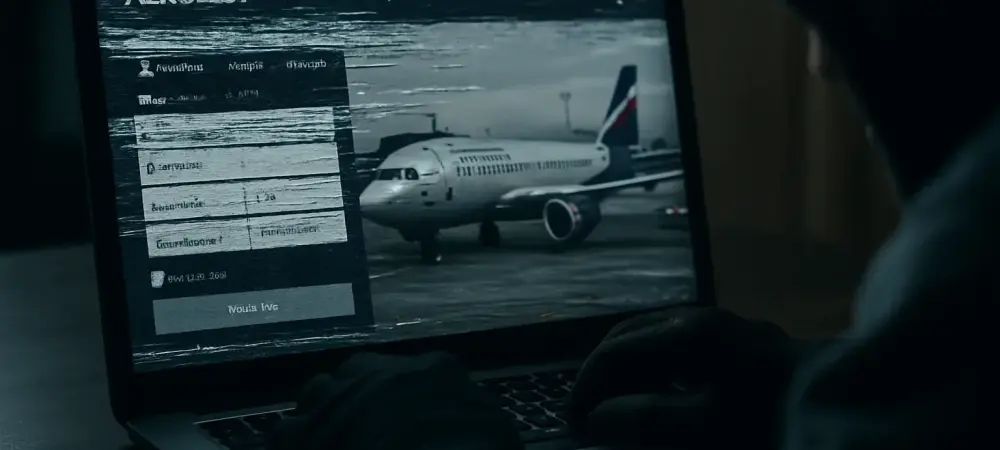
I’m thrilled to sit down with Dominic Jainy, a seasoned IT professional whose expertise in artificial intelligence, machine learning, and blockchain offers a unique perspective on the evolving landscape of cybersecurity. Today, we’re diving into a recent high-profile cyberattack on Aeroflot, Russia’s national airline, claimed by pro-Ukraine hacktivist groups. Dominic will help us unpack the details of this disruptive incident, explore the groups behind it, and discuss its broader implications in the context of international cyber warfare and the ongoing Ukraine-Russia conflict.
Can you walk us through the details of the cyberattack on Aeroflot and what made it so significant?
Certainly. The cyberattack on Aeroflot was a bold move by pro-Ukraine hacktivist groups, who claimed to have completely compromised and destroyed the airline’s internal IT infrastructure. This wasn’t just a surface-level breach; they asserted that they had deep access to the core systems for an extended period. The attack reportedly led to the cancellation of over 50 flights, causing major disruptions, especially for holiday travelers. What makes this incident stand out is the scale and strategic nature of the damage, as well as its timing alongside other Ukrainian efforts to pressure Russia. Aeroflot officially attributed the chaos to an “information systems failure,” but the hackers painted a very different picture of calculated destruction.
Who are the groups behind this attack, and what do we know about their history?
The two groups claiming responsibility are Silent Crow and Cyber Partisans, both known for their pro-Ukraine stance. Silent Crow, in particular, has a track record of targeting Russian entities, with past breaches linked to Moscow’s government and state-owned companies. Cyber Partisans, often associated with Belarusian opposition, have also been involved in disruptive actions against regimes aligned with Russia. Silent Crow publicly stated on Telegram that this was a long and large-scale operation, emphasizing their deep infiltration into Aeroflot’s network over the course of a year. These groups are not new to the cyber warfare scene and seem to be motivated by political and ideological goals.
What kind of damage did the hackers claim to have inflicted on Aeroflot’s systems?
The hackers boasted about causing extensive damage, claiming to have destroyed around 7,000 physical and virtual servers. They also said they exfiltrated a massive 20 terabytes of data, including sensitive information from flight history databases, corporate systems like email archives, and even employee computers. On top of that, they accessed data from wiretapping servers, which adds a layer of espionage to the attack. They suggested the financial impact could run into tens of millions of dollars for recovery, framing the damage as strategic and long-lasting. If true, this level of destruction and data theft is staggering.
How does this attack differ from other cyberattacks we’ve seen in recent years?
This incident is considered one of the most disruptive to Russia since the invasion of Ukraine began, largely because it directly impacted civilian life by grounding flights and halting mobility. Experts have noted that the attack combined multiple tactics—deep covert infiltration, physical destruction of infrastructure, and cascading service failures. It’s not just about stealing data; it’s about sabotage and sending a psychological message to the Russian public. This blend of espionage and outright destruction marks a shift in how cyber warfare can be wielded to undermine a nation’s resilience, making it a standout case in modern conflicts.
How does this cyberattack connect to the broader Ukraine-Russia conflict?
This attack is deeply tied to the ongoing war, aligning with Ukraine’s apparent strategy to “bring the war home” to ordinary Russians. It coincided with reports of Ukrainian drone strikes on Russian airspace, suggesting a coordinated effort to disrupt both physical and digital infrastructure. The idea here seems to be to make the conflict tangible to Russian civilians, who might otherwise feel detached from the war’s consequences. By targeting something as everyday as air travel, the hackers are amplifying the psychological impact, showing that no part of life is immune to the conflict’s reach.
What lessons can businesses and governments take away from an incident like this?
This attack is a wake-up call for both private companies and governments, especially those in critical sectors like transportation. It highlights the importance of continuous threat hunting to detect long-term infiltrations before they escalate. Network segmentation is also crucial to limit the spread of damage if a breach occurs. Additionally, robust disaster recovery plans are non-negotiable—businesses need to be prepared to rebuild quickly after such devastating attacks. Finally, collaboration across industries and with government bodies is essential to defend civilian systems, particularly during times of geopolitical tension or active conflict.
Looking ahead, what is your forecast for the role of cyberattacks in international conflicts like this one?
I believe cyberattacks will only become more central to international conflicts in the coming years. They offer a way to strike at an adversary without traditional military engagement, often with plausible deniability. As technology advances, especially with AI and machine learning, we’re likely to see even more sophisticated attacks that can evade detection for longer and cause greater disruption. The Aeroflot incident shows how cyber warfare can target civilian infrastructure to create widespread impact, and I expect this trend to grow, with nations and non-state actors alike using digital tools to wage war on multiple fronts. Governments and organizations will need to prioritize cybersecurity as a core component of national defense.