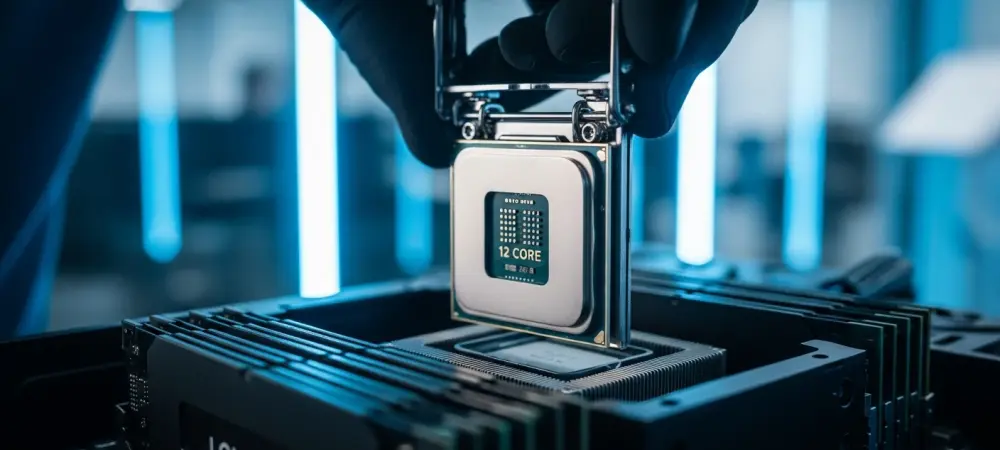
The silicon landscape shifted unexpectedly when a rare industrial processor found its way into a high-end consumer gaming rig through sheer technical persistence. While Intel designed the Bartlett Lake Core 9 273PQE for embedded systems and rugged hardware, a modder known as Kryptonfly successfully bridged the gap, booting this 12-core powerhouse on a consumer-grade Asus Z790 motherboard. This achievement marked a significant milestone in community-driven hardware exploitation, proving that the boundaries between enterprise and consumer hardware are often thinner than BIOS restrictions suggest.
The Significance of the Bartlett Lake Architecture
Understanding the buzz surrounding this mod required a look at the current shift in CPU design. While modern consumer chips favor a performance and efficiency hybrid model, many enthusiasts still crave the raw, uninterrupted power of a pure P-core configuration. Bartlett Lake offered exactly that—a 12-core, 24-thread layout that prioritized high-performance throughput without the scheduling complexities sometimes introduced by E-cores.
As the LGA1700 socket neared the end of its traditional lifecycle, finding new ways to utilize exotic silicon provided a vital path for extending the longevity of existing Z790 setups. This specific architecture bypassed the hybrid overhead, appealing to users who demanded consistent latency and predictable thread behavior for specialized workloads or high-frame-rate gaming.
Overcoming Hardware Incompatibility and Firmware Barriers
The journey from a “5F” hang code to a stable Windows desktop involved sophisticated firmware manipulation and technical problem-solving. Initial attempts to pair the Core 9 273PQE with consumer boards resulted in critical system agent initialization errors, as the motherboard’s stock BIOS did not recognize the embedded chip’s unique ID. To circumvent this, the modder utilized custom BIOS patches to trick the motherboard into executing a Raptor Lake startup sequence.
This software-level camouflage allowed the system to bypass POST errors and successfully load the operating system. Diagnostic tools like Aida64 eventually recognized the 12-core architecture, confirming that the microcode adjustments were effective. However, the process highlighted the fragility of such setups, as the hardware initially struggled to maintain communication between the CPU and the board’s peripheral controllers.
Lessons from the Legacy of Community Hardware Modding
This project drew direct parallels to historical community efforts where builders ported high-end mobile or enterprise CPUs to older consumer sockets through microcode adjustments. By leveraging firsthand experience with BIOS editing, Kryptonfly demonstrated that hardware limitations were often artificial rather than physical. This breakthrough reinforced the value of community research, showing that specialized industrial chips could find a second life in enthusiast machines.
Moreover, the success of this mod served as a reminder that the enthusiast community remains a vital force in hardware longevity. By refusing to accept manufacturer-imposed limitations, independent developers continued to uncover hidden potential within existing platforms. These efforts often paved the way for more accessible tools that allowed less technical users to eventually benefit from similar hardware cross-compatibility.
Potential Strategies for Exploring Non-Consumer Hardware
For hardware enthusiasts looking to follow this development, the process highlighted several critical areas for technical focus. Success in these “forbidden” hardware pairings relied on identifying compatible microcode versions and understanding how to patch BIOS files without compromising system integrity. Future efforts would need to address lingering stability issues, such as USB driver errors and power delivery optimization, to ensure that the 12 P-core performance was fully realized.
As benchmark results emerge, the community will gain a clearer framework for determining which embedded chips offer the best price-to-performance ratio. Moving forward, enthusiasts should prioritize documentation of power stages and voltage regulator compatibility to prevent hardware damage. This exploration opened the door for a more modular approach to the LGA1700 platform, suggesting that the most powerful upgrades might not always come from a retail box.