As the march toward quantum computing accelerates, traditional computational hardware has met an innovation ceiling. However, Nvidia’s H100 GPUs are spearheading a revolutionary leap forward, providing the computational might to power quantum supercomputers. These GPUs exhibit an impressive balance between processing power and energy efficiency, making them the cornerstone of the next generation of supercomputing systems. Researchers and scientists across the globe have now at their disposal tools that can execute complex calculations, once considered impractical, in record time. This marks a significant milestone in the quest to unravel some of the world’s most perplexing scientific mysteries.
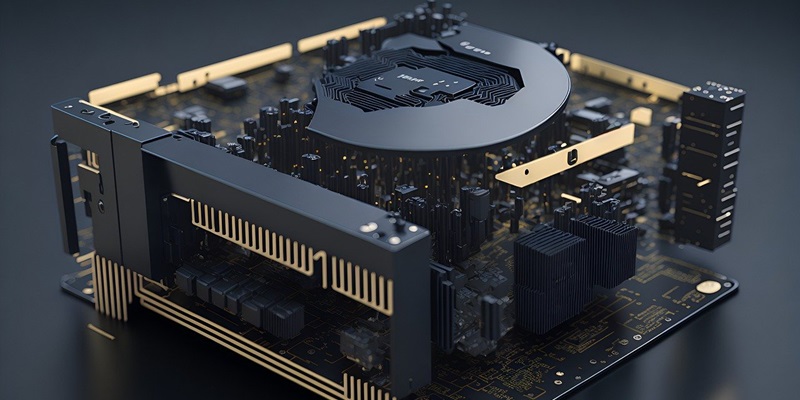
The centerpiece in this endeavor is the Application Specific Integrated Circuit (ASIC) designed within the H100, which offers unprecedented acceleration for quantum circuit simulations. This feature is essential, as the simulation of quantum states is an inherently resource-intensive task. By harnessing the power of the H100 GPUs, researchers can create and observe the behavior of quantum circuits without the astronomical costs of running actual quantum computers. As such, these simulations are pivotal for understanding quantum mechanics and pushing the boundaries of what’s possible with computation, thus making significant advances toward practical quantum computing applications in various fields.
Global Adoption and Industry Impact
Japan is making quantum leaps in computing with the ABCI-Q system, utilizing over 2,000 Nvidia H100 GPUs. This significant effort by Fujitsu positions Japan as a leader in quantum computing research. Leveraging Nvidia’s advanced GPU tech, this partnership is propelling scientific breakthroughs in fields like medicine, materials science, and quantum physics. The ABCI-Q supercomputer embodies the critical role of high-performance GPUs in expanding the horizons of research and innovation.
In Denmark, the Novo Nordisk Foundation is advancing quantum research by incorporating Nvidia GPUs into their cutting-edge DGX SuperPOD. This integration signifies a global trend in science toward harnessing the power of high-performance GPUs. Such technological integration is essential for tackling the complex challenges of modern times. Collectively, these initiatives with the #00 GPUs spotlight their pivotal role in not just processing, but shaping the future of scientific computing.