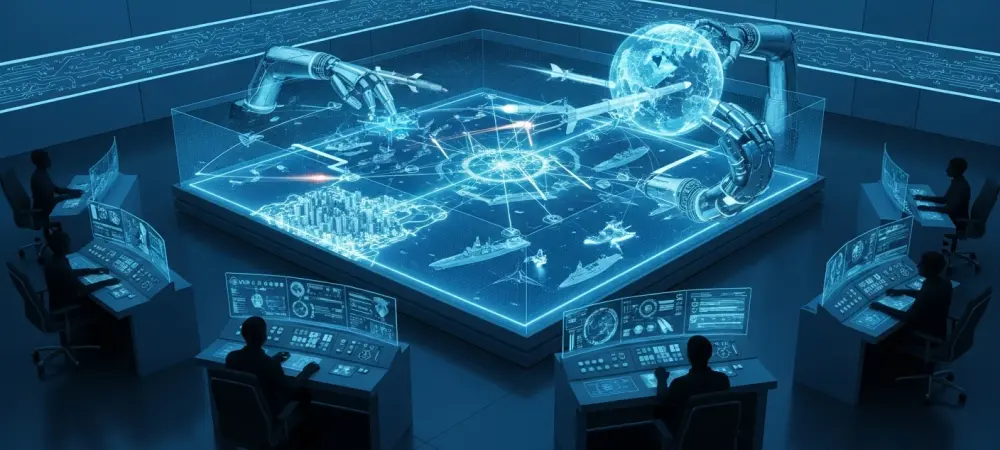
The modern battlefield has transcended the traditional physical realm, transforming every unsecured network switch and surveillance feed into a tactical asset for long-range precision strikes. This evolution marks a fundamental departure from the era when digital and physical operations existed in silos, often managed by disparate commands with varying objectives. Today, the doctrine of unified cyber-kinetic warfare has matured into a singular offensive framework where the distinction between a line of code and a missile trajectory has all but vanished. This shift is most evident in the recent strategic maneuvers observed across the Middle East, where digital intrusions now serve as the primary sensory input for kinetic engagements.
The Convergence of Digital and Physical Combat
Statistical Indicators and Emerging Patterns of Integration
Data compiled by Check Point Research and Flashpoint reveals a stark increase in the coordination between state-sponsored cyber actors and conventional military units. Since the major military exchanges of early 2025, there has been a documented surge in Iranian activity that demonstrates a sophisticated blending of these domains. CrowdStrike reports indicate that cyber operations are no longer merely preparatory; they are now deeply integrated into the live execution of strikes. This transition suggests that military planners now view the digital environment as a persistent, high-fidelity extension of their physical reconnaissance and targeting capabilities.
Furthermore, the exploitation of Internet Protocol (IP) camera vulnerabilities has seen an unprecedented growth trend. Specifically, surveillance systems manufactured by Hikvision and Dahua have become primary targets across a broad geographical arc including Israel, Qatar, Bahrain, the UAE, and Cyprus. This is not a random act of digital vandalism but a calculated effort to build a real-time observation network. Correlation statistics suggest that unauthorized network access frequently precedes missile launches by mere minutes, providing the necessary data for real-time targeting correction and immediate Battle Damage Assessment.
Real-World Applications and Case Studies in Modern Conflict
The effectiveness of this doctrine was underscored during the missile strikes of 2025, where compromised IP cameras provided the primary visual confirmation for impact verification. Technical investigations into these incidents identified the widespread exploitation of specific vulnerabilities, including CVE-2017-7921, CVE-2021-36260, and the more recent CVE-2025-34067. By seizing control of these feeds, offensive actors bypassed traditional satellite-based intelligence cycles, allowing for an agile and responsive targeting loop that outpaced conventional defensive responses.
Beyond direct military targeting, the scope of these operations has expanded to include logistics and critical infrastructure sabotage. A notable example involved the breach of the Jordan Silos and Supply General Company, where a phishing campaign led to a significant disruption of food supply logistics. Additionally, the emergence of “Operation Epic Fury” demonstrated the international reach of this doctrine. Pro-Iranian Russian hacktivists targeted American SCADA systems and CCTV networks, signaling that the unified cyber-kinetic approach is being exported to allies, creating a global network of interconnected threats that target both military and civilian infrastructure.
Industry Perspectives on the Multidomain Blueprint
Strategic analysts point toward the total collapse of traditional linear conflict boundaries as the most significant outcome of this new warfare blueprint. In this hybrid environment, cyber operations are frequently deployed to “blind” air defense sensors immediately before a kinetic strike. This technique creates a window of vulnerability that conventional systems struggle to close, as the defensive response is often delayed by the need to troubleshoot a digital failure while simultaneously reacting to a physical threat. Expert commentary suggests that this synchronization is the hallmark of modern multidomain strategy.
From an economic perspective, threat intelligence specialists highlight the psychological and financial impact of these combined operations. The disruption of global shipping routes through digital interference, coupled with the physical threat of drone or missile strikes, has caused insurance risks to skyrocket. This dual-threat model serves as a force multiplier, where code-based intelligence significantly enhances the lethality and efficiency of conventional military assets. The result is a highly effective method of coercion that targets an adversary’s national resolve and economic stability concurrently.
Future Projections and Global Security Implications
The new blueprint for conflict suggests a future where every connected device serves as a potential military scout, effectively turning civilian infrastructure against the population it was meant to serve. This realization has sparked a re-evaluation of security protocols for the Internet of Things (IoT) environment. The potential for more destructive operations is increasing, shifting from simple service disruption toward efforts aimed at causing permanent, irreparable damage to critical infrastructure. As state actors refine their capabilities, the threshold for what constitutes a “kinetic” act is becoming increasingly blurred.
One of the most concerning aspects of this evolution is the “Fog of War” strategy, where the information environment is flooded with contradictory data to overwhelm decision-makers. By combining high-speed physical strikes with a deluge of digital misinformation and sensor manipulation, aggressors can paralyze defensive command structures. Western defense sectors currently face the monumental challenge of securing fragmented IoT environments and lagging update cycles against state-actor exploitation. The “code and cordite” doctrine is no longer a peripheral threat; it has become the standard operating procedure for global powers and their proxies.
Strategic Summary and the Path Forward
The synthesis of the unified cyber-kinetic doctrine fundamentally redefined the modern battlefield beyond the constraints of physical geography. It established a reality where the integrity of a digital network was just as vital as the thickness of a bunker wall. The reliance on interconnected systems provided a clear pathway for adversaries to project power across borders without the immediate need for a large-scale troop presence. As these tactics became more prevalent, the traditional separation between civilian IT management and national defense began to dissolve, forcing a total reconsideration of what it meant to be secure in a hyper-connected world.
This transition necessitated a critical shift toward integrated defense strategies that treated cybersecurity as a primary component of national sovereignty. The lessons learned from the strikes of the past year demonstrated that passive defense was no longer sufficient to counter proactive, multidomain threats. Consequently, the development of robust, self-healing infrastructure became a priority for those seeking to mitigate the risks posed by this new era of warfare. Public and private sector collaboration emerged as the only viable method to harden critical assets against an enemy that moved at the speed of light while striking with the weight of steel. By the time these strategies were fully realized, the global security landscape had been permanently altered, demanding a perpetual state of vigilance across both the digital and physical horizons.