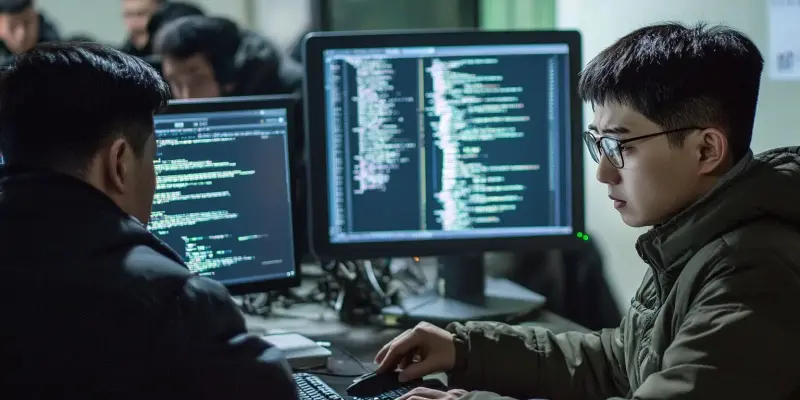
In a recent development highlighting the ever-evolving landscape of cyber threats, North Korean state-sponsored hackers have been discovered using a novel approach to deploy macOS malware. The malware, known as FlexibleFerret, is being disseminated under the guise of fake job interviews, part of a campaign named “Contagious Interview,” targeting both developers and potential employers. This tactic has increased concerns among security researchers and raised the alarm for companies, especially those involved in technology sectors, to bolster their cybersecurity awareness and defenses.
A New Threat with Old Roots
SentinelOne researchers revealed that the North Korean actors are luring unsuspecting individuals by posing as prospective employers conducting job interviews. During these fake interviews, victims are directed to malicious links under the pretense of scheduling follow-up interviews or downloading necessary software. Once the victims click on these links, they receive deceptive error messages persuading them to install bogus software updates, thereby unknowingly downloading the FlexibleFerret malware onto their systems. This sneaky technique blends social engineering with sophisticated technical exploitation, making it particularly dangerous and effective.
The malicious campaign targeting job seekers has been ongoing since November 2023, with the North Korean hackers exploiting platforms such as GitHub, job search websites, and tech forums. By opening fake issues in legitimate GitHub repositories, the hackers distribute the malware, hoping to gain backdoor access to the victim’s system. FlexibleFerret stands out because it evades detection using a valid Apple Developer signature and Team ID, which have unfortunately only recently been revoked by Apple. This level of sophistication highlights the attackers’ determination and resourcefulness in bypassing standard security measures.
Persistent Evasion Tactics
Despite Apple’s efforts to counteract this threat by revoking the compromised developer credentials, FlexibleFerret remains a thorn in cybersecurity efforts. The malware’s ability to elude detection by Apple’s XProtect signifies the advanced methods employed to obscure its presence on infected systems. FlexibleFerret’s use of legitimate developer signatures allows it to blend in seamlessly with legitimate processes, making it exceedingly challenging for conventional security software to identify and neutralize the threat. This incident underscores the need for more adaptive and robust security protocols to counter such clandestine malware.
The larger context of these attacks aligns with warnings previously issued by the FBI regarding North Korean operatives’ use of deepfake technologies to infiltrate Western firms. By integrating fake job interviews into their cyberattack strategies, these hackers exploit a critical vulnerability in remote hiring practices prevalent in the modern workforce. Job applicants, often eager to secure new employment opportunities, may lower their guard, making them prime targets for these sophisticated phishing campaigns. The consequences for employers are dire, as compromised systems can lead to significant data breaches and unauthorized access to sensitive corporate information.
Enhanced Vigilance and Proactive Defense
Security experts emphasize the importance of robust cybersecurity measures to mitigate the risks posed by such sophisticated attacks. Enhancing employee training to recognize phishing attempts, conducting regular security audits, and implementing advanced threat detection systems are critical steps companies should take. As the cyber threat landscape continuously evolves, staying vigilant and proactive is essential in protecting sensitive data and systems from malicious actors.