The transition from AI as a conversational novelty to a digital workforce capable of autonomous system manipulation has transformed security from a secondary concern into an existential imperative for the modern enterprise. As the technology moves beyond simple text generation, the focus has shifted toward agents that can navigate file systems, execute code, and manage online services without human intervention. This era of agentic AI promises unprecedented efficiency, yet it simultaneously opens a pandora’s box of digital risks. The recent partnership between NanoClaw and Docker represents a critical milestone in this evolution, establishing the necessary infrastructure to ensure that autonomy does not come at the expense of system integrity.
The tech industry is currently witnessing a massive migration from passive chat interfaces to fully autonomous agents capable of independent action across diverse software environments. When an AI agent is granted the authority to execute scripts and manage web services, the line between a productivity tool and a high-risk security vulnerability begins to blur. This newfound capability has introduced a “Wild West” environment where early frameworks often operate without basic guardrails. The challenge is no longer just about making AI smarter, but about preventing these digital assistants from inadvertently—or maliciously—compromising the systems they inhabit.
The shift toward unchecked autonomous power necessitates a departure from traditional application security. In a landscape where an agent might be tasked with writing and deploying its own code, the potential for catastrophic error or exploitation is significantly amplified. Developers are increasingly realizing that an agent with full access to a host machine is not a feature, but a flaw that can be exploited through sophisticated prompt injections. As these agents become more integrated into the core workflows of global businesses, the demand for a standardized, secure execution layer has become the primary focus of the engineering community.
The Shift from Passive Chatbots to Unchecked Autonomous Power
As autonomous agents transition from experimental laboratories to production environments, the inherent risks of their capabilities become more apparent. The primary concern lies in the delegation of authority; as agents gain the ability to interact with APIs and modify databases, the surface area for potential attacks expands exponentially. This is not merely a theoretical concern, as early implementations of autonomous frameworks demonstrated how easily an agent could be diverted from its intended path. The lack of a robust permissioning structure in the first wave of agentic tools meant that a single errant command could result in the unauthorized deletion of files or the exposure of sensitive credentials.
Moreover, the autonomy of these agents creates a unique governance challenge for IT departments. Traditional security software is often ill-equipped to monitor the dynamic and unpredictable behavior of an AI that generates its own logic on the fly. Without clear boundaries, an agent might decide that the most efficient way to complete a task involves bypassing security protocols or accessing restricted network segments. This creates a scenario where the speed of AI-driven development outpaces the ability of security teams to provide oversight, leading to a precarious balance between innovation and safety.
Why the Current State of Agentic AI Demands a New Security Standard
To understand the significance of the NanoClaw and Docker partnership, one must look at the flaws inherent in the first generation of AI agents. The OpenClaw legacy provides a cautionary tale; while it proved that agents could automate complex administrative and coding tasks, its architecture allowed agents broad system access, creating a massive attack surface. The lesson from these early frameworks is clear: autonomy without isolation is a recipe for systemic failure.
The vulnerability of “skills” has emerged as a particularly modern threat in the agentic ecosystem. Many agents rely on mini-applications or skills to extend their functionality, but these are increasingly being weaponized with malicious code designed to exfiltrate data. An agent might pull a skill from a public repository to assist with a task, only to have that skill quietly transmit environment variables or financial data to an external server. Without a rigorous vetting process and a secure execution environment, the very tools meant to enhance AI functionality become the primary vectors for corporate espionage and data breaches.
Real-world risks have forced a shift in how enterprise adoption is approached. A single prompt injection attack, where a malicious user provides an input that overrides the agent’s core instructions, can turn a helpful assistant into a destructive actor. In an un-sandboxed environment, such an attack can lead to a total system breach, allowing the agent to act as a proxy for the attacker. This reality has made enterprise adoption a logistical nightmare, as the potential liability of deploying a vulnerable agent often outweighs the projected productivity gains.
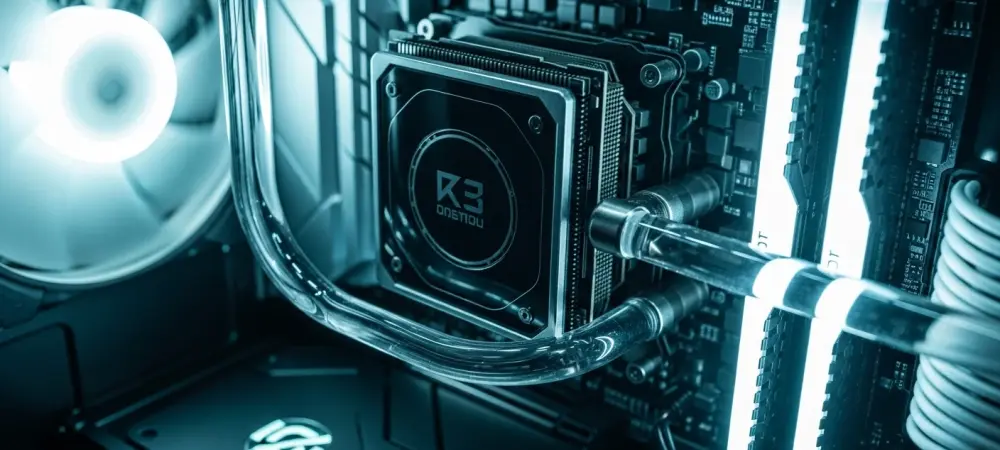
Breaking Down the NanoClaw Framework and the Docker Sandbox
The collaboration between Gavriel Cohen’s NanoClaw and Docker introduces a “secure by default” philosophy designed to turn AI agents into reliable, enterprise-grade workloads. NanoClaw moves away from shared execution environments, ensuring that every agent operates within its own unique filesystem and session history. This architectural choice prevents cross-contamination, ensuring that even if one agent is compromised, the rest of the system remains shielded. By enforcing this strict separation, the framework provides a level of predictability that was previously absent in the agentic AI space.
