Unveiling a Growing Threat to National Security
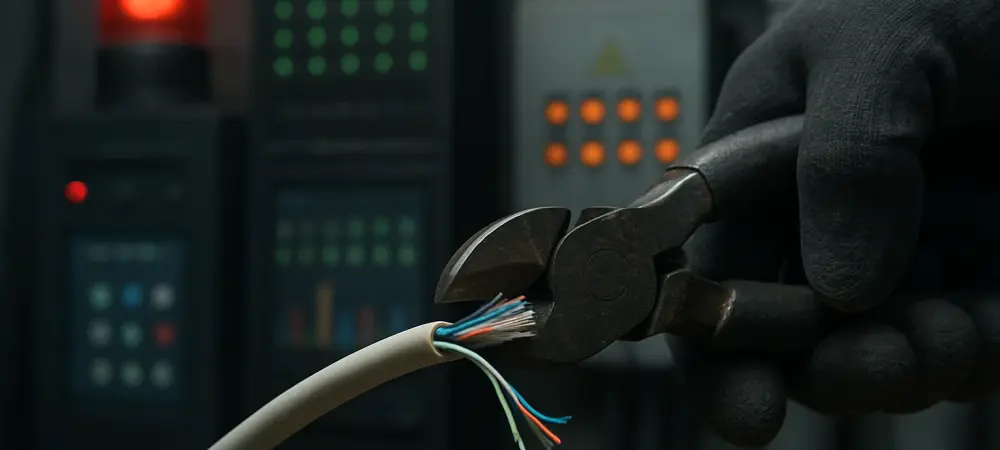
In a chilling scenario, imagine a small rural hospital in the Midwest suddenly losing access to patient records due to a ransomware attack, forcing doctors to delay life-saving surgeries while cybercriminals demand payment. This is not a distant possibility but a stark reality for many critical infrastructure entities grappling with escalating cyber threats. Cybersecurity stands as a cornerstone of national security, public safety, and economic stability, protecting essential systems like hospitals, water utilities, and energy grids from digital assaults. Yet, a troubling trend has emerged with reduced federal support for cybersecurity under the current administration, raising alarms across sectors. This analysis delves into the specifics of these cuts, their real-world impacts, expert critiques, future risks, and vital takeaways for safeguarding the nation’s infrastructure.
The Erosion of Federal Cybersecurity Funding
Budget Reductions and Strategic Shifts
The current administration has proposed significant budget cuts to key agencies tasked with defending critical infrastructure, notably the Cybersecurity and Infrastructure Security Agency (CISA). These reductions include slashing funding for essential services and reducing workforce capacity by nearly a third, severely limiting the agency’s ability to respond to threats. Additionally, an executive order issued earlier this year halted previous federal partnership frameworks, redirecting responsibilities toward state and local governments. Such policy shifts aim to shrink federal involvement, but data indicates that many of these smaller entities lack the resources to handle sophisticated cyber threats on their own.
These changes have sparked concern among stakeholders who view federal guidance as indispensable. The proposed budget not only curtails CISA’s operational scope but also impacts Sector Risk Management Agencies (SRMAs) across various domains. With funding for critical services like vulnerability assessments on the decline, the infrastructure protection landscape is undergoing a dramatic and risky transformation, potentially leaving vital systems exposed.
Consequences for Infrastructure Operators
Smaller operators, such as rural hospitals and local water utilities, bear the brunt of these federal cutbacks. These entities have long depended on free services provided by federal agencies, including threat hunting and tailored cybersecurity advice, to maintain a baseline of defense against digital attacks. Without this support, many face heightened risks, unable to afford costly private solutions to fill the gap left by diminished government aid.
A poignant example lies in the healthcare sector, where reduced federal assistance has already correlated with increased vulnerabilities. Rural medical facilities, often operating on tight budgets, struggle to implement robust defenses, making them prime targets for ransomware that can disrupt patient care. The absence of federal resources exacerbates these challenges, creating a precarious situation for communities reliant on these critical services.
Voices from the Field: Expert Critiques
Insights from Industry Leaders
Cybersecurity experts and industry leaders have voiced profound concerns over the federal pullback. Grant Geyer from Claroty describes federal support as a lifeline for under-resourced operators, warning that its reduction leaves them navigating a dangerous digital landscape alone. Similarly, Michael Daniel from the Cyber Threat Alliance highlights how budget cuts hinder SRMAs’ ability to maintain vital oversight and relationships with operators, weakening overall defenses. Errol Weiss from the Health Information Sharing and Analysis Center calls the delegation of responsibilities to state and local levels “ludicrous,” pointing to their limited capacity to counter nation-state actors. Frank Cilluffo from Auburn University’s McCrary Institute echoes this sentiment, arguing that such entities are ill-equipped to manage large-scale cyber defense initiatives. The consensus among these voices is clear: federal involvement remains essential to combat the rising tide of cyber threats.
The Gap in State and Local Capabilities
Beyond individual opinions, a broader agreement exists that shifting cybersecurity burdens to state and local governments is impractical. These entities often operate under constrained budgets and lack the technical expertise needed to address sophisticated attacks from foreign adversaries or criminal groups. This policy direction risks creating a patchwork of defenses, with uneven protection across the nation’s critical infrastructure.
The implications of this gap are significant, as local failures can have national repercussions. Experts stress that only a coordinated federal approach can effectively tackle the scale of modern cyber threats, underscoring the urgency of reversing the trend of reduced support to ensure comprehensive security for all sectors.
Looking Ahead: Risks and Potential Outcomes
Long-Term Vulnerabilities Across Sectors
The reduction in federal cybersecurity support poses severe long-term risks for critical infrastructure sectors like energy, water, and transportation. Diminished resources could lead to increased vulnerabilities, with outdated systems and inadequate defenses becoming easy targets for attackers. As digitization expands and artificial intelligence empowers cybercriminals, the stakes for unprotected infrastructure grow even higher. Consider the cascading effects of such vulnerabilities: a cyberattack on a local water utility using default passwords could disrupt supply to a military base, directly impacting national security. These interconnected risks highlight how weakened defenses in one area can ripple across others, amplifying the potential for systemic failures that threaten public safety on a grand scale.
Challenges and Opportunities in a Shifting Landscape
This trend also exacerbates disparities between well-funded operators and those with limited resources, creating uneven cybersecurity preparedness nationwide. Larger entities might pivot to private solutions, while smaller ones struggle to keep pace, widening the protection gap. However, this challenge presents an opportunity for private sector innovation to step in, potentially developing cost-effective tools tailored for under-resourced operators.
Despite these possibilities, the evolving threat landscape demands a balanced approach. While private initiatives can supplement defenses, they cannot replace the strategic oversight and resources that federal agencies provide. Addressing these disparities and leveraging emerging technologies will be crucial to mitigating future risks in an increasingly hostile digital environment.
Reflecting on a Path Forward
Looking back, the trend of diminishing federal cybersecurity support for critical infrastructure painted a worrisome picture of heightened risks and vulnerabilities. The severe budget cuts and policy shifts left smaller operators particularly exposed, while the delegation of responsibilities to state and local governments proved impractical against sophisticated cyber threats. Experts consistently warned of the national security implications, emphasizing the interconnected nature of critical systems.
Moving forward, actionable steps became imperative to address this crisis. Policymakers needed to prioritize reinstating robust federal funding and resources for agencies like CISA, ensuring that all operators, regardless of size, had access to essential cybersecurity tools. Industry leaders were encouraged to collaborate on innovative solutions, bridging gaps where public support fell short. Ultimately, a unified effort among government, the private sector, and communities was deemed essential to rebuild a resilient defense framework, safeguarding the nation’s vital infrastructure against an ever-evolving digital threat landscape.