In today’s interconnected global economy, the Taiwan Strait has become a crucial chokepoint, with the potential to disrupt supply chains and bring about an economic doomsday if China were to make a move on the island nation. This article delves into the challenges and timeline for achieving supply chain independence in advanced chips, shedding light on the critical importance of this issue.
The challenges and timeline for achieving supply chain independence
Advanced chips play a pivotal role in the global supply chain, powering a wide range of industries. However, replacing Taiwan as the sole provider of advanced chips is no easy feat and is estimated to take at least 10-20 years. According to Huang, the founder of Nvidia, a prominent technology company, supply chain independence is somewhere between a decade to two decades away. This extended timeline underscores the complexity and significance of this transition.
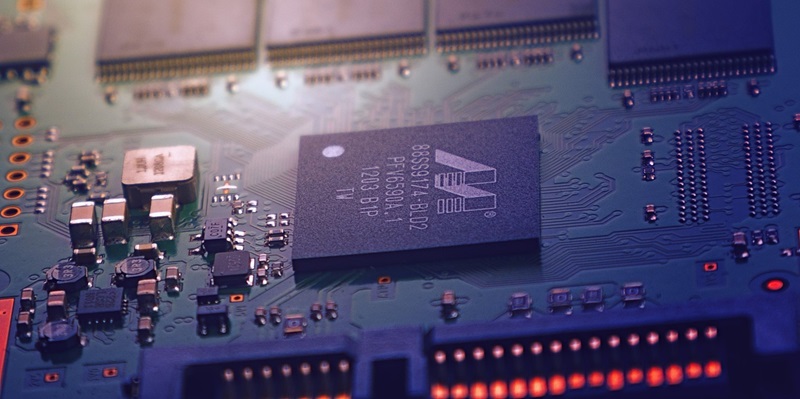
The complexities of Nvidia’s GPU manufacturing process
Nvidia is known for its highly complex GPUs (Graphics Processing Units) that are integral to various cutting-edge technologies. These GPUs consist of a staggering 35,000 individual parts, with only a small portion sourced from TSMC (Taiwan Semiconductor Manufacturing Company) in Taiwan. This highlights Nvidia’s dependence on Taiwan for critical components, making the journey towards achieving supply chain independence even more challenging.
The Importance of Supply Chain Independence
Recognizing the importance of achieving supply chain independence, Huang believes that companies like Nvidia should strive to break free from reliance on the rest of the world. However, reading between the lines, it appears that Huang acknowledges the formidable obstacles that come with complete independence, raising questions about its feasibility and desirability.
The Vision for American Leadership in Chip Manufacturing
There is a growing recognition of the need for the United States to regain its leadership in chip manufacturing. The director of the National Institute of Standards and Technology, Laurie E. Locascio, envisions, “Within a decade, we envision that America will both manufacture and package the world’s most sophisticated chips.” This ambitious vision underscores the pivotal role that chip manufacturing plays in economic stability and national security.
Huang’s perspective on the timeline for independence
When asked about the feasibility of achieving supply chain independence within a decade, Huang cautiously noted that it is technically possible but falls on the lower end of his estimate. This cautious response reflects the intricate challenges and complexities involved in this transition, emphasizing the need for careful planning and strategic execution.
Nvidia’s business strategy and national security considerations
Huang emphasized Nvidia’s intention to do business with as many companies as possible, including those in China. However, he also acknowledged the importance of US national security in navigating trade relationships. In this regard, Nvidia is committed to designing GPUs that comply with regulations to ensure safe trade with China, striking a delicate balance between economic interests and national security concerns.
The timeline for achieving supply chain independence in advanced chips is estimated to take at least a decade, and perhaps even longer. This journey is fraught with complex challenges, given the intricate nature of chip manufacturing and the dependencies that have been established over the years. However, the pursuit of supply chain independence is crucial for economic stability, reducing vulnerability to geopolitical tensions, and strengthening national security. As we navigate this path, collaboration and strategic planning among industry stakeholders, governments, and international bodies will be vital to achieving a resilient and sustainable global supply chain.