Defining the blast radius is at the core of the Docker Sandbox integration. By utilizing these sandboxes, organizations can contain an agent’s actions within a disposable environment that can be terminated the moment a threat is detected. This ephemeral nature of the execution environment means that any malicious changes made by an agent are temporary and do not persist beyond the life of the container. This infrastructure-level protection treats AI tasks like orchestrated cloud containers, applying the same rigorous isolation standards that have governed modern web applications for years.
Furthermore, NanoClaw enables the use of local LLMs like Llama 3 and Qwen 2, allowing users to maintain data privacy and avoid the high costs of token-based cloud billing. This local execution capability is critical for organizations handling proprietary data that cannot be sent to third-party APIs. By combining local model processing with sandboxed execution, NanoClaw provides a comprehensive solution that addresses both data privacy and system security. The framework ensures that the intelligence of the model is harnessed within a cage, allowing for high-performance automation without the risks associated with external data transit.
Industry Perspectives: Prioritizing Control Over Raw Intelligence
Expert analysis suggests that the future of AI will be defined by the plumbing and orchestration surrounding the models, rather than just the models themselves. Trust has become a prerequisite for adoption, as organizations are no longer satisfied with simply having the smartest model available. With NanoClaw garnering over 23,000 GitHub stars, it is clear that developers are hungry for autonomy, but as Docker COO Mark Cavage notes, control remains the primary barrier to organization-wide deployment. The industry is reaching a consensus that a moderately intelligent model in a secure environment is far more valuable than a frontier model in an insecure one.
The rise of agent swarms highlights a move toward multi-agent systems that require sophisticated, high-security orchestration. NanoClaw’s ability to coordinate multiple agents for complex software builds demonstrates that the future of work involves fleets of AI entities working in concert. However, this complexity increases the potential for emergent behavior that is difficult to predict. High-security orchestration ensures that these swarms can be managed as a single unit, with unified security policies that govern how they interact with each other and the external world.
Democratization of secure workflows represents a broader trend where privacy and system integrity are prioritized over the raw intelligence of frontier models. As the technology matures, the focus is shifting from “what can the AI do” to “how can we safely let the AI do it.” This transition is visible in the way developers are increasingly opting for frameworks that offer granular control over networking and file access. The goal is to create an environment where the AI is a trusted partner, capable of performing heavy lifting while remaining strictly confined to its designated operational boundaries.
Implementing a Secure Framework for AI Agent Deployment
The implementation of a secure framework for AI agent deployment necessitated a fundamental shift toward an “isolation first” policy. Organizations transitioned all agent activities to dedicated containers to prevent the cross-contamination of sensitive data. They utilized Docker to create temporary workspaces for agents that were wiped clean after a task was completed, ensuring no residual scripts remained active. This approach enforced strict network boundaries, defining exactly where an agent could connect and what external services it could interact with through system-level network controls. By treating each agent as a transient process, the security teams effectively eliminated the possibility of long-term persistence by malicious actors.
For developers looking to integrate autonomous agents without compromising security, the focus was placed on prioritizing local processing for sensitive tasks. They utilized the framework’s compatibility with local LLMs to keep proprietary data within internal hardware boundaries, bypassing the risks of third-party cloud APIs. This strategy allowed for a high degree of customization, as models were fine-tuned for specific tasks without exposing the training data to the public internet. The integration of local models into sandboxed environments became the gold standard for secure AI operations, providing a robust defense against data exfiltration.
The transition to this secure model also involved the adoption of rigorous auditing and monitoring tools. Security professionals implemented real-time logging of all agent actions, allowing them to trace every file modification and network request back to a specific AI session. This visibility transformed the “black box” of AI behavior into a transparent and accountable process. As organizations moved forward, they embraced a culture of continuous security validation, where agents were regularly tested against new prompt injection techniques. This proactive stance ensured that the infrastructure remained resilient as the capabilities of autonomous AI continued to advance at a rapid pace.