In the rapidly evolving landscape of artificial intelligence, Large Language Models (LLMs) have emerged as powerful tools with vast potential. However, the dark side of this technology is becoming increasingly apparent. LLMs can now be weaponized, enabling attackers to personalize context and content in rapid iterations, with the aim of triggering responses from unsuspecting victims. This article delves into the alarming reality of weaponized LLMs, exploring their potential for harm and emphasizing the urgent need for enhanced security measures.
The Potential for Weaponized LLMs
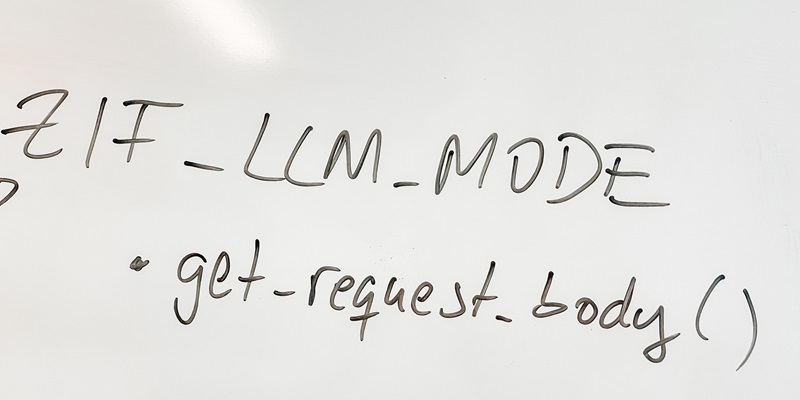
LLMs possess the ability to personalize and manipulate context and content to an unprecedented extent. Attackers can utilize this capability to fine-tune LLMs until they successfully trigger desired responses from their victims. By leveraging rapid iterations, attackers can refine their approaches and exploit vulnerabilities in unsuspecting individuals, organizations, and systems. This immense potential for manipulation raises serious concerns about the readiness of LLM providers to address the security risks posed by their own creations.
Addressing Security Risks: A Call to Action
Considering the destructive potential of weaponized LLMs, it is crucial for LLM providers to acknowledge the risks and take immediate action to harden their models against potential attacks. In the current developmental phase of these technologies, it is vital to incorporate robust security measures to avert the devastating consequences that weaponized LLMs may unleash. Only by proactively addressing these risks can LLM providers ensure the responsible and safe use of their creations.
LLMs: A Double-Edged Sword
While LLMs offer immense benefits in terms of language generation and understanding, they also present significant dangers due to their potential misuse. These models, when in the wrong hands, can become lethal cyber weapons. Their power lies not only in their ability to generate coherent text but also in the ease with which attackers can learn and eventually master them. This dual nature of LLMs raises concerns about the potential for widespread harm if not properly regulated and secured.
The BadLlama Study: Highlighting Critical Threat Vectors
A collaborative study between the Indian Institute of Information Technology, Lucknow, and Palisade Research shed light on a critical vulnerability in Meta’s Llama 2-Chat. Despite their intensive efforts to refine the model, the study revealed that attackers could fine-tune the LLM to remove safety training altogether, bypassing existing controls. This finding emphasizes the pressing need for LLM providers to address such threat vectors and fortify their models against malicious manipulation.
The ReNeLLM Framework: Exposing Inadequate Defense Measures
Researchers have discovered how generalized nested jailbreak prompts can deceive LLMs, exposing the inadequacy of current defense measures. In response to this finding, the proposed ReNeLLM framework harnesses LLMs to generate jailbreak prompts, highlighting the vulnerabilities that exist within these models. By exposing these weaknesses, researchers aim to spur the development of more robust defense mechanisms to safeguard against potential attacks.
Exploiting Safety Features: Jailbreaking and Reverse Engineering
The safety features incorporated into LLMs can be circumvented through jailbreaking and reverse engineering techniques. Attackers may leverage these methods to disable or bypass safety measures, potentially enabling them to manipulate the LLMs for their own malicious purposes. The prevalence of jailbreaking and reverse engineering highlights the need for enhanced security protocols to protect against potential exploits.
Phishing and Social Engineering Attacks: A Disturbing Reality
The ease with which targeted spear-phishing campaigns can be created and disseminated using spam emails sends shockwaves through cybersecurity circles. A chilling simulation conducted by Oxford University exemplified how swiftly and effortlessly such campaigns could be sent to every member of the UK Parliament. This stark illustration serves as a wake-up call, highlighting the urgent need for robust defense mechanisms to combat this growing threat.
Brand Hijacking, Disinformation, and Propaganda
LLMs also pose a grave risk in terms of brand hijacking, dissemination of disinformation, and propagation of propaganda. With the ability to generate convincing and contextually relevant content, LLMs can be employed to manipulate public opinion, spread falsehoods, and tarnish reputations. Such misuse of LLMs has enormous implications for democracy, public trust, and societal stability, underscoring the importance of mitigating these risks.
LLMs in Biological Agents and Genetic Engineering
A collaborative study between researchers from MIT and Harvard has revealed disturbing implications regarding the use of LLMs in biological contexts. The study explored how LLMs could aid in synthesizing harmful biological agents or advancing dangerous genetic engineering techniques. These findings underscore the urgent need for responsible oversight and regulation to prevent the potential misuse of LLMs in the realm of biosecurity.
The era of weaponized LLMs has arrived, magnifying the need to address the associated risks. LLMs represent a double-edged sword, promising immense benefits while simultaneously presenting the potential for devastating cyberattacks. The BadLlama study, the ReNeLLM framework, and chilling simulations by Oxford University serve as timely reminders of the pressing challenges we face. It is imperative for LLM providers, researchers, policymakers, and regulatory bodies to collaborate closely to secure and regulate this powerful technology. Failure to act swiftly and decisively may plunge us into a future defined by unprecedented cyber threats and widespread chaos. It is only through collective effort and vigilance that we can safeguard against the dark potential of weaponized LLMs.