Today we’re joined by Dominic Jainy, a leading mind at the intersection of artificial intelligence and cybersecurity. We’ll be delving into the discovery of VoidLink, a sophisticated new malware framework targeting Linux and cloud systems, to understand what its advanced architecture signals about the future of digital espionage and the security challenges that lie ahead for cloud-native environments. The conversation will explore the malware’s highly modular design, its unique ability to adapt its behavior based on its environment, and the strategic implications of its development by what appears to be a state-affiliated group.
A sophisticated Linux malware framework, VoidLink, reportedly has over 30 modular plugins. What does this high degree of modularity suggest about its creators’ long-term strategy, and how might attackers combine specific plugins to tailor an attack against a high-value cloud environment?
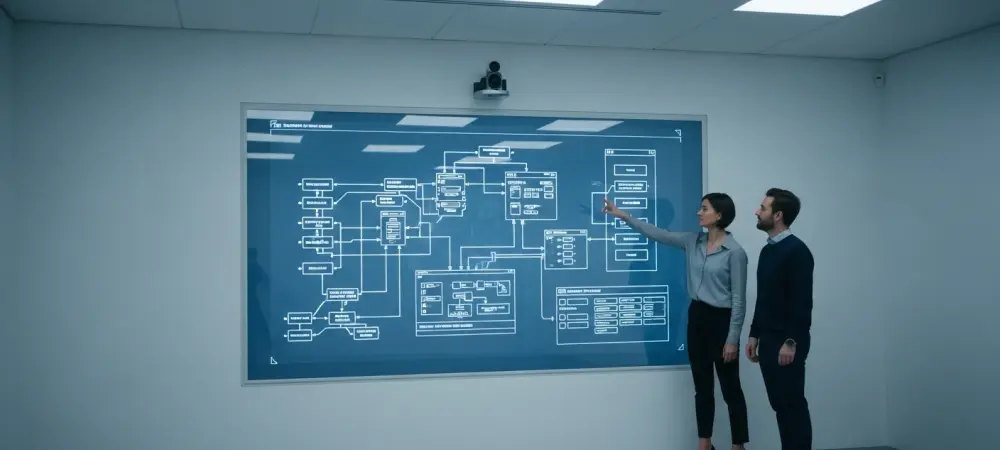
The modularity is what makes this framework so concerning. Seeing a platform with over 30 distinct plugins—including loaders, implants, and rootkits—tells me the authors weren’t building a one-off tool; they were creating a versatile, long-term weapon system. This isn’t a sledgehammer; it’s a complete surgical kit. For a high-value target, like a major cloud provider’s infrastructure, an attacker wouldn’t deploy all 30 modules. Instead, they might combine a stealthy rootkit for persistence, a specific plugin for harvesting AWS credentials, and another designed to move laterally within a Kubernetes cluster. This architecture shows a strategy of adaptability and future-proofing, allowing them to create bespoke attacks for almost any target without having to rebuild their entire toolset.
This malware is uniquely “cloud-first,” capable of identifying if it’s on AWS, Azure, or inside a Kubernetes pod before adapting its behavior. Can you walk us through the technical steps it might take to harvest cloud metadata and what this means for organizations’ cloud security posture?
The “cloud-first” aspect is a chilling evolution. Once VoidLink gains a foothold, its first action is reconnaissance. It would likely query the internal metadata endpoints that cloud providers like AWS or Azure make available to running instances. This is how a virtual machine learns about itself—its instance ID, security groups, and, critically, any attached access roles. By tapping into this, the malware instantly knows where it is and what permissions it has inherited. It can then harvest temporary API credentials directly from that metadata. For security teams, this is a nightmare scenario. It means a seemingly minor breach on a single container can immediately escalate into a full-blown cloud account compromise if that container had overly permissive access rights. It bypasses traditional network defenses and goes straight for the control plane.
VoidLink is said to calculate a risk score by profiling a system’s security tools, which then dictates how aggressively it operates. How does this adaptive stealth challenge traditional intrusion detection systems, and what new defensive paradigms are needed to counter such intelligent threats?
This adaptive stealth is a game-changer. Traditional intrusion detection systems, or IDS, often rely on spotting known malicious signatures or loud, anomalous behavior like aggressive port scanning. VoidLink is designed to defeat this very logic. By first identifying the security tools on a host, it calculates a risk score. On a well-defended system, it will throttle its own activities—no port scans, no noisy communications—essentially putting itself into a deep stealth mode. It becomes a quiet, patient observer. This makes it incredibly difficult for standard security tools to spot. To counter this, we need to move beyond simple anomaly detection. We need a zero-trust mindset, where we assume a breach is possible and focus on containing the blast radius. It requires more sophisticated behavioral monitoring that looks for very subtle, low-and-slow patterns of activity rather than just the obvious red flags.
The framework is designed to harvest a wide range of sensitive data, including API credentials and Git tokens. Please detail the typical chain of attack once these assets are compromised. What kind of lateral movement or supply chain attacks become possible with this specific stolen information?
Once those credentials are stolen, the initial beachhead becomes a launchpad for devastating attacks. With a compromised Git token, an attacker can access an organization’s source code. They can hunt for other hardcoded secrets, understand the application’s architecture, or, even worse, inject their own malicious code into the repository. This opens the door to a full-blown supply chain attack, where the company’s own software updates become a delivery mechanism for malware. With cloud API credentials, the damage is even more direct. An attacker can spin up their own servers for crypto-mining, exfiltrate sensitive data from storage buckets, or pivot to other connected services within the cloud environment. They essentially become a rogue cloud admin, with the power to disrupt operations or steal a company’s most valuable intellectual property.
Since there is no evidence of this framework being abused yet, it’s believed to be in development for future espionage campaigns. What technical indicators point toward state-affiliated development, and what does this “build now, deploy later” approach signal about future cyber threats?
Several indicators point away from typical cybercriminals and toward a state-affiliated actor, likely Chinese. First, the sheer sophistication and the number of features in a framework that isn’t for sale on the dark web suggest a massive investment of resources, typical of a government project. The objective here isn’t a quick ransomware payout; it’s long-term, persistent access for espionage and data theft. This “build now, deploy later” strategy is profoundly unsettling. It means a highly capable adversary is patiently crafting and stockpiling a powerful cyber-weapon, last updated as recently as late 2025. They are pre-positioning assets, waiting for the right geopolitical trigger to deploy them. It signals a future where cyber threats could be activated on a massive scale with little to no warning.
What is your forecast for the evolution of Linux and cloud-native malware?
My forecast is that malware like VoidLink is the blueprint for the future. We are going to see a significant increase in “environment-aware” threats that are no longer just infecting a machine but are designed to understand and exploit the cloud control plane itself. Malware will become more modular, more adaptive, and far stealthier, specifically targeting the unique architectures of AWS, Azure, and Kubernetes. The primary goal will shift from simply compromising a server to compromising an entire cloud account through credential theft. This means the line between endpoint security and cloud security will completely dissolve, forcing defenders to adopt a much more integrated and intelligent approach to protect their infrastructures.