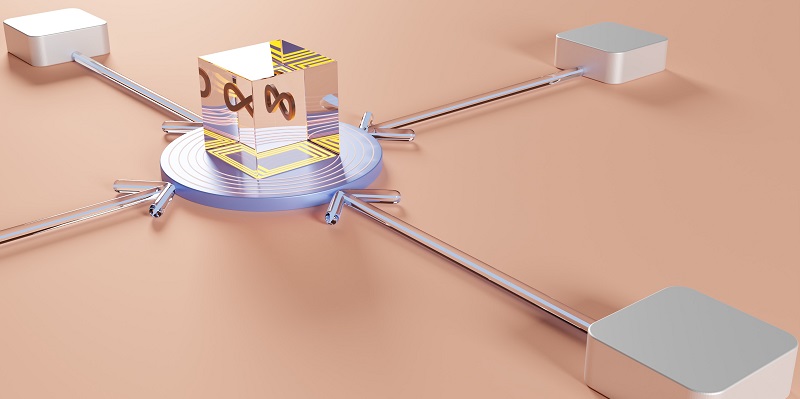
In today’s rapidly evolving technological landscape, organizations are constantly seeking ways to optimize their software development processes. This is where DevOps comes into play. DevOps is a set of practices and cultural philosophies that aim to streamline the collaboration between development and operations teams throughout the software development lifecycle (SDLC). A crucial aspect of DevOps is the implementation of an efficient pipeline that enables smooth flow and integration of code from development to deployment.
The importance of version control systems for code collaboration and management
The first step in the DevOps pipeline is to store the development code on a version control system (VCS) where the development team can collaborate on the code and manage different versions of the development. A VCS not only provides a central repository for the code but also ensures version control, enabling developers to track changes, revert to previous versions if needed, and work concurrently without conflicts.
Understanding Jenkins as an open-source DevOps tool for continuous integration
Jenkins is one such open-source DevOps tool used for continuous integration. Continuous Integration (CI) is a practice that involves merging code changes into a central repository frequently. Jenkins automates this process by continuously building, testing, and integrating code changes, enabling developers to identify and resolve integration issues early on. With Jenkins, developers can monitor the progress of builds, run tests automatically, and receive immediate feedback on the status of the code.
The role of testing in the software development life cycle (SDLC) for meeting real-world requirements
Testing plays a crucial role in the entire SDLC (Software Development Life Cycle) to ensure that what is built meets the real-world requirements. DevOps promotes the integration of testing at every stage of the pipeline, from unit testing to system testing and beyond. By automating tests and integrating them into the pipeline, organizations can identify bugs and issues early, ensuring a high-quality end product. Testing frameworks such as Selenium and JUnit are commonly used in DevOps practices to streamline the testing process.
Exploring continuous deployment and its benefits in simplifying code deployment to remote servers
Continuous deployment involves deploying code to remote servers without complications. By automating the deployment process, organizations can release new features and updates quickly and efficiently. Continuous deployment tools like Docker and Kubernetes provide containerization capabilities that ensure consistency and portability of applications across different environments. This not only simplifies deployment but also reduces the risk of compatibility issues.
An overview of Ansible and its capabilities for configuration management, software provisioning, and deployment
Ansible is open-source software that provides configuration management, software provisioning, and deployment capabilities. It allows for the automation of infrastructure setup and application deployment, making it easier for DevOps teams to manage complex environments. With Ansible, organizations can define infrastructure as code, enabling consistent and repeatable deployments. Ansible’s agentless architecture ensures easy setup and maintenance.
The significance of continuous feedback in capturing user experiences and driving future improvements
Continuous feedback involves capturing the user experiences and insights of the application to strategize future actions and improvements. This feedback can come from various sources, including user surveys, analytics data, and support tickets. By actively gathering and analyzing feedback, organizations can identify pain points, address usability issues, and prioritize feature enhancements to ensure a seamless user experience.
The importance of continuous monitoring in assessing compliance and security issues
Continuous monitoring is crucial for assessing compliance issues and security threats in applications. Monitoring tools like Nagios and Splunk provide real-time visibility into the performance, availability, and security of applications and infrastructure. By actively monitoring key metrics and logs, organizations can detect and mitigate issues before they impact end-users, ensuring the reliability and security of their applications.
Challenges and strategies in keeping applications running smoothly after successful deployment
After successfully configuring the production environment and deploying the application, the main challenge is to keep the application running smoothly without any issues. This involves proactive monitoring, capacity planning, and disaster recovery strategies to ensure high availability and minimal downtime. Automated scaling and load-balancing techniques can also help manage increased traffic and maintain optimal performance.
The significance of maintenance is to ensure the smooth functioning of the application despite updates and patches
Maintenance is a major part of continuous operations, ensuring that recent releases, patches, and updates do not impact the current deployment. Regular maintenance activities include applying security patches, updating dependencies, and monitoring system health. By prioritizing maintenance tasks and adopting a proactive approach, organizations can minimize disruptions to the application and reduce the risk of vulnerabilities.
The benefits of adopting DevOps in delivering products at a faster pace
Adopting DevOps enables organizations to deliver their products at a faster pace. By automating key processes, eliminating manual bottlenecks, and fostering cross-team collaboration, DevOps practices create efficiencies that accelerate software development and deployment cycles. This not only increases the speed of product delivery but also enhances overall productivity, innovation, and customer satisfaction.
In conclusion, the DevOps pipeline provides a systematic approach to streamline software development, from code collaboration and continuous integration to testing, deployment, feedback, and monitoring. By adopting DevOps principles and leveraging relevant tools, organizations can achieve faster and more efficient software delivery while ensuring high-quality and reliable applications. The key lies in embracing a culture of collaboration, automation, and continuous improvement throughout the entire software development lifecycle.