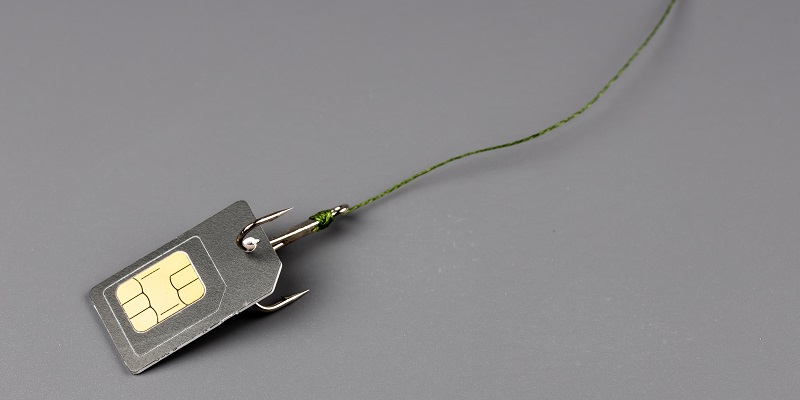
In today’s digital world, smartphones have become an integral part of our lives. However, with the increasing cases of online fraud and SIM card swapping, it is crucial to take measures to secure our SIM cards. This article will guide you on how to lock your SIM card and prevent unauthorized access, ultimately protecting your bank account and personal information.
The link between SIM cards and bank accounts
Many of us link our bank accounts or other sensitive information to our SIM cards for added convenience. However, this can also make us vulnerable to scammers and potential loss. If a fraudster gains access to your SIM card, they can easily manipulate your bank account, causing significant financial harm.
Locking the SIM Card to Prevent Fraud
To safeguard your SIM card from potential fraud, it is essential to change the settings on your Android phone and activate the SIM card lock. This lock will require a PIN number, ensuring that only authorized persons can access your SIM card and its associated functions.
Step-by-Step Process to Lock SIM Card
1. Open your phone settings: Navigate to the settings section on your Android phone.
2. Find SIM Card Lock option: In the settings menu, locate the SIM Card Lock option. It may be under different names, such as SIM Security or SIM Card Management, depending on your device.
3. Access Biometric and Security: Once you find the SIM Card Lock option, click on it to proceed further. You may need to enter your security credentials, such as your phone’s PIN or fingerprint authentication.
4. Generate a PIN of your choice: In the SIM Card Lock settings, you will typically find an option to set a PIN number. Generate a PIN that is unique and easy for you to remember but difficult for others to guess.
5. Importance of Remembering the PIN: It is crucial to remember the PIN you set for your SIM card lock. This PIN will be required to unlock your SIM card each time your phone restarts or if you remove and reinsert the SIM card. Failure to enter the correct PIN will prevent any unauthorized access.
Security Measures when Phone Restarts
In addition to setting a PIN for your SIM card, you can also enable additional security measures to protect your device and SIM card when your phone restarts. This feature, usually called “Secure Start-up” or “Encrypted Start-up,” will prompt you for your PIN or password upon restarting the device, adding an extra layer of security.
Securing your SIM card is of the utmost importance in today’s age of online fraud and SIM card swapping. By following the step-by-step process outlined in this article, you can effectively protect your SIM card, bank account, and personal information from unauthorized access. Remember to set a strong PIN and keep it confidential. Stay vigilant and take proactive measures to ensure the safety of your smartphone and your valuable data.