In today’s digital age, the rise of deepfake videos and camera injection attacks has posed a significant challenge to biometric authentication and online security. These sophisticated techniques allow fraudsters to manipulate identities and deceive unsuspecting users. This article delves into the alarming forecast by Europol, explores the intricacies of camera injection attacks, discusses the concealed nature of these attacks, highlights the potential consequences, and provides valuable insights into safeguarding against them.
Europol’s Forecast for the Future of Online Content
Europol predicts that by 2026, as much as 90 percent of online content may be artificially generated. This surge in artificially created content presents a pressing issue for organizations that rely on accurately determining the true identities of their users. As deepfake technology evolves rapidly, fraudulent actors can exploit it to deceive both individuals and organizations.
Understanding Camera Injection Attacks
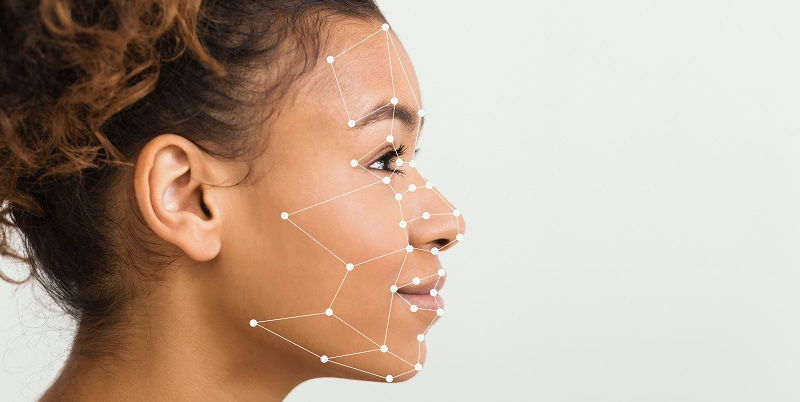
Camera injection occurs when fraudsters bypass a camera’s charge-coupled device (CCD) to inject pre-recorded or deepfake content in real-time. Through various methods, such as face swap videos and fabricated content, attackers can impersonate others and manipulate visual data captured by cameras. This process raises concerns about the reliability of biometric authentication systems that heavily rely on facial recognition.
One of the most alarming aspects of camera injection attacks is the potential for attackers to go undetected. Victims may remain oblivious to the hack, unaware that their identity has been compromised. This allows malicious actors to exploit the stolen identity for various malicious activities without immediate consequences.
Consequences of Successful Attacks
When attackers successfully bypass verification through camera injection, the potential for damage becomes substantial. Identity theft, creation of fake accounts, and fraudulent transactions are among the risks involved. Such actions can lead to severe financial and reputational damage for both individuals and organizations, causing turmoil and loss in all aspects of life.
To effectively safeguard against camera injection attacks, it is crucial to detect instances of compromised camera device drivers. Organizations must implement robust mechanisms that continuously monitor and verify the integrity of camera systems. Regular audits and updates of camera firmware play a vital role in preventing unauthorized access and exploitation.
Techniques for Detecting Fake Videos
Detecting fake videos requires comparing the natural motion in a video with the captured footage. Differences in parameters such as ISO, aperture, frame rate, resolution, and light or color intensity can expose fraud. By carefully analyzing these aspects, it becomes possible to identify manipulated videos and mitigate the risk of deepfake attacks.
Use of Accelerometers for Detecting Camera Hacks
Leveraging the built-in accelerometer within cameras can help in identifying potential camera hacks. By tracking changes in objects within recorded videos, suspicious activities that indicate camera manipulation can be highlighted. Implementing this technique alongside other detection measures enhances overall security.
Forensic Analysis for Uncovering Manipulation
Forensic analysis of individual frames within a video can uncover signs of manipulation. Look for double-compressed parts or traces of computer-generated deepfake images, which can indicate potential fraudulent activity. Conducting a thorough and rigorous examination of videos is crucial in identifying tampered content.
As deepfake videos and camera injection attacks become increasingly prevalent, the need for robust security measures is paramount. Organizations must stay vigilant, constantly improving their algorithms and detection mechanisms to stay one step ahead of fraudsters. By implementing the techniques discussed, such as identifying compromised camera device drivers, comparing natural motion, utilizing accelerometers, and conducting forensic analysis, individuals and organizations can protect themselves from the detrimental consequences of these emerging threats. A proactive approach to security is essential to maintain trust and ensure the integrity of online identities in the digital landscape.