The most notable aspect of this malware is its ability to execute commands, effectively granting remote control to the attackers. This functionality not only allows the APT group to extract valuable data but also provides them with the means to manipulate the compromised system for their nefarious purposes.
Functionality and Potential Impact
Though seemingly simplistic in design, ObjCShellz is remarkably functional and poses a significant threat to targeted systems. Its powerful command execution capabilities make it a potent tool in the hands of the BlueNoroff APT group. With remote control at their disposal, the attackers can exfiltrate critical information, disrupt operations, or even plant further malware within compromised networks.
Assessment of the malware’s delivery mechanism
Based on the expertise and past strategies of BlueNoroff, it is highly likely that this newly discovered malware variant is a late stage within a multi-stage malware delivery system. It is suspected that social engineering methods have been utilized to entice unsuspecting victims into downloading or executing the initial payload, which subsequently leads to the installation of ObjCShellz.
The identification of this new malware variant associated with BlueNoroff holds significant implications for cybersecurity efforts worldwide. The financially motivated campaigns by this APT group have already caused substantial damage. With the discovery of ObjCShellz, organizations must remain vigilant and adopt robust security measures to combat the ever-evolving cyber threats.
As the battle against cybercriminals intensifies, it is crucial for security researchers, organizations, and individuals to collaborate and share information to stay one step ahead. Proactive measures, such as regularly updating security systems, educating on social engineering techniques, and implementing multifactor authentication, can go a long way in thwarting the attacks of groups like BlueNoroff. Ultimately, a unified approach is key to protecting our digital ecosystems from the growing threats that lurk in the shadows.