In today’s rapidly evolving digital landscape, ensuring the security of software is of paramount importance. As organizations strive to deliver high-quality and secure applications, GitLab has emerged as a prominent player, focusing on DevSecOps, infrastructure as code, and continuous integration. This article delves into the strategies and features that GitLab offers to create a secure build pipeline environment while harnessing the power of automation.
Understanding supply chain attacks
Supply chain attacks have become a significant concern for organizations as malicious actors aim to maintain silence, gain insights, and compromise data for financial gain or intellectual property compromise. GitLab recognizes these threats and actively works towards fortifying software pipelines against such attacks.
Creating a Secure Build Pipeline Environment
GitLab’s primary goal is to provide companies with the means to effectively secure their build pipelines. By limiting access to secrets, utilizing cloud security, and implementing CI/CD security controls at scale, GitLab empowers organizations to create a robust and secure environment for software development.
AI Features for Automated Security
GitLab’s AI features go beyond traditional code repository functionalities. With code generation and suggested changes/reviewers, developers can automate the infusion of security into the development process without hampering their productivity. These AI-driven capabilities streamline security practices and alleviate the burden on security teams.
Early feedback loop for security issues
One of the key advantages of GitLab’s approach is the establishment of a tight feedback loop early in the development process. By providing just-in-time, actionable feedback, security issues can be identified and resolved before the software reaches production. This proactive approach saves time, effort, and resources while ensuring a higher standard of software security.
Shifting Left Approach for Security Teams
GitLab adopts a shifting left approach, advocating for security teams to focus on design and architecture work earlier in the software development lifecycle, instead of dealing with vulnerabilities at the code-committing stage. This strategic shift allows for greater collaboration and empowers teams to address security challenges proactively.
AI-driven and traditional security solutions
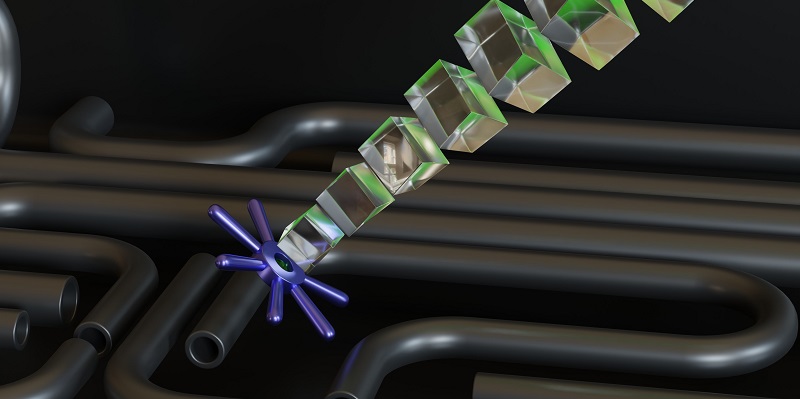
To fortify the software pipeline, GitLab employs an integrated security solution that combines AI-driven tools with traditional static code analysis and container scanning for known vulnerabilities. This multifaceted approach equips organizations with comprehensive security measures, covering different aspects of the development process.
The importance of automation in security teams
Automation plays a pivotal role in enhancing the efficiency of security teams. By leveraging both AI-driven and traditional software automation, manual work is substantially reduced, freeing up valuable time and resources for handling critical security issues that cannot be automated. This shift enables security teams to focus on strategic decision-making and proactive measures.
Prioritizing Automation in Security Teams
A significant movement within security teams is the prioritization of automation as a means to scale and meet the demands of the velocity required by companies and engineering teams. By embracing automation, organizations can streamline their security practices and effectively safeguard their software pipelines against emerging threats.
In an ever-changing threat landscape, the ultimate goal is to secure the software pipeline regardless of the number of developers involved. With its focus on DevSecOps, infrastructure as code, and continuous integration, GitLab provides a comprehensive solution for bolstering software security. By leveraging automation and providing meaningful feedback, organizations can strengthen their security posture and deliver high-quality and secure applications. GitLab is an indispensable ally in the quest for secure software development.