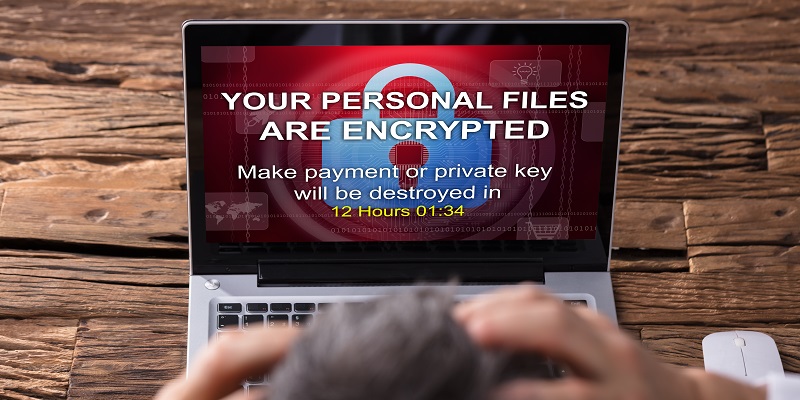
In recent years, ransomware attacks have become increasingly prevalent and damaging, causing significant financial losses and disruptions across various industries. June 2023 saw a staggering surge in ransomware incidents, with a record-breaking 434 attacks reported. This article delves into the details of this alarming trend, highlighting the exploits of notable ransomware groups and providing insights into the evolving threat landscape. It also emphasizes the importance of staying vigilant and adapting security measures to protect against these ever-evolving cyber threats.
Ransomware Attacks Surge in June
Ransomware attacks in June showed a remarkable 221% year-on-year increase, reflecting a concerning upward trajectory in cybercriminal activities. The total tally of 434 incidents marked an all-time high, illustrating the urgency for organizations to fortify their cybersecurity defenses.
Clop Ransomware Exploits Zero-Day Vulnerability in MOVEit Software
One of the standout threats during the month was Clop ransomware, which accounted for 21% of attack activity. Clop capitalized on a zero-day vulnerability found in MOVEit software, a popular file transfer solution. This underscores the criticality of promptly patching vulnerabilities to prevent potential breaches and data extortion attempts.
LockBit 3.0 remains the most prolific ransomware group. Throughout 2023, this established group accounted for 14% of attacks, showcasing the enduring presence of experienced cybercriminals in the ransomware landscape. With their sophisticated tactics and potent malware, LockBit 3.0 continues to demonstrate their dominance as a threat actor.
Emergence of New Ransomware Groups
June witnessed the emergence of several new ransomware groups, further contributing to the rising number of attacks. Notably, groups such as 8base, Rhysida, and Darkrace showcased their capabilities, indicating a dynamic and continually evolving threat landscape. These developments serve as a sobering reminder that organizations must remain proactive and adaptive in their security measures.
Regional Distribution of Ransomware Victims
Geographically, North America experienced the highest number of ransomware victims, accounting for 51% of attacks. Europe followed closely with 27%, while Asia accounted for 9% of victims. These statistics underscore the global reach and impact of ransomware, warranting a collaborative and international approach to tackle this menace.
Targeted Sectors in Ransomware Attacks
Among the sectors targeted by ransomware attackers, the “industrials” sector suffered the most significant impact. Critical infrastructure, manufacturing, and energy companies within this sector faced substantial cybersecurity challenges. Additionally, the “consumer cyclicals” and technology sectors were also prime targets, highlighting the breadth of industries vulnerable to these attacks.
Insight from Matt Hull, Global Head of Threat Intelligence
Matt Hull, a prominent figure in the cybersecurity landscape, emphasizes the evolving nature of the ransomware threat landscape. He highlights the importance of adopting a comprehensive approach to cybersecurity, combining proactive measures, threat intelligence, and efficient incident response capabilities to effectively mitigate risks.
Importance of Adapting Security Measures
While established groups like LockBit 3.0 continue to pose significant threats, the appearance of new ransomware groups necessitates constant adaptation of security measures. Organizations must invest in robust cybersecurity frameworks that evolve and adapt alongside emerging threats. Continuous monitoring, employee training, and timely patching of software vulnerabilities are crucial elements of a well-rounded defense strategy.
Recommendations for Organizations
To safeguard against ransomware attacks, organizations should prioritize the following measures:
– Maintain up-to-date security protocols and antivirus software.
– Conduct regular vulnerability assessments and promptly address any identified weaknesses.
– Implement multi-factor authentication and strong password policies.
– Conduct regular training and awareness programs to educate employees about phishing and social engineering tactics.
– Back up critical data regularly and keep backups offline or in secure and segmented networks.
– Apply the recent patch for MOVEit software to address the exploited vulnerability.
The surge in ransomware attacks witnessed in June 2023 serves as a stark reminder of the constantly evolving threat landscape organizations face. Established and new ransomware groups alike continue to target vulnerable sectors and exploit software vulnerabilities. Staying ahead of these threats requires proactive measures, regular patching, employee education, and a comprehensive cybersecurity strategy. By remaining vigilant and adapting security measures, organizations can strengthen their defense against ransomware and protect their critical assets from malicious actors.