In the realm of CPU performance, SAFEDISK has set a new standard by pushing an Intel Core i9-14900K to its limits. Achieving a record-breaking time of 2 minutes, 59.919 seconds in the SuperPI 32M benchmark isn’t just a personal triumph; it’s a testament to what’s possible in the hands of a skilled overclocker. This latest feat surpasses previous expectations for computer processing speeds, illustrating the major league capacity of the i9-14900K when overclocked beyond its factory settings. SAFEDISK’s accomplishment is more than just a milestone; it’s a gauntlet thrown down in the world of high-performance computing, challenging others to step up their game. With the bar set this high, the i9-14900K not only shines in its raw speed but also hints at the untapped potential lurking within modern CPUs.
Precision Engineering and Extreme Cooling
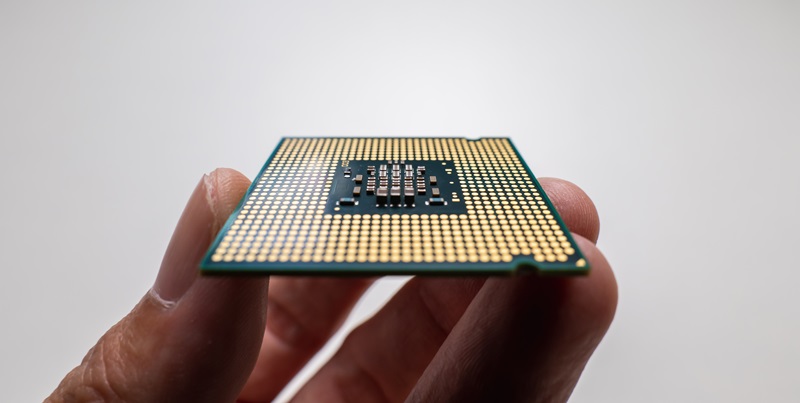
The secret behind this world-record-breaking performance lies not only in the intrinsic power of the Intel Core i9-14900K. SAFEDISK capitalized on sophisticated technological synergy, pairing the CPU with an ASUS ROG Maximus Z790 APEX motherboard and expertly optimized G.Skill DDR5 memory—a combination designed for peak performance. This achievement was made possible through the use of extreme liquid nitrogen cooling (LN2), enabling the chip to function at deeply sub-zero temperatures. SAFEDISK pushed the configuration even further by deactivating all but four of the 24 cores and 32 threads, allowing an unheard-of overclocking frequency of 8449.22MHz while operating at an elevated voltage of 1.79V.
A New Era for Overclockers
SAFEDISK’s staggering overclock of the Core i9 CPU to just under three minutes in a computing task marks a new pinnacle for enthusiast computing. This compares to the stock Core i9-14900K which finishes the same task at 5 minutes and 45 seconds. This feat not only underlines the Core i9’s potential for speed when pushed beyond its limits but also the overclocking community’s relentless drive for advancement. The detailed hardware knowledge required to achieve such a result accentuates the technical proficiency held by SAFEDISK. The ability to coordinate and finely tune the various system components to work in harmony represents a significant stride in high-performance computing. It’s a perfect illustration of how far technology can be pushed, from the baseline to new heights, by those passionate about the endless pursuit of improved speed and efficiency